SecureAuth Connect Platform Overview
SecureAuth Connect is a modern, cloud-native identity and access management (IAM) platform that provides secure, easy access for Customer IAM (CIAM), Workforce IAM, and Partner IAM use cases. It combines passwordless login, ongoing security monitoring, risk assessment, and identity management in one platform.
SecureAuth Connect Platform is designed for comprehensive identity and access management across a wide range of use cases — from consumers to workforce, partners, and even emerging AI-driven agents.
-
Customer IAM (CIAM): Deliver secure, scalable management of customer identities with frictionless onboarding, progressive profiling, and adaptive authentication — improving user trust, retention, and loyalty.
-
Workforce IAM: Protect employee and contractor access with passwordless login, continuous authentication, and endpoint trust enforcement to secure hybrid work environments.
-
Partner IAM: Simplify collaboration with vendors, suppliers, and resellers through role-based and policy-driven access that adapts to partner hierarchies and external identity providers.
-
B2B IAM: Enable secure, multi-tenant identity management for business customers and sub-organizations, offering delegated administration, organization-scoped policies, and isolated analytics for each tenant.
-
Agentic AI IAM: Manage access for AI agents and machine-to-machine identities, supporting autonomous workflows, delegated consent, and policy-based authorization for actions performed on behalf of users.
Business benefits
SecureAuth Connect delivers measurable business outcomes across revenue growth, operational efficiency, and risk reduction. By unifying authentication, authorization, and risk intelligence under a single platform, organizations gain both stronger security and smoother user experiences.
-
Accelerate Revenue: Speed up user onboarding and boost customer conversion through frictionless, passwordless, and omnichannel login experiences. Enable faster access for workforce and partners, reducing time-to-value for every identity.
-
Reduce Cost: Simplify identity operations with centralized policy management and flexible configuration that scale across brands, business units, or customer types—without costly customization or surge pricing. Cut IT support overhead and eliminate manual user management.
-
