Azure Active Directory configuration
Use this guide to configure an Azure Active Directory (AD) to allow read and optional write access and connect with the SecureAuth® Identity Platform.
After you complete this configuration, you can then add an Azure AD data store in the Identity Platform.
Prerequisites
Identity Platform version 20.06
Azure AD and access to the Azure portal
Process
Step 1: Register the Identity Platform in Azure portal.
Step 2: Add API permissions in the Azure portal.
Step 3: Create a client secret in the Azure portal.
Step 4: Get the Azure AD connection settings; you will need this in the Identity Platform.
Step 1: Register the Identity Platform in Azure portal
To integrate Azure AD with the Identity Platform, you need to register the Identity Platform in the Azure portal.
Log in to your Azure Account through the Azure portal.
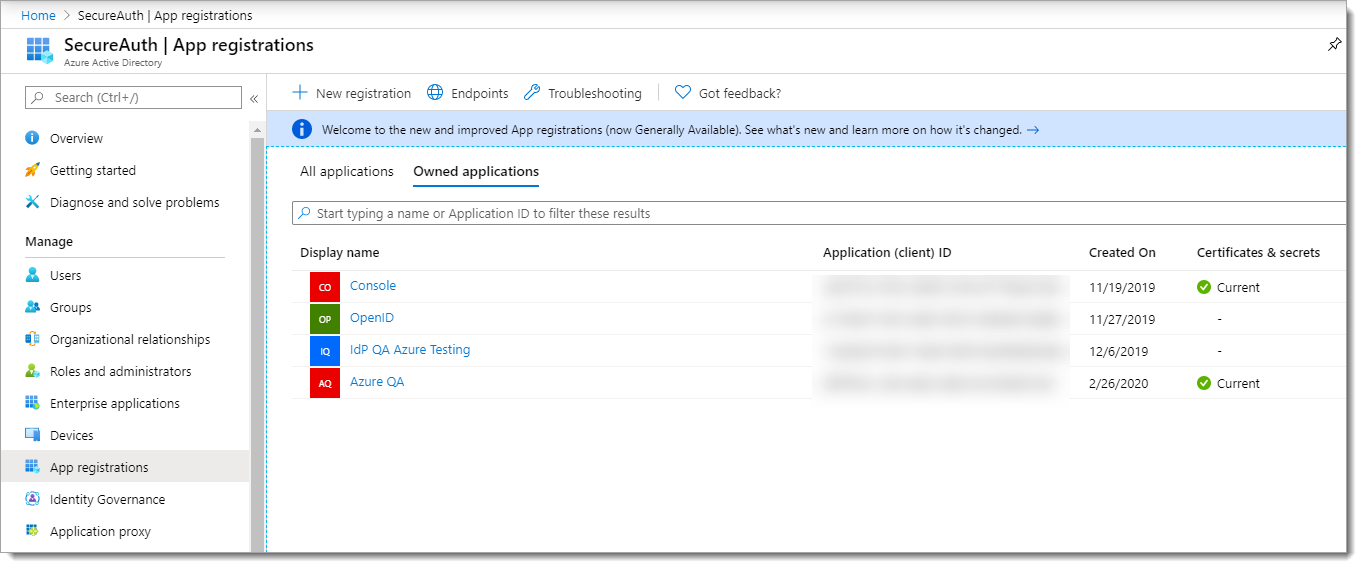
Select Azure Active Directory.
Select App registrations.
Select New registration.
Set a Name and keep the default Supported account types selection option to a single tenant.
