Configure SSO for administrators
The SecureAuth CIAM platform lets you set up and connect different authentication methods to make user access secure and easy for modern SaaS applications.
Choose from built-in options like passwords, verification codes, and passwordless methods, or connect to external services like Google Workspace, GitHub, and Microsoft Entra ID to match your security needs.
Before you begin
To configure SSO for administrators, you need:
- Workspace access: Administrator permissions in your target workspace
- Authentication strategy: Decide which authentication methods to enable
- Session requirements: Determine appropriate session timeouts for your security needs
Part 1: Set up authentication methods
Before configuring SSO, you need to create an Identity Pool in the SecureAuth platform.
Create identity pool
-
In the target workspace, go to Authentication > Providers.
-
On the Identity Providers page, click Create Connection.
-
On the Create Connection page, select Identity Pool and click Next.
-
On the Connect Identity Provider page, click Create Pool.
-
Complete the required fields:
- Name: Descriptive name for the identity pool
- Description: Purpose and scope of the pool
- Tag Color: Visual identifier for the pool
Configure sign-in methods
-
Expand the Sign-in section.
-
Configure the authentication methods:
First-factor authentication methods
Choose the primary authentication method for user login:
Password
Traditional login with username and password.
Verification Code
Send a one-time verification code by email or SMS to the user.
Authenticator App
Send a time-based one-time passcode (TOTP) to the user's mobile authenticator app.
Passkey
Secure, passwordless authentication using FIDO2 devices like YubiKey or Touch ID. Users authenticate with physical or biometric keys instead of traditional passwords.
Second-factor authentication methods
Optionally enable an additional authentication method for enhanced security.
Additional settings
| Setting | Description |
|---|---|
| Reduce 2FA verification on same device | Remember the device for a set time, avoiding repeated 2FA prompts. Adjust the time or disable by setting to 0 seconds. |
| Sign-in identifier settings | Check this box to ignore case sensitivity in email and username during user login. |
Configure sign-up options
-
Expand the Sign-up section.
-
Select the registration mode:
Self Registration
Allow users to self-register and manage their profile details.
Admin Initiated Registration
Administrator creates user accounts and sends invitation emails to users.
Part 2: Enable SSO
Activate persistent sessions
-
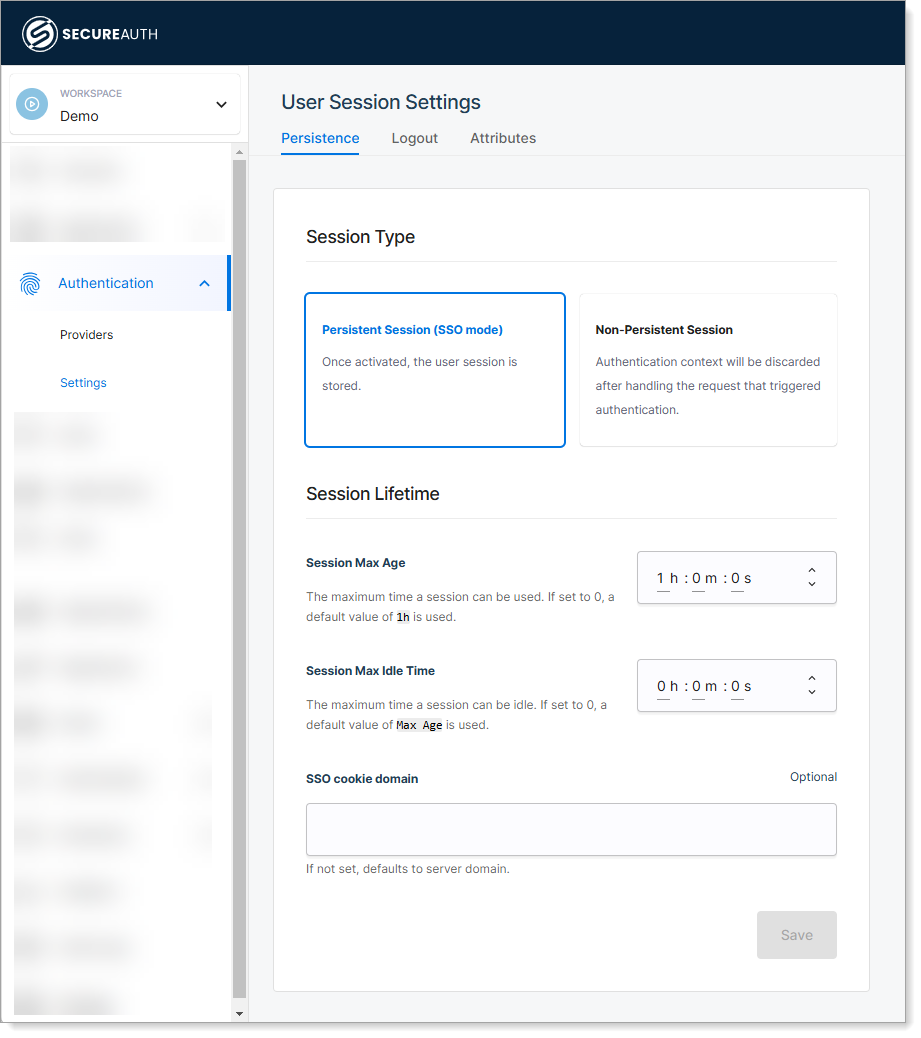
In the target workspace, go to Authentication > Settings > Persistence.
-
Select the Persistent Session (SSO mode) option.
Configure session settings
