Adaptive authentication rules settings in a policy
In a policy, set up your adaptive authentication rules to prompt for multi-factor authentication (MFA), skip MFA, or block users during login.
Use case scenario
As an administrator, you work for ACME Corporation. ACME has offices all over the world and a small group of executives who travel extensively. You need an authentication policy to:
Bypass MFA for executives who have minimal risks based on behavior and IP reputation.
Block login attempts from China, except for the group of executives working out of the Beijing office.
The following is an overview of how to set this up:
Rule 1: Skip MFA if the user is in ACME_executives group and poses a low user risk, and threat level.
Rule 2: Block user located in China or if user is not in the ACME_employees group.
Else Rule: The last catch-all rule. This rule cannot be deleted. You can set it to Prompt for MFA, Skip MFA, or Run Device/Browser recognition.
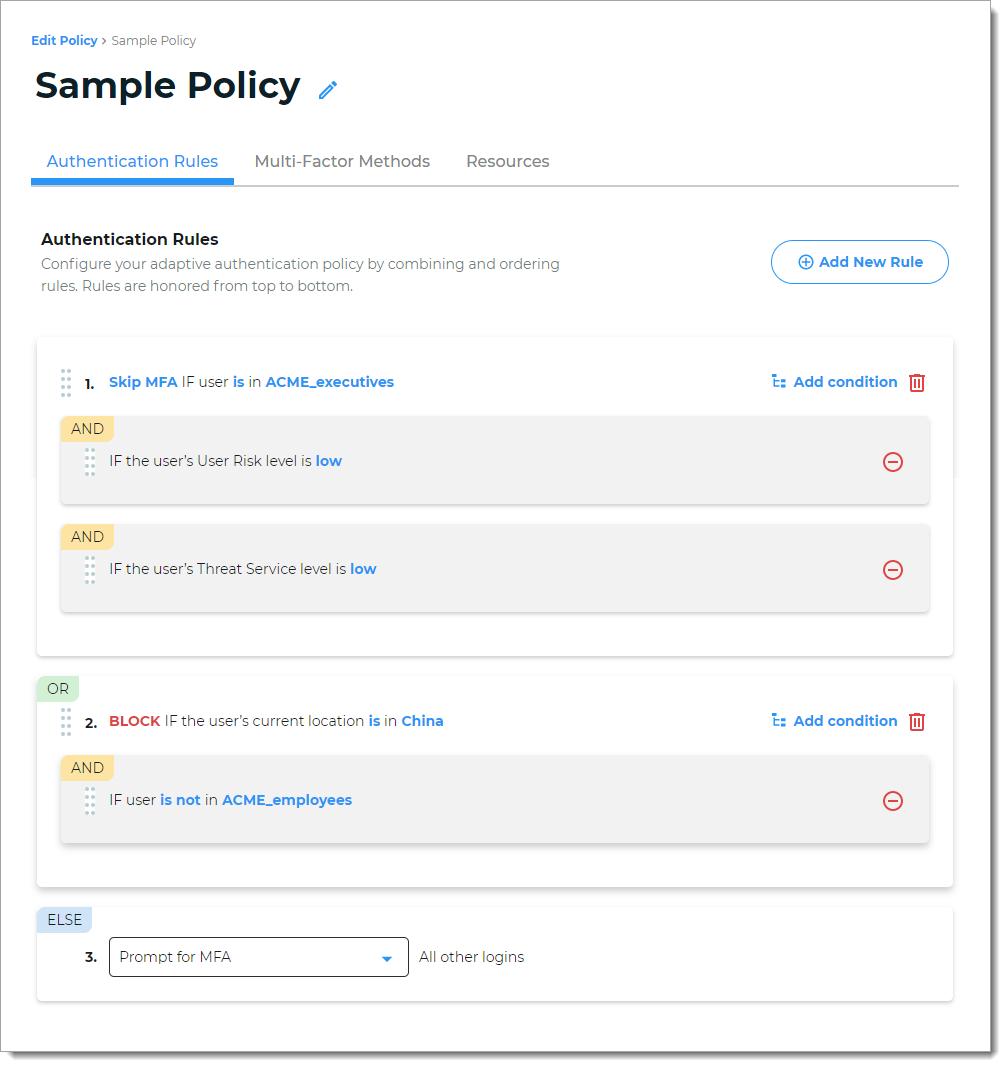
The Identity Platform honors the rules from top to bottom, and you can drag and drop rules to organize them.
Setting up authentication rules
With a policy open in edit mode, select the Authentication Rules tab.
When modifying a rule, you can do any of the following:
Select Prompt for MFA (require a form of authentication) when the user login invokes this rule.