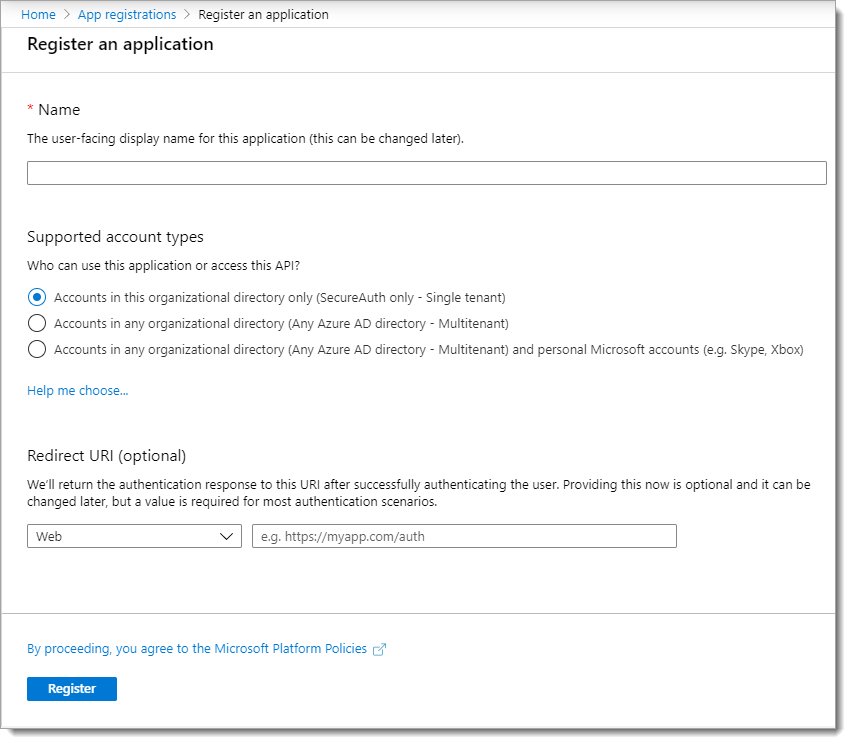
Click Register.
Step 2: Add API permissions
You will need to grant read and write permissions for the Identity Platform API calls to Azure AD.
From the App registrations list, click name of the registered app that you just created.