In the Session Lifetime section, configure the following settings:
| Setting | Description | Recommended Value |
|---|---|---|
| Session Max Age | Time after which a user's session expires, requiring reauthentication | 8 hours for standard security |
| Session Max Idle Time | Time after which an inactive session expires, requiring reauthentication | 30 minutes for high security |
| SSO Cookie Domain | Domain for the SSO cookie of logged-in users. If empty, uses the authorization server's domain | Leave empty unless using custom domains |
| Allowed Logout Redirect Domains | Domains where applications can redirect users after logout. Valid only with redirect_to parameter | Add your application domains |
| Post-Logout Redirect URL | Default URL to redirect users after logout when no redirect_to parameter is provided | Your organization's homepage |
- Shorter sessions: Better security but more frequent logins
- Longer sessions: Better user experience but increased security risk
- Idle timeouts: Automatically protect against unattended sessions
Verify SSO configuration
After completing the setup:
-
Test authentication: Log in using your configured authentication methods
-
Verify SSO behavior:
- Log into one application
- Access another application in the same workspace
- Confirm you're not prompted to authenticate again
-
Test session timeout: Wait for the configured idle time and verify the session expires
Expected result: After logging into an application through SecureAuth, users can access all workspace applications without reauthenticating, as long as the session remains valid.
Authentication method comparison
| Method | Security Level | User Experience | Best For |
|---|---|---|---|
| Password | Medium | Familiar | Standard business apps |
| Verification Code | High | Moderate friction | Sensitive applications |
| Authenticator App | High | Low friction after setup | Tech-savvy users |
| Passkey | Very High | Excellent | Modern organizations |
Troubleshooting
Common issues
| Issue | Cause | Solution |
|---|---|---|
| SSO not working between apps | Persistent session not enabled | Verify Persistent Session (SSO mode) is selected |
| Sessions expiring too quickly | Session timeout too low | Increase Session Max Age or Session Max Idle Time |
| Users can't register | Registration mode mismatch | Check Sign-up section configuration |
| 2FA prompts on every login | Device memory disabled | Increase Reduce 2FA verification time setting |
Security best practices
- Use multi-factor authentication for administrator accounts
- Set appropriate session timeouts based on your security requirements
- Regularly review authentication logs and session activity
- Enable device memory for trusted devices to reduce friction
- Test SSO configuration thoroughly before rolling out to users