Stay Secure: Safeguard every login, API, and transaction using adaptive risk intelligence, device trust, and fine-grained authorization. Continuously assess session risk to stop threats before they reach critical systems.
-
Prevent Breaches: Eliminate credential theft and unauthorized access with phishing-resistant FIDO2 authentication, contextual MFA, and dynamic policy enforcement that responds instantly to anomalies.
-
Increase User Satisfaction: Deliver a seamless, frustration-free experience with passwordless authentication, smart step-up prompts, and consistent access journeys across web, mobile, and shared devices.
Key solutions
SecureAuth IAM provides comprehensive identity and access management features. These include passwordless authentication, risk assessment, access control, and multi-brand identity support to meet enterprise security needs.
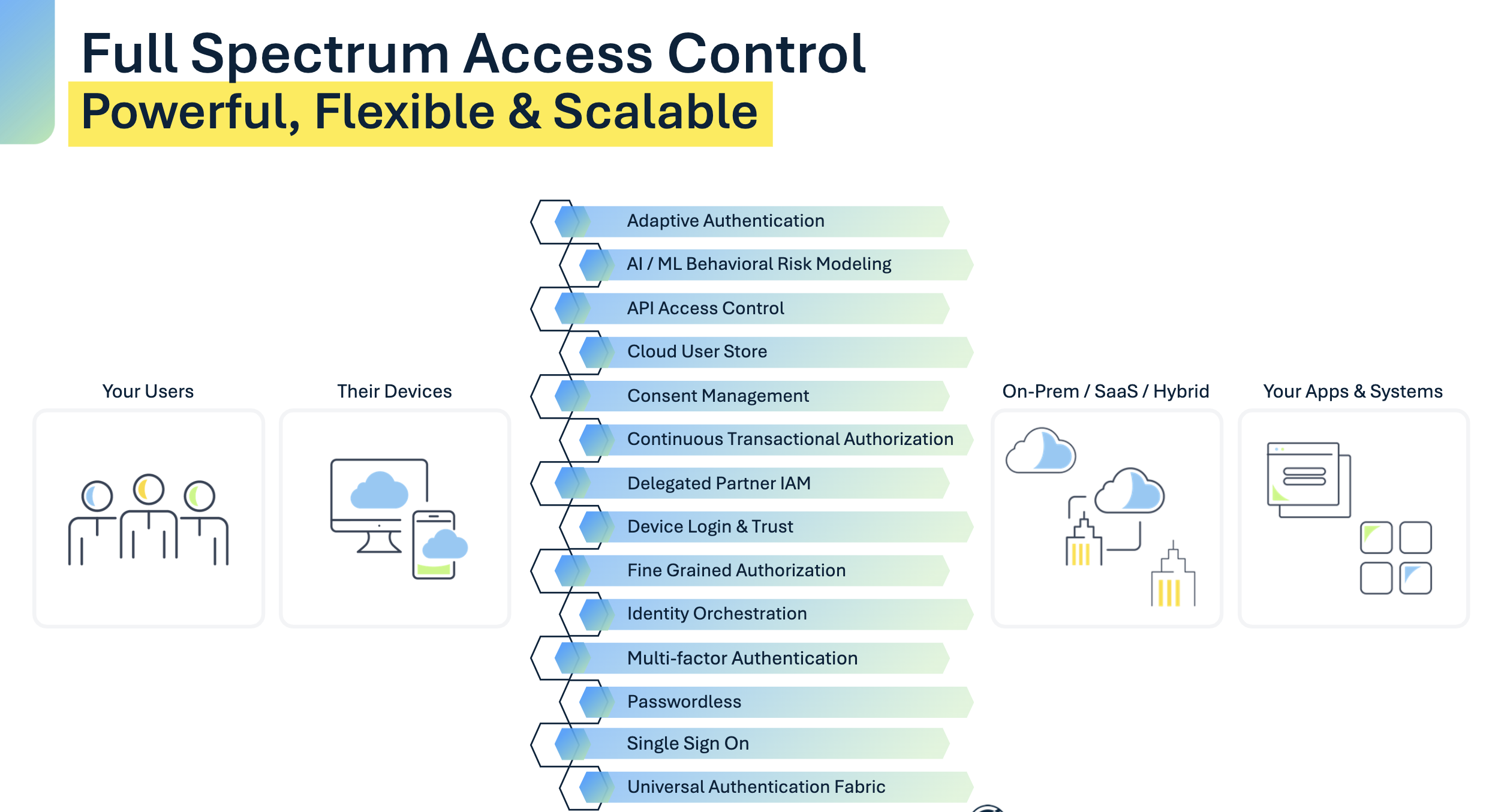
SecureAuth Connect Platform scales automatically and integrates with your existing systems. Key features include:
- Independent operation for different business units
- Works with existing systems using industry standards (OAuth, OpenID Connect, SAML, SCIM)
- High availability with global performance
SecureAuth IAM delivers a powerful, flexible, and secure IAM platform designed to address the evolving identity needs of modern enterprises.
Customer Identity and Access Management (CIAM)
Onboarding, progressive profiling, social sign‑in, consent, multi‑brand UX, frictionless authentication experiences.
Workforce Identity and Access Management
Passwordless workforce access, SSO, adaptive MFA, device trust, risk based ML models, session assurance.
B2B Identity Management and Delegated Administration
Org and sub‑org hierarchy, delegated admin, customer org autonomy, auditability for B2B and B2B2C SaaS providers.
Multi‑Brand and Multi‑Tenant Experiences
Multi brand experience within single platform for branding, UX variants, org separation, onboarding, user authentication.
Agentic AI Authorization and Access Control
Non‑human identities, authorization token patterns and profiles, least‑privilege scopes, auditable actions, token exchange.
Enterprise Passwordless and Passkey Management
FIDO2 cerified provider, passkeys with recovery, device binding, policy control, and audit trails.
Device Trust for Workforce
Protect employee device access and assets with passwordless and ML driven access models, endpoints, VDIs, device binding.