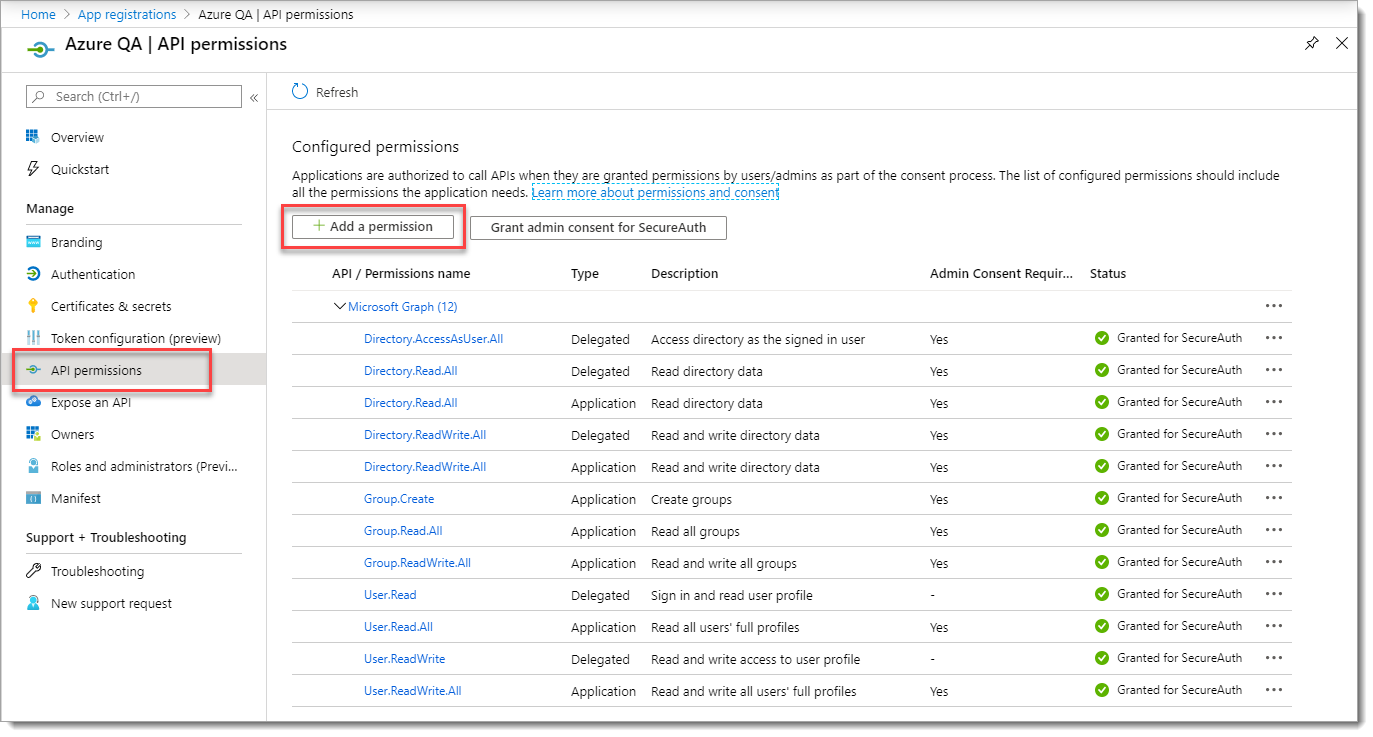
In the left pane, click API Permissions. Then, click Add a permission.
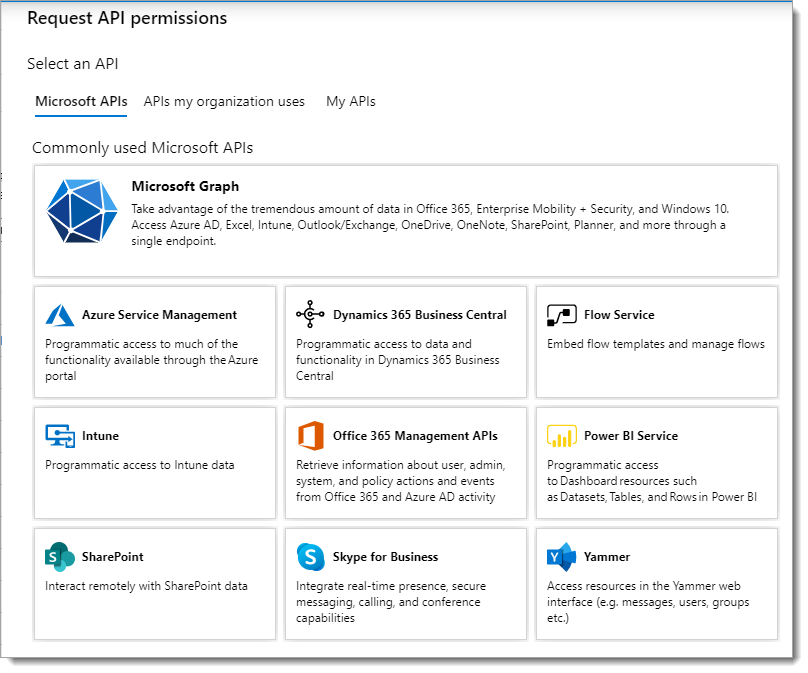
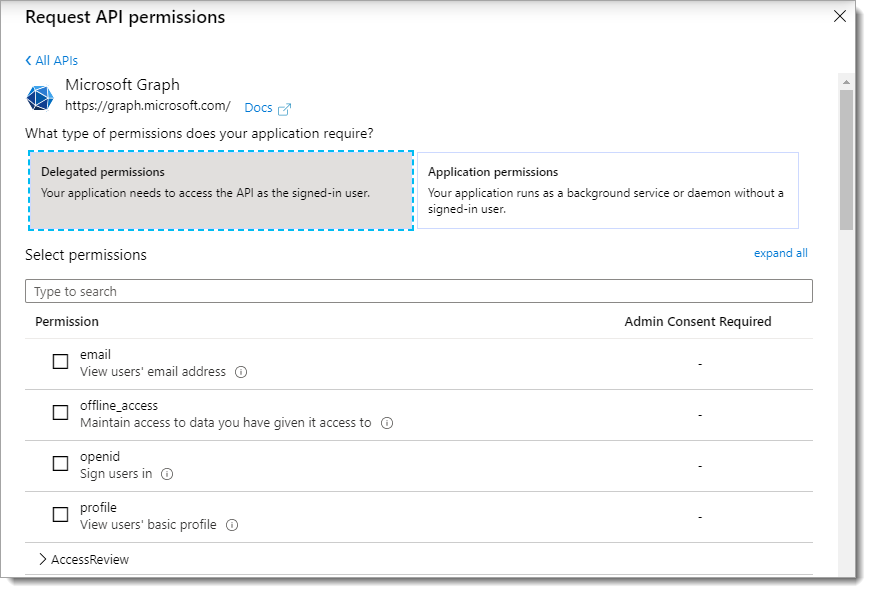
Select Microsoft Graph.
