SMS OTP
SecureAuth Connect SMS OTP delivers one-time password (OTP) verification codes to users by text message, using Twilio as the delivery channel. When a user selects SMS during authentication, SecureAuth Connect sends a text message containing the verification code to their registered phone number.
Use cases
SMS OTP fits when you need a phone-based factor that most users can receive without installing an app.
- Broad device support: Almost every mobile phone can receive text messages, including older devices that do not support push notifications or authenticator apps.
- Quick onboarding: Users do not need to install anything or pair a device. If they have a phone number on file, SMS OTP works immediately.
- Step-up verification: Use SMS OTP as a second factor during sensitive actions like scope granting or account recovery, without requiring users to set up a dedicated authenticator.
- Fallback for email delivery issues: Some corporate email systems delay or filter OTP messages. SMS delivery bypasses that path.
SMS OTP is not the best fit when users are in regions with unreliable carrier delivery, when SIM-swap attacks are a concern for high-value accounts, or when cost per message is a constraint at very high volume.
How SMS OTP delivery works
When a user selects SMS as their OTP delivery method, SecureAuth Connect sends a text message to the user's registered phone number. The message contains the OTP code. The user enters the code on the verification screen in their browser.
SMS OTP uses the same phone number as Voice OTP. Users do not need to register a separate number for each delivery channel.
Use a Twilio phone number or messaging service that is verified and enabled for outbound SMS in your target regions. Check Twilio's geographic permissions to confirm Twilio can deliver messages to the countries where your users are located.
Prerequisites
- Tenant administrator access
- A Twilio account with a verified phone number or messaging service
Set up Twilio as SMS provider
Set up Twilio as the SMS provider for this channel. This does not affect your voice provider settings.
-
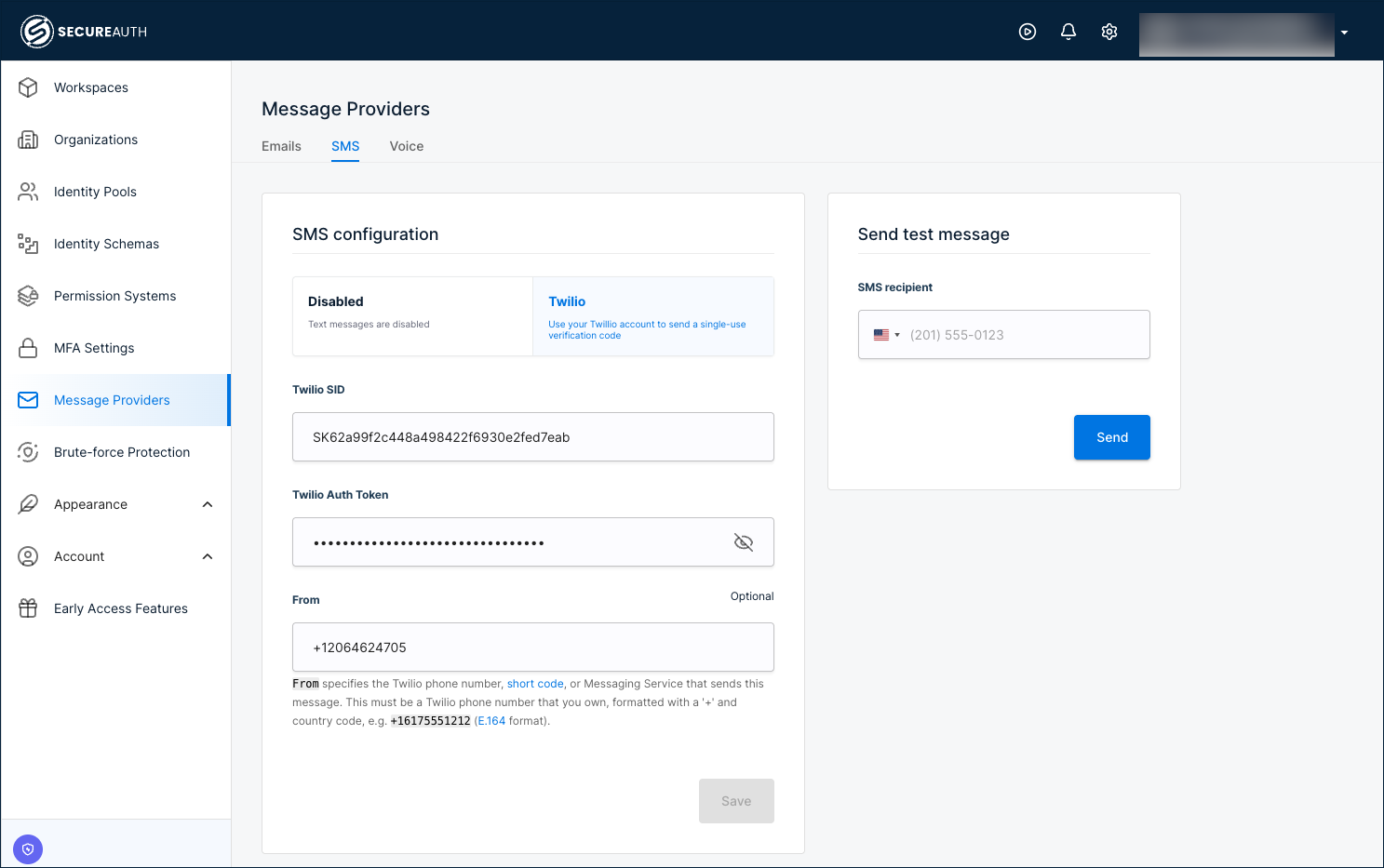
Go to Tenant Settings > Message Providers.