Continuous Session Assurance (Facial Liveness)
Keep sessions trusted post-login with risk-triggered liveness and face match to verify the right person is still in the seat
Fine‑Grained Authorization for SaaS Platforms
Policy and Attribute-based access control (PBAC/ABAC), FGA/ReBAC for resource action level permissions and entitlements.
Protect APIs with OAuth 2.1 and OpenID Connect
AuthZ server, scopes, token lifecycles, token exchange, PKCE, PAR.
Open Banking and FAPI‑Compliant API Security
FAPI 2.0 (Baseline/Advanced), PAR, JAR/JARM, mTLS, DPoP, consented data sharing, SSA, DCR, RAR.
Fraud Prevention: Account TakeOver Protection
Eliminate Account take over fraduluent attempts, unauthorized access to maintain brand trust and loyalty
Fraud Prevention: Transaction Protection
Protect transactions by evaluating risk in real time and requiring step-up verification when needed
Fraud Prevention: Compromised Credential Protection
Integrates breach intelligence feeds to detect and block known-compromised credentials before they can be used
Fraud Prevention: Account Sharing and License Abuse Detection
Identifies use of shared credentials locations, devices, patterns to enforce revenue and compliance actions.
Key capabilities
SecureAuth IAM provides comprehensive identity and access management features. These include passwordless authentication, risk assessment, access control, and multi-brand identity support to meet enterprise security needs.
SecureAuth Connect Platform scales automatically and integrates with your existing systems. Key features include:
- Independent operation for different business units
- Works with existing systems using industry standards (OAuth, OpenID Connect, SAML, SCIM)
- High availability with global performance
SecureAuth IAM delivers a powerful, flexible, and secure IAM platform designed to address the evolving identity needs of modern enterprises.
Passwordless authentication
FIDO2 passkeys, biometrics, mobile push with device binding, and certificates.
Adaptive risk engine
Real-time risk scoring based on user behavior and device patterns.
Policy-based access control and FGA
Role-based and attribute-based access control with detailed permissions.
Open banking and open data (FAPI)
Secure financial data sharing with dynamic registration and user consent.
Agentic AI and A2A access control
Non-human identities and application-to-application access with secure token exchange, minimal permissions, and audit trails.
Device trust and endpoint protection
Enforce compliant devices; extend passwordless to workstations/endpoints.
Continuous session assurance
Ongoing validation of active user sessions using biometrics, behavior, and device data.
Multi-workspace delegated authorization
Isolated workspaces with local policy control under centralized governance.
Multi-brand and B2B SaaS identity
Organizations, sub-organizations, identity pools, and delegated administration.
Enterprise passkey provider
Centralized passkey management, recovery, and consistent user experience.
Consent and data privacy
Purpose-based consent, progressive profiling, data retention, and user rights management.
Developer and Ops tooling
APIs and SDKs, webhooks and events, infrastructure-friendly configuration, audit trails, and dashboards.
Deployment models
Whether you need global SaaS, a dedicated single-tenant environment, customer-managed deployment, or fully air-gapped operation, SecureAuth offers deployment flexibility without sacrificing performance, security, or manageability.
Cloud-native SaaS
99.99% SLAGlobal, resilient SaaS with guaranteed uptime and continuous updates.
Private single-tenant SaaS
Dedicated EnvironmentIsolated SaaS instance with full tenant-level segregation and custom SLAs.
Customer deployed
K8s / On-Prem ReadyDeploy in customer-managed environments, on-premises or in Kubernetes.
Air-gapped
Offline ModeOperate in isolated environments with no external connectivity, ensuring maximum data sovereignty.
Hybrid identity
Best of Both WorldsCombine SaaS federation with local identity for optimal flexibility.
Security and compliance
The SecureAuth platform is SOC 2 Type II and ISO 27001 certified, operating under rigorous security controls, continuous monitoring, and well-established privacy practices to help organizations meet regulatory and compliance obligations.
SOC 2 Type II
Independent AuditControls for security, availability, and confidentiality validated over time.
ISO/IEC 27001
Certified ISMSFormal information security management system with continuous improvement.
Trust and transparency
Reports on RequestSecurity documentation, pen test summaries, and reports available from our SOC team.