Click Delegated permissions. Then, scroll down to find and select the following check boxes:
Directory.AccessAsUser.All
Directory.Read.All
Directory.ReadWrite.All
User.Read
User.ReadWrite
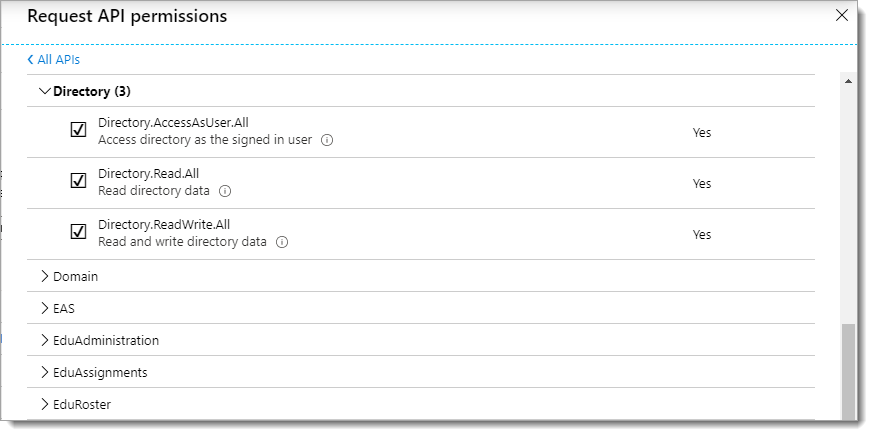
When you are done making your selections for delegated permissions, click Add permissions at the bottom of the page.
Click Application permissions. Then, scroll down to find and select the following check boxes.
Directory.Read.All
Directory.ReadWrite.All
Group.Create
Group.Read.All
Group.ReadWrite.All
User.Read.All
User.ReadWrite.All
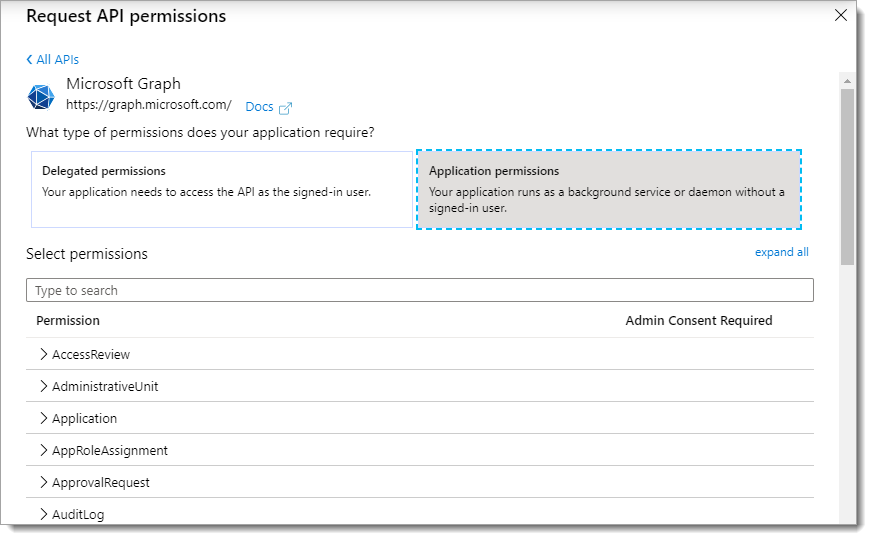
When you are done making your selections for application permissions, click Add permissions at the bottom of the page.