Select Skip MFA (allow access) when the user login invokes this rule.
Select Block (block access) when the user login invokes this rule.
To move a rule, click and hold the 8-dot icon on the left to drag and drop a rule and change its hierarchy in the list.
To remove a rule or condition, click the minus icon or the trash can icon.
To change the properties of a rule, click the blue rule link.
To add a new rule, click Add New Rule and choose from the following rule types:
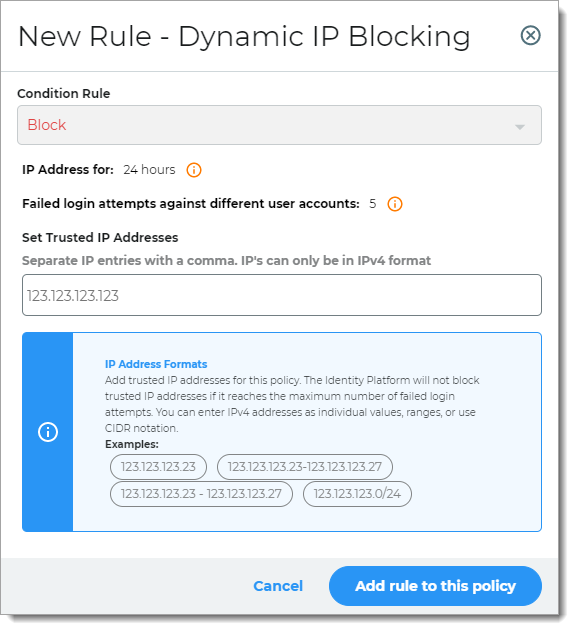
Dynamic IP Blocking
Rule to block source IP address from password spraying and other online password attacks.
For example, instead of locking user accounts, the Identity Platform blocks login attempts coming from the source IP address.
Note
To change how long the Identity Platform blocks the source IP address after a specified number of failed logins, go to IP Filtering on the left side of the page.
Take note that the Identity Platform applies this change to all policies that use the Dynamic IP Blocking rule.
In the Set IP Addresses field, add trusted IP addresses for this policy. The Identity Platform will not block trusted IP addresses if it reaches the maximum number of failed login attempts.
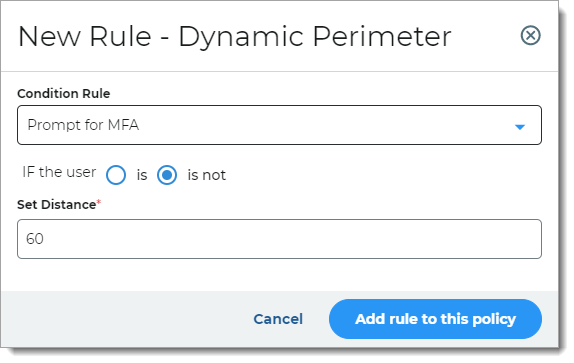
Dynamic Perimeter
Rule to determine access based on whether the user login is or is not within a set distance from the previous location.
For example, if the user login is more than 60 miles from the previous location, then the user is prompted for a form of authentication.
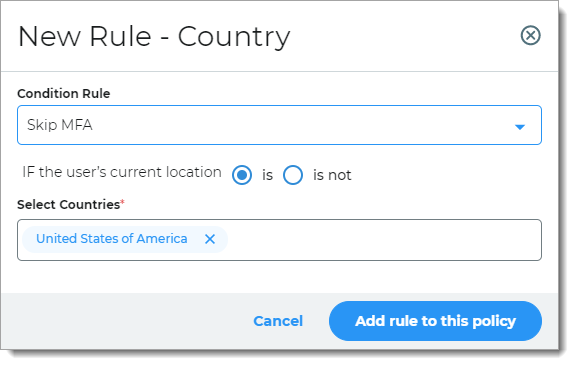
Country
Rule to determine access based on whether the user login is or is not within a defined country.
For example, if the user login is in the United States, then the user is allowed access.
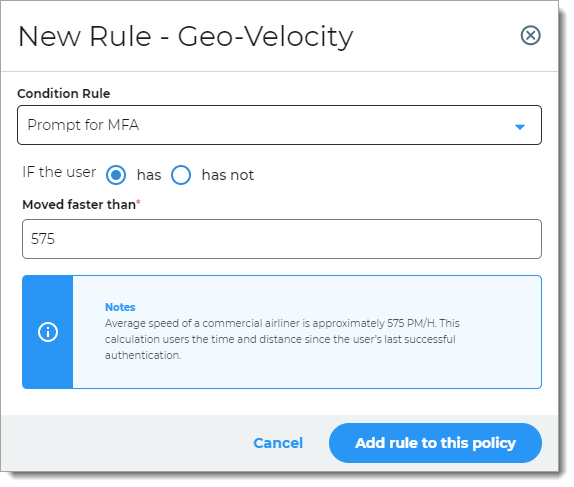
Geo-velocity
Rule to determine access based on the speed of travel between the previous login and current login attempt.