-
Select the SMS tab.
-
Select Twilio as the provider.
-
Enter the required Twilio settings:
Setting Description Twilio SID Your Twilio Account SID from the Twilio console. Twilio Auth Token The authentication token associated with your Twilio account. Do not share or expose this token. From The sender phone number, short code, or messaging service registered with Twilio. Format must follow E.164 standard (for example, +16175551212). -
Click Save.
Test your configuration
Use the built-in test option to verify SMS delivery:
-
Go to the Send test message section.
-
Enter a recipient phone number in E.164 format.
-
Click Send. You should receive a text message containing a test OTP code. Verify that the message arrives and the code displays correctly.
Set code length and lifetime
These are tenant settings and apply to all workspaces.
-
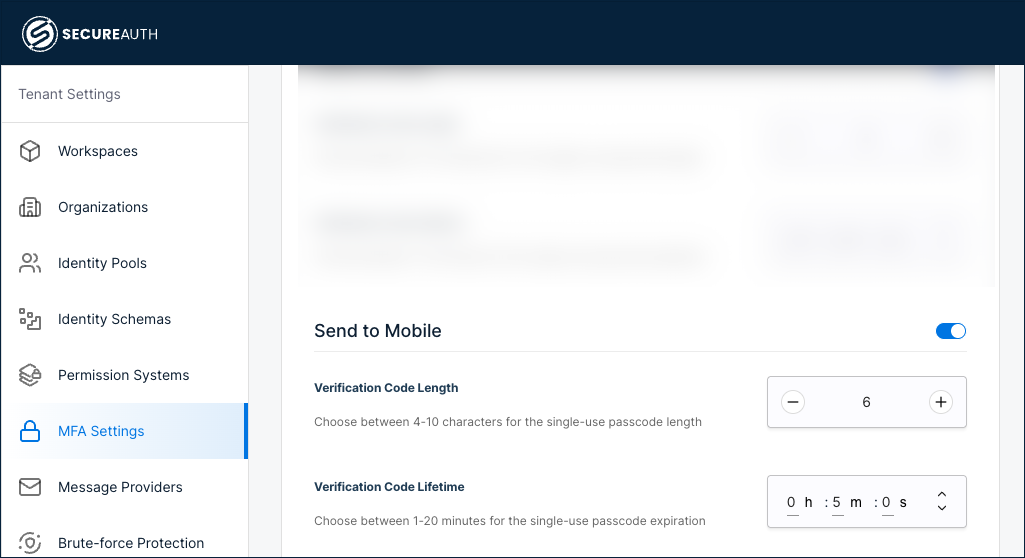
Go to Tenant Settings > MFA Settings.
-
Enable Send to Mobile (SMS).
-
Configure the verification code settings:
Setting Description Verification Code Length The number of digits in the code (for example, 6).Verification Code Lifetime How long the code remains valid (for example, 5minutes). -
Click Save.