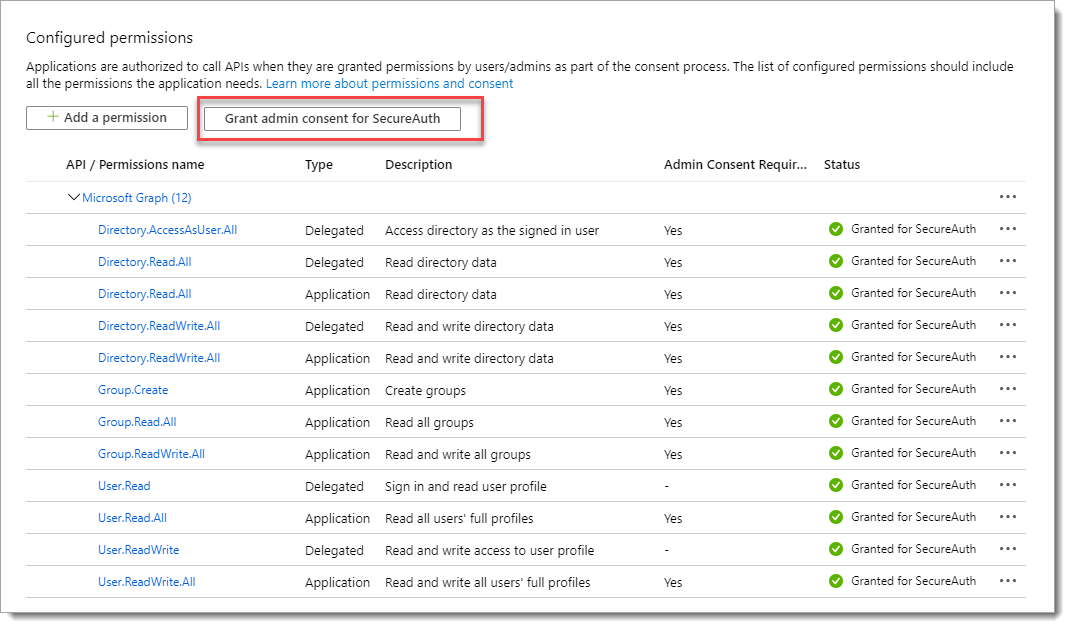
View and verify the list of configured permissions and click Grant admin consent.
Step 3: Create client secret
Create an application secret key so the Identity Platform can connect to Azure AD. You will need to copy and paste this client secret in the connection settings when you add the Azure AD data store in the Identity Platform.
From the left pane, click Certificates & secrets. Then, click New client secret.