For example, if the user logged in from Los Angeles, California (point A) at 11:15 a.m. and then from New York, New York (point B) at 11:45 a.m. on the same day, then the user is prompted for a form of authentication.
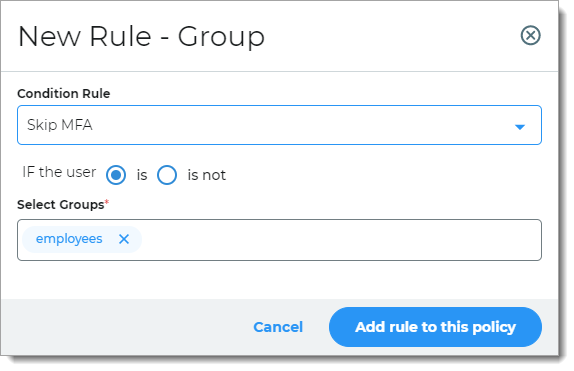
Group
Rule to determine access based on group membership.
For example, if the user is a member of a specified group, then the user is allowed access.
Note
Before you can use this rule, groups must be defined in the data store for your organization.
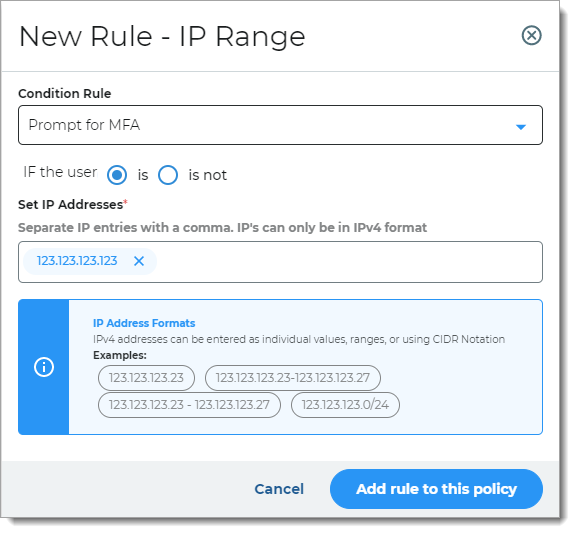
IP Range
Rule to determine access based on IP ranges. You can enter IPv4 addresses as individual values, ranges, or using CIDR Notation.
For example, if the user login comes from any of the specified IP addresses, you can set it to prompt the user for a form of authentication, allow the user to skip MFA, or block the user.
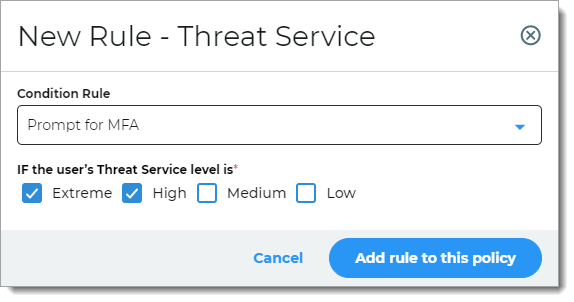
Threat Service
Rule to determine access based on known risks associated with the login attempt as determined by the SecureAuth Threat Service; it analyzes IP traffic for threats.
For example, if the user login is associated with a known threat, then the user is prompted for a form of authentication.
Note
You must have a license to use this feature. To learn more about the Threat Service rule, contact your SecureAuth Account Manager.
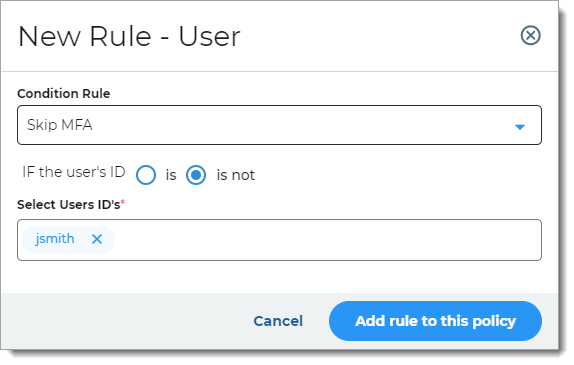
User
Rule to determine access based on whether the user login is the same as the specified user ID.
For example, if the user login matches the user ID, then the user is allowed access.