Enable SMS OTP as an authentication method
After configuring the SMS provider, enable SMS OTP as an authentication method:
-
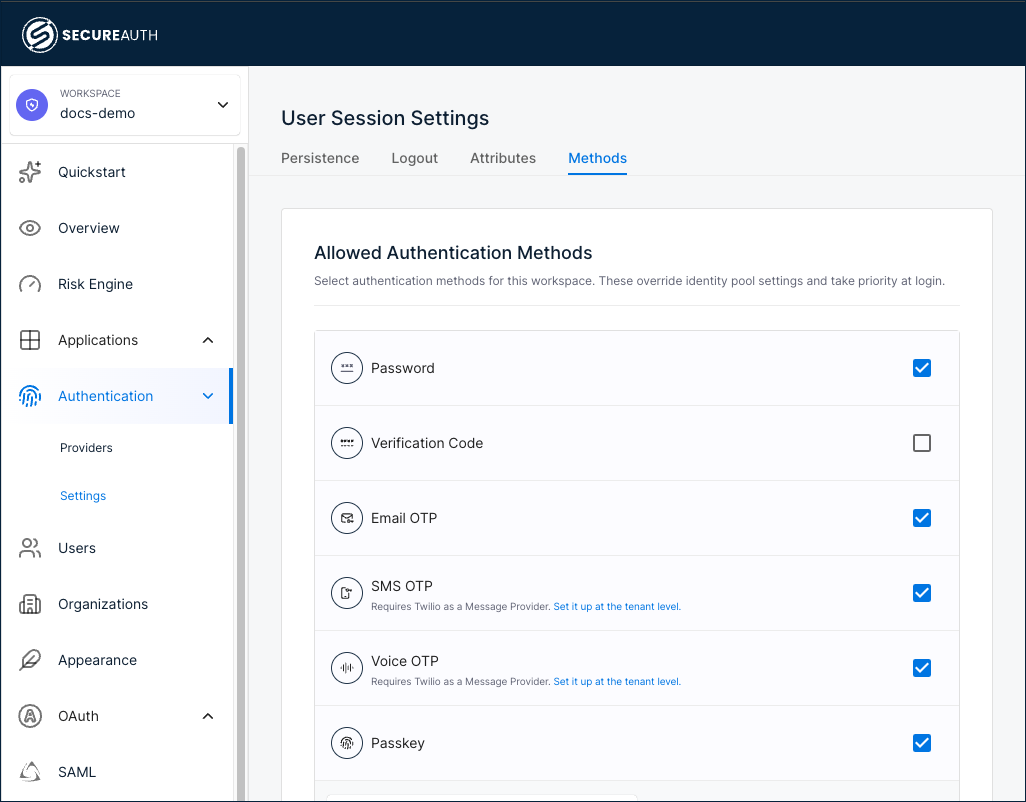
In your workspace, go to Authentication > Settings.
-
Select the Methods tab.
-
Select the SMS OTP check box.
-
Click Save.
If you have not set up the SMS provider yet, the Allowed Authentication Methods page shows a link under SMS OTP that takes you to the configuration page.
Add SMS OTP as a sign-in method
Add SMS OTP as a first-factor or second-factor authentication method for your users.
-
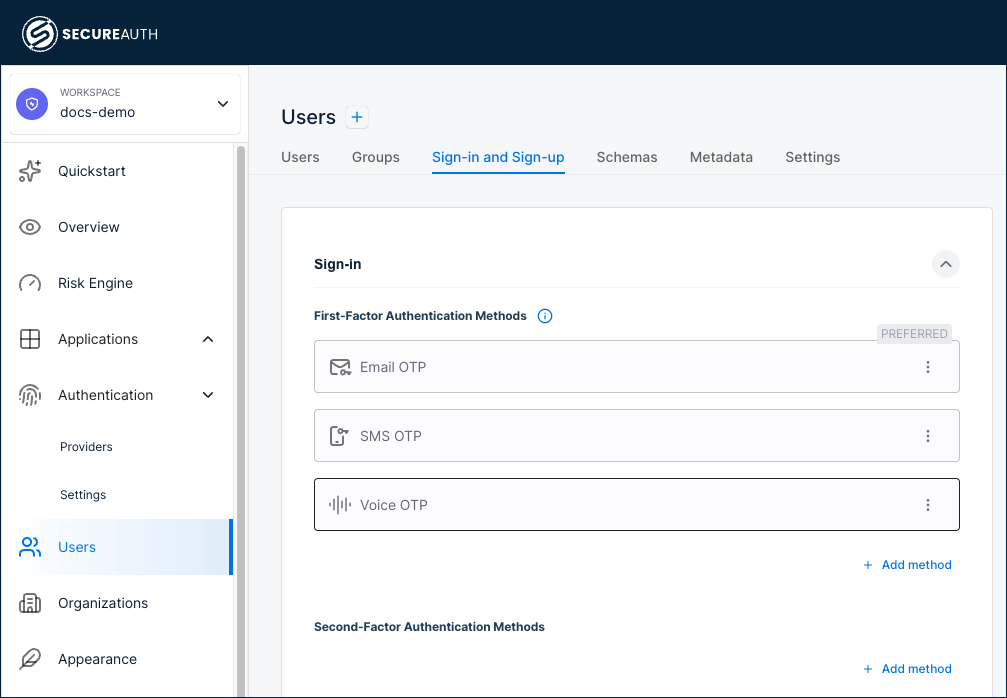
Go to Users > Sign-in and Sign-up.
-
Under First-Factor Authentication Methods or Second-Factor Authentication Methods, click + Add method and select SMS OTP.
-
(Optional) To make SMS OTP the preferred method shown at sign-in, click the three-dot menu and select Make Preferred. Only one method can be preferred per identity pool.
-
Click Save.
OTP rate limiting
SecureAuth Connect enforces rate limits on OTP send requests to prevent abuse. If a user or API client exceeds the allowed number of OTP requests within a time window, subsequent requests are temporarily blocked.