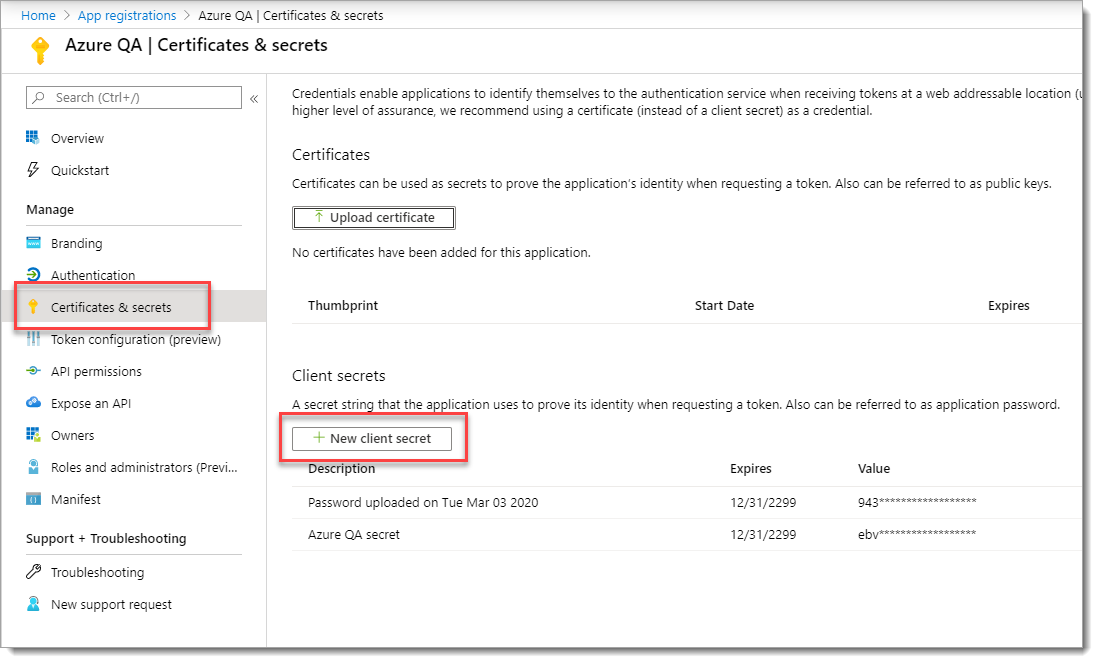
Add a description for the client secret and choose Never for the expiration.
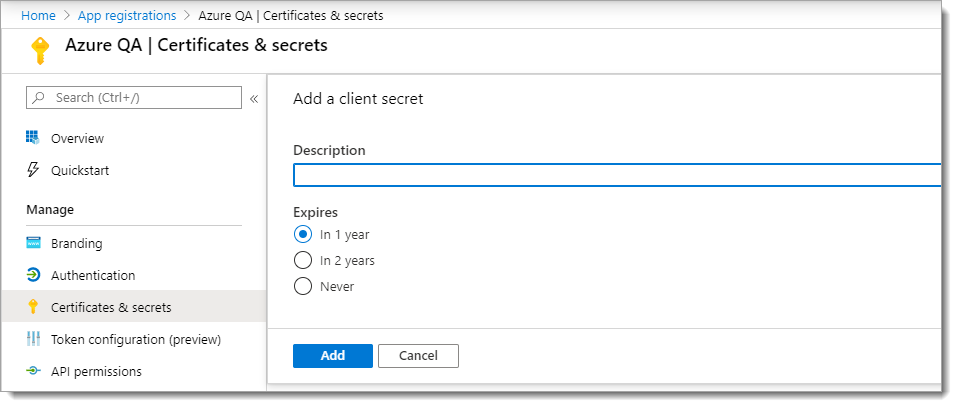
Click Add.
