Add server-side web application
A server-side web application runs on a backend server — Node.js, Java, and .NET are common examples. An online banking portal or e-commerce account dashboard are typical use cases: the server fetches data, renders the page, and returns it to the browser. Unlike a browser-based application, the code runs on the server where it is not publicly visible.
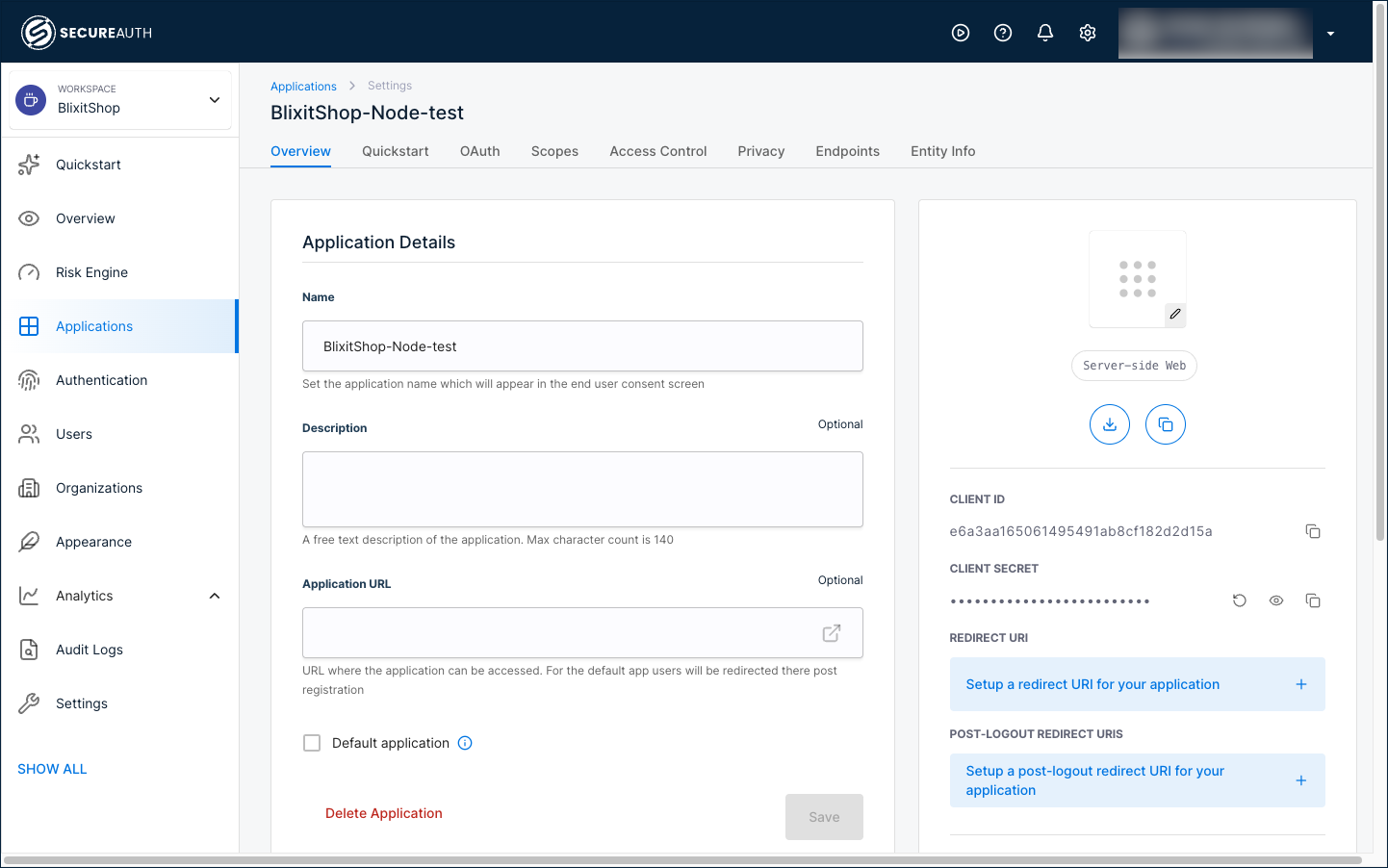
Because the server can safely store secrets, SecureAuth registers these applications with both a Client ID and a Client Secret. The secret authenticates your server during sign-in. Treat it like a password: do not include it in client-side code or commit it to a public repository.