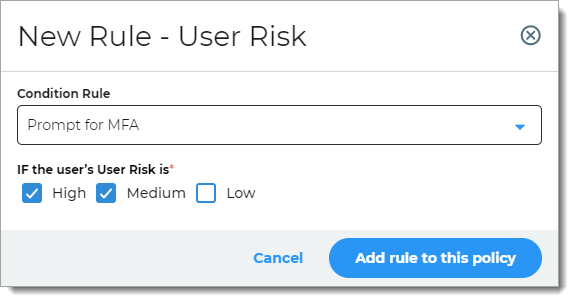
User Risk
Rule to determine access based on user reputation and behavior factors associated with the login attempt. User risk is a learning algorithm of user behavior over time.
For example, if the login reputation and behavior of the user falls into the specified risk level, then the user is prompted for a form of authentication.
Note
You must have a license to use this feature. To learn more about the Threat Service rule, contact your SecureAuth Account Manager.
All other logins
This is a catch-all rule evaluated last and determines access (Prompt MFA or Skip MFA) if it doesn't trigger any of the above rules. You cannot delete or reorder this rule in the list.
The Run Device/Browser Recognition option runs device/browser recognition and applies one of the following conditions:
Skip MFA when the device or browser profile matches the user profile
Prompt for MFA when the device or browser profile do not match
Prompt for MFA when device recognition is not enabled
Prompt for MFA when the Login workflow includes "Valid Persistent Token"
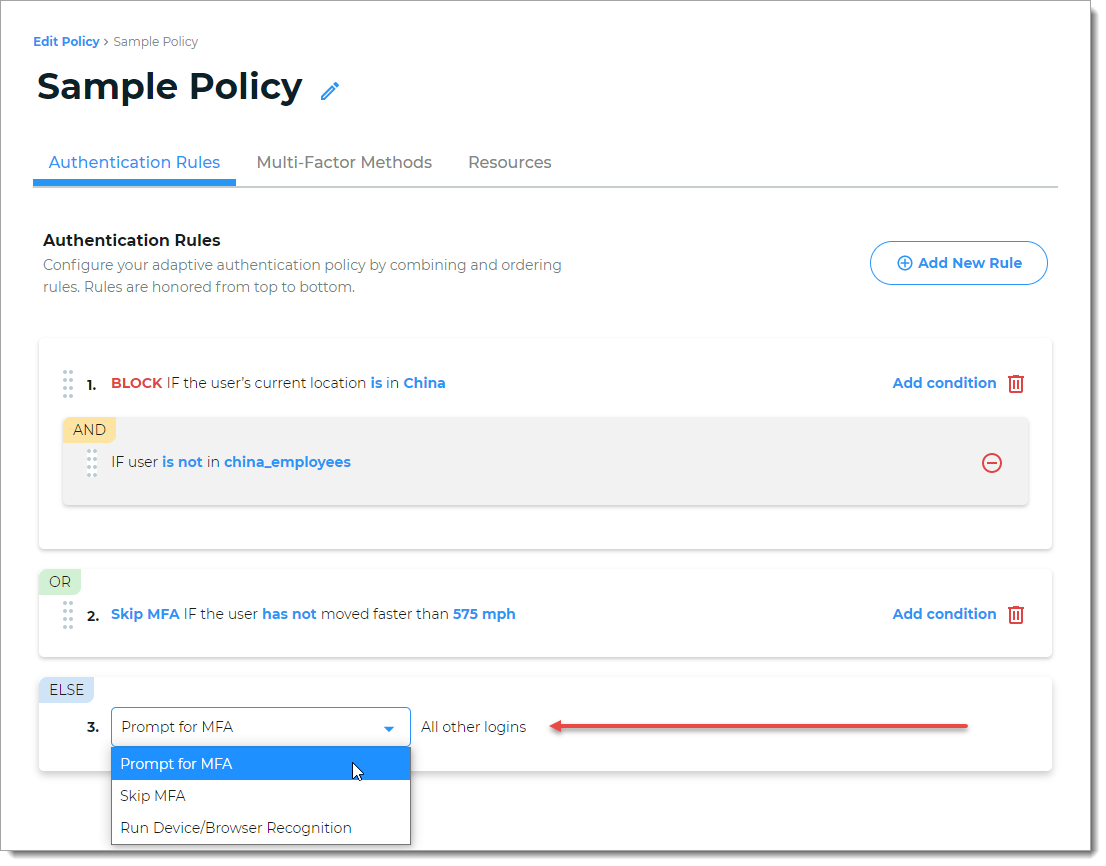
After you add and reorganize the authentication rules, Save your changes.