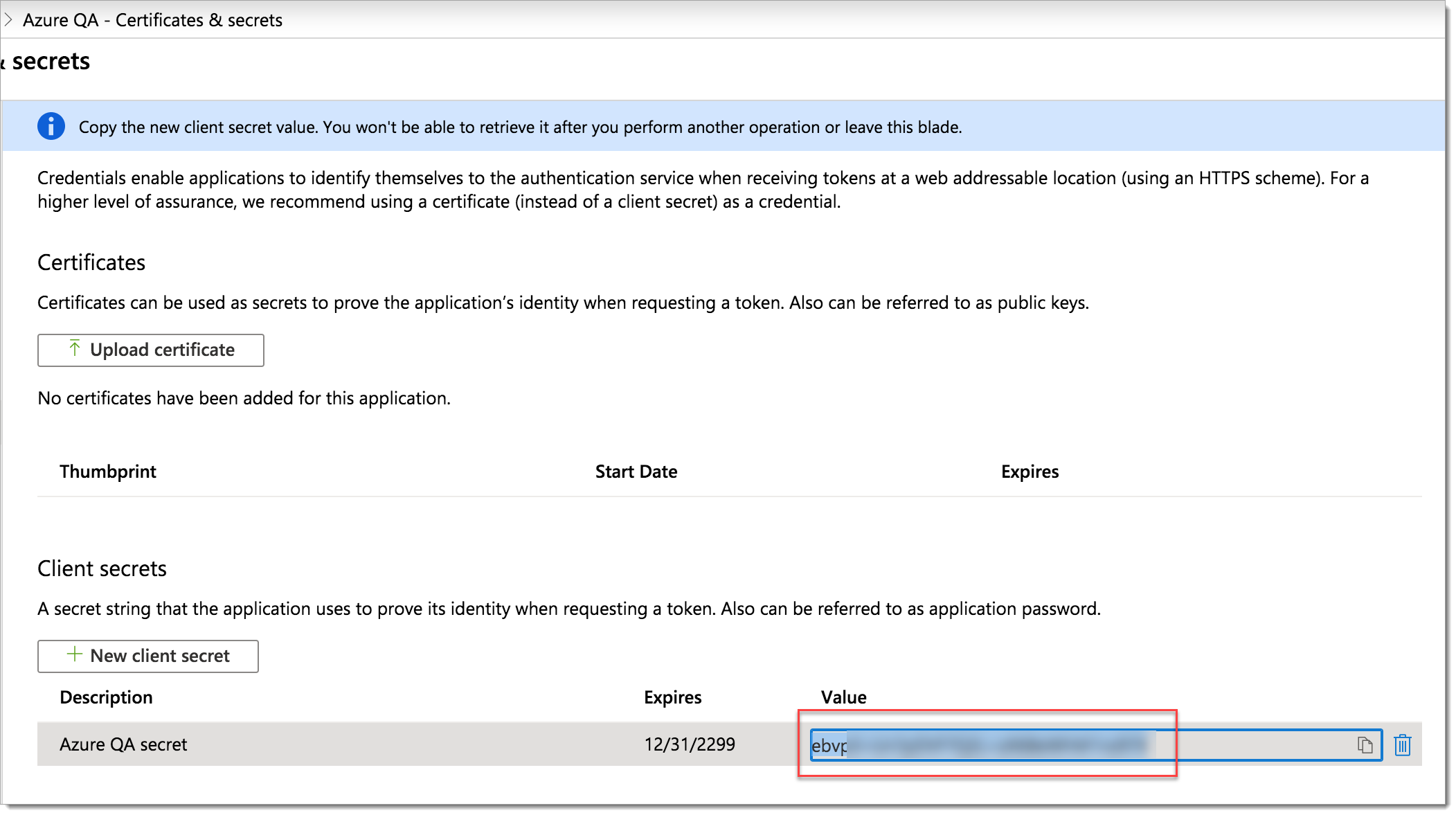
Copy the client secret key, before it gets masked when you leave the page.
