How policies are used in the Identity Platform
Policies in the SecureAuth® Identity Platform allow you to define rules to authenticate and block your users to certain resources. A policy is a collection of rules and acts as a middle piece in how user identity is asserted in the Identity Platform:
User login attempt to access a resource.
Identity Platform connects to the data store.
User is subjected to an authentication policy.
User identity is asserted into a resource.
The Identity Platform comes with a default policy that can be modified, but it cannot be deleted. You can also create multiple custom policies with different rules for your resources. When a new custom policy is created, the rules from the default policy are applied.
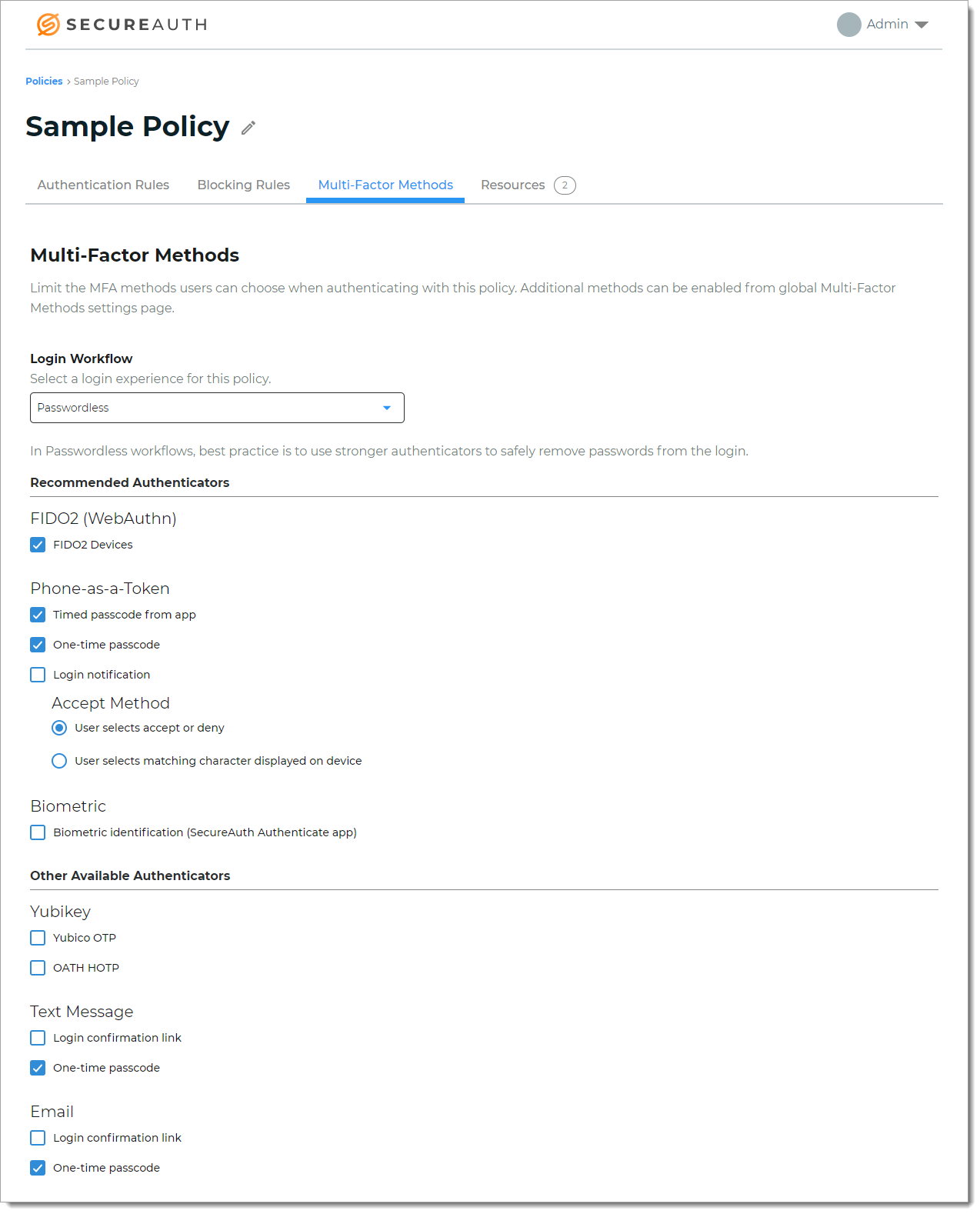
Multi-factor methods can be defined globally in the Identity Platform, and you can limit which multi-factor authentication methods are available in a policy. For example, your organization wants to use SMS text authentication method for a certain group of resources, but you want to make sure that your users can only use an email link for another set of resources.