Before you begin
You'll need:
- Access to your workspace in SecureAuth
- The redirect URI where users should land after signing in (your application's callback URL)
- Access to your application's server configuration
Add the application
-
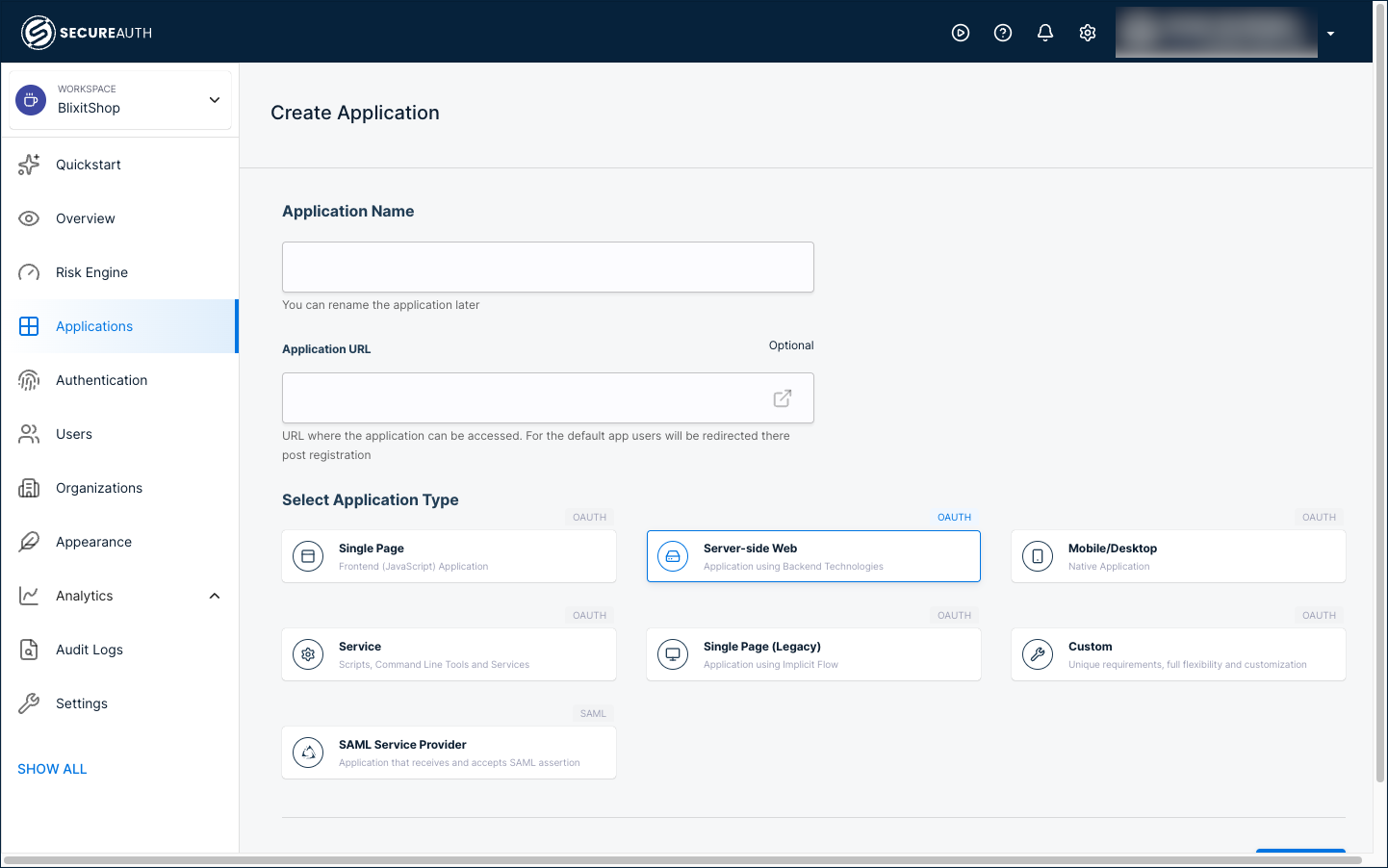
In your workspace, select Applications > Clients > Create client.
-
Enter a name for your application, select Server-side Web, and click Create.
-
In the right panel, click + Setup a redirect URI and enter your application's callback URL.
The redirect URI is the URL where SecureAuth sends users after they sign in. This must match the callback URL in your application code.
-
Copy the Client ID and Client Secret from the right panel. You'll need both when configuring your application code.
Integrate with your application
After creating the client in SecureAuth, use the Quickstart tab to get framework-specific integration code pre-filled with your application's configuration.
Open the Quickstart tab guide for step-by-step instructions, code snippets for .NET, Java, and Node.js, and a link to clone a full working example.
Test the integration
- Start your application server.
- Navigate to the login page.
- Verify that users are redirected to SecureAuth for authentication.
- After signing in, confirm users are redirected back to your application.
Next steps
- Restrict access with user policies to control who can use the application
- Set up single sign-on (SSO) by connecting external identity providers
- Skip the consent screen for your own applications
- Enable passwordless authentication for a better user experience