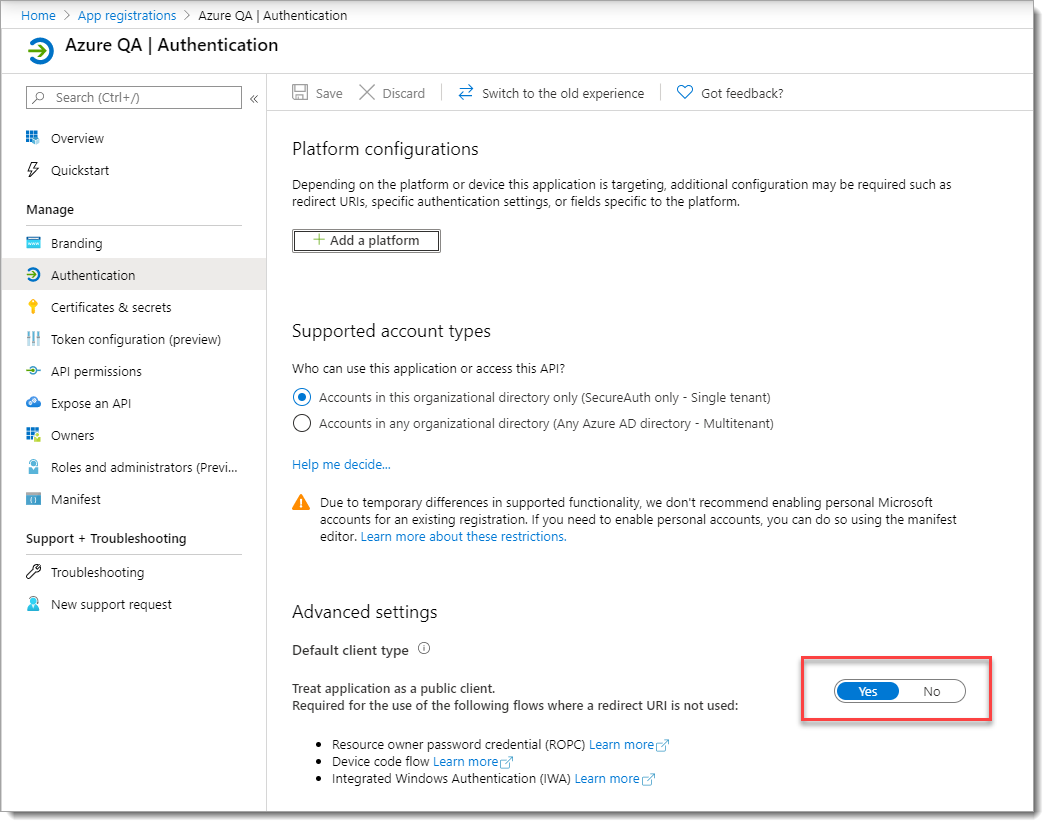
From the left pane for this app registration, click Authentication.
In the Advanced settings section, select Yes.
Step 4: Get Azure AD connection settings
When you add an Azure AD data store in the Identity Platform, you will need to capture and provide the following information in the Identity Platform data store connection settings.
Azure Tenant Domain (for example, company.onmicrosoft.com)
Directory Tenant ID
Client ID
Client secret key (when you created a client secret key in the Azure portal, you should have copied this value)
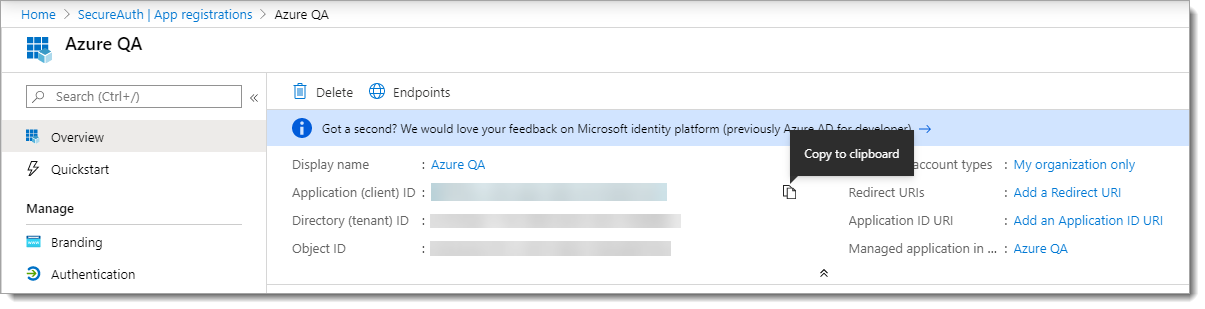
Capture connection IDs in Azure portal
Select Azure Active Directory.
Select App registrations.
From the list, click the application name link.
Hover your mouse to the right of the ID strings and select Copy to clipboard.