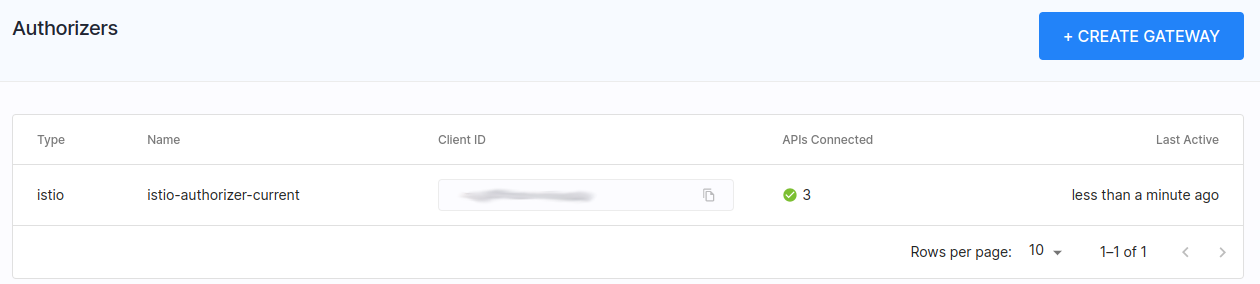
How the SecureAuth Risk Engine Prevents Account Takeovers (ATO)
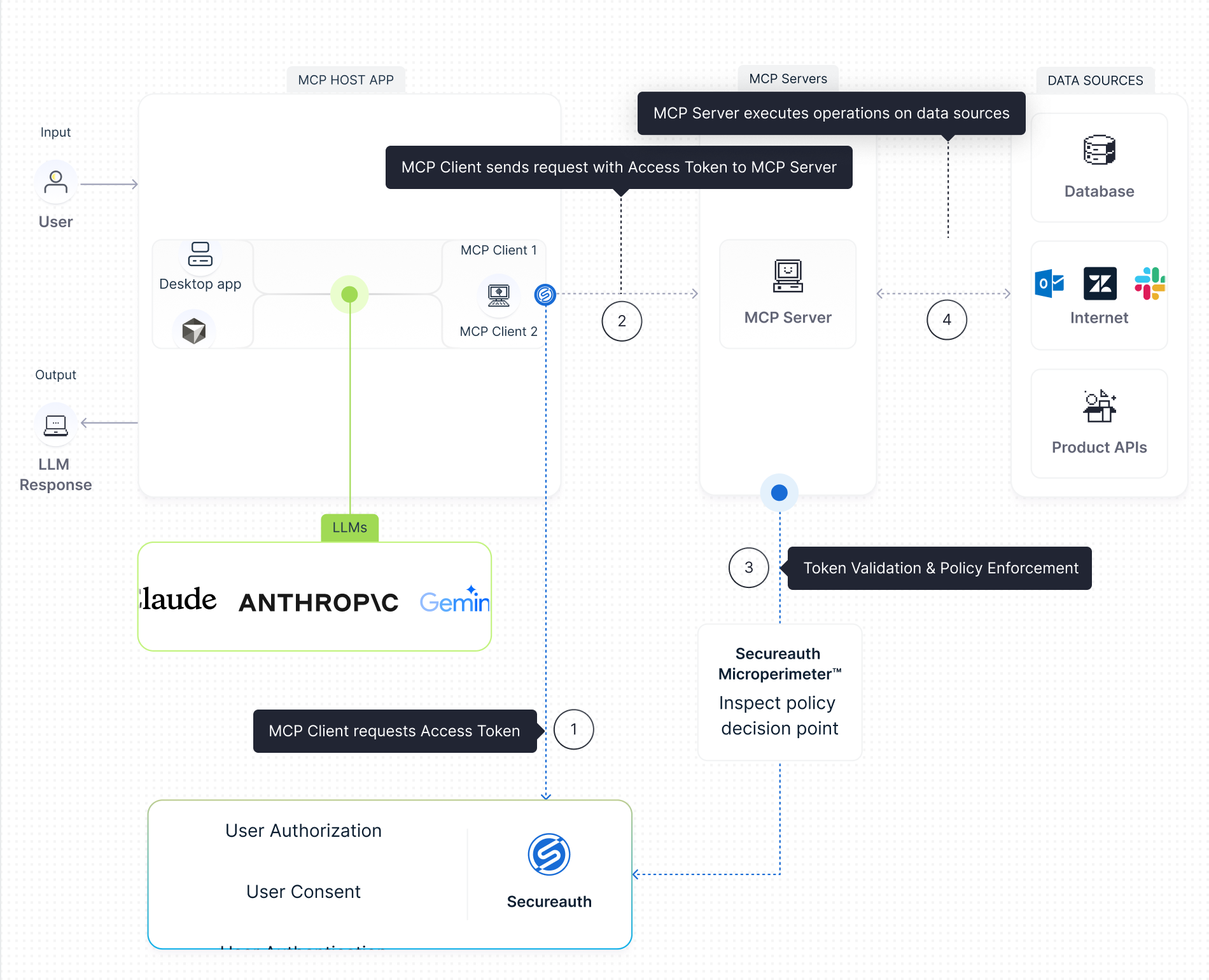
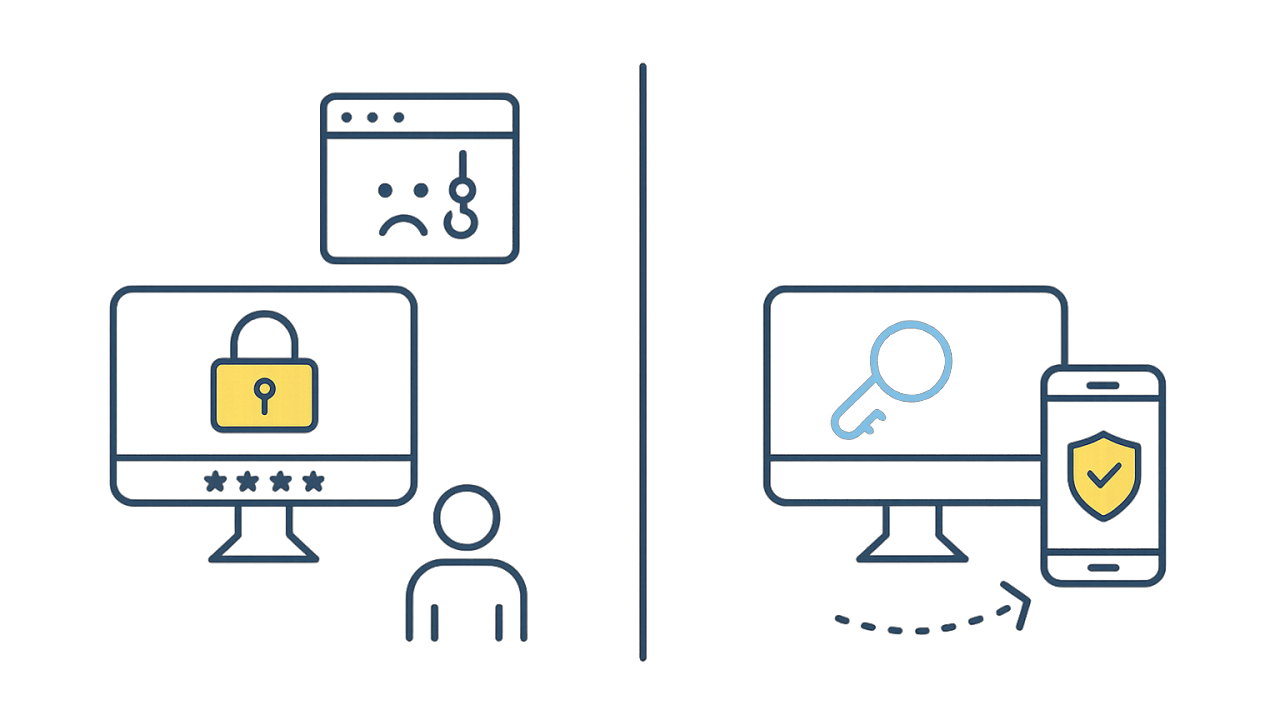
Learn how the SecureAuth Risk Engine uses contextual analysis, machine learning models, and behavioral signals to detect and prevent account takeover attacks even when credentials are valid.