In a policy, you configure authentication rules on the following tabs:
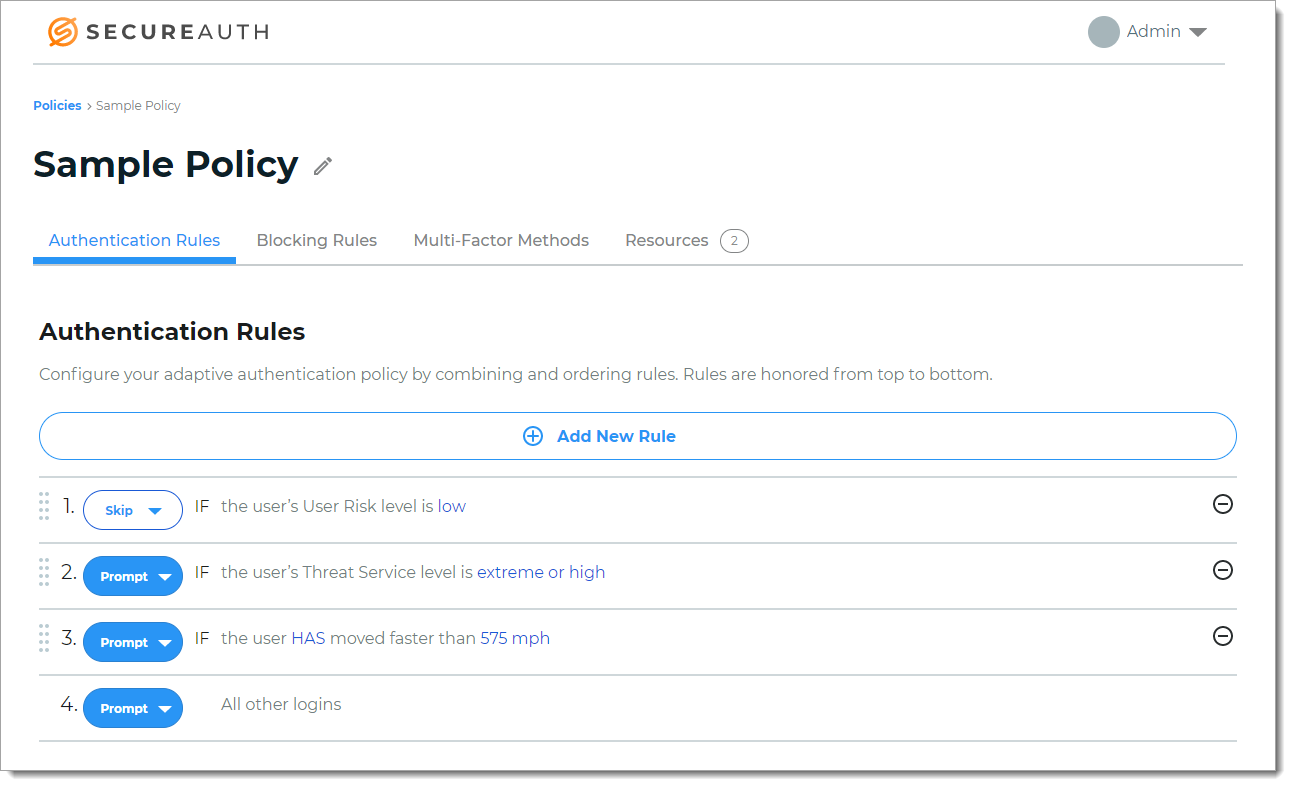
Authentication Rules | Rules to specify how to handle the user login attempts to access a resource are handled by the Adaptive Engine. For example, if a user logged in from Los Angeles, California (point A) at 11:15 a.m. and then from New York, New York (point B) at 11:45 a.m. on the same day, something might be off. The Adaptive Engine can determine whether it is logistically possible for the user to get from point A to point B at the time of the login. The rule option (Skip or Prompt) determines whether the user must use multi-factor authentication to verify their identity or be allowed access to the resource.
| |
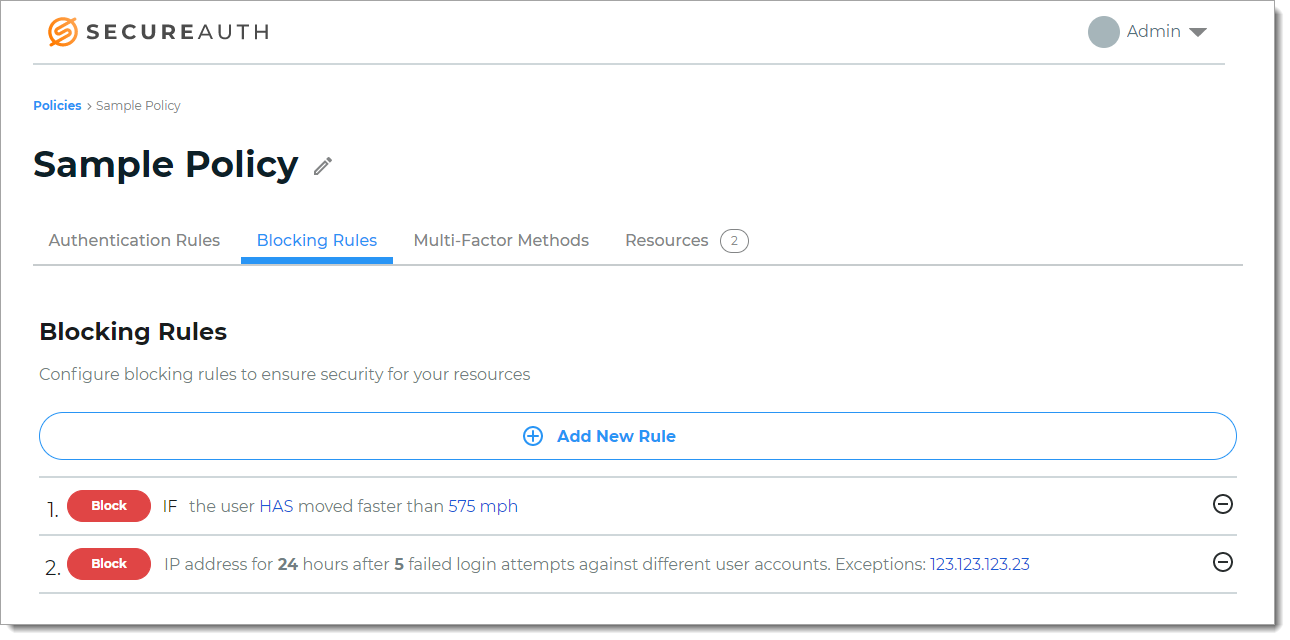
Blocking Rules | Rules to block users from accessing any resources. For example, your organization does not allow a user from a certain country to log in into your system, you can set up a blocking rule to prevent access.
| |
Multi-Factor Methods | Select the types of multi-factor methods (MFA) users can choose to authenticate with this policy. When you use the default policy or create a custom policy, the global settings for Multi-Factor Methods (configured from the left side of the main page under AUTHENTICATION) are applied in this tab. You can select which MFA methods you want applied to this policy. For example, your organization has the global settings enabled for a timed passcode from an authentication app and the use of a text message one-time passcode. But for this policy, you don't want to allow users the ability to use an email login confirmation link; you can clear that check box.
| |
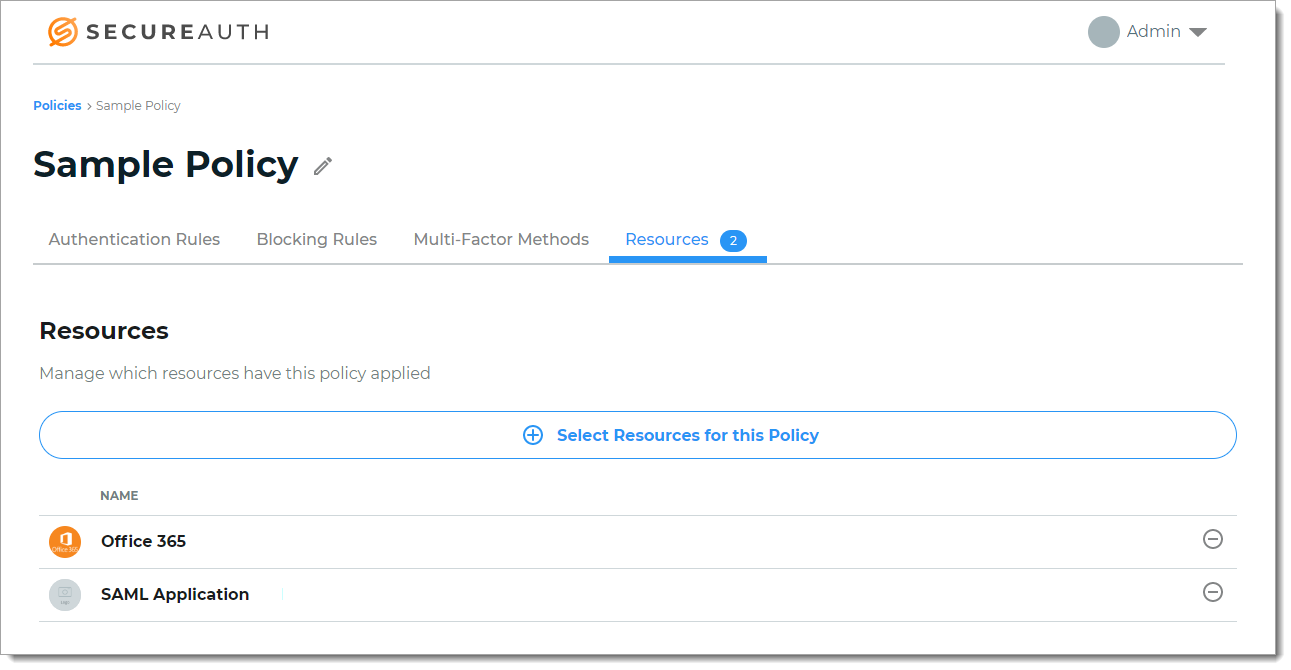
Resources | Pertains to the list of resources added by means of the Application Manager. Choose the resources to which this policy applies. By default, all resources are added to the default policy, unless otherwise assigned to a custom policy. For example, resources might be Office 365 and Salesforce logins to which the authentication rules, blocking rules, and multi-factor methods defined in this default policy apply to authenticate user logins.
|