SecureAuth User Risk settings
The SecureAuth® Identity Platform uses machine learning to track and analyze user login behavior patterns. It tracks the login patterns for a period of time to identify normal patterns, then assigns each user a personal risk score. Because the login behavior pattern and risk score is unique to each user, it prevents bad actor attempts to access your resources.
To learn how the Identity Platform calculates user risk scores and uses them, see Machine learning user risk score calculations.
For each level of user risk (high, medium, and low) you can define the Identity Platform risk actions.
Prerequisites
Identity Platform version 19.07 or later
Prevent package license – contact SecureAuth Support
On the left side of the Identity Platform page, click Risk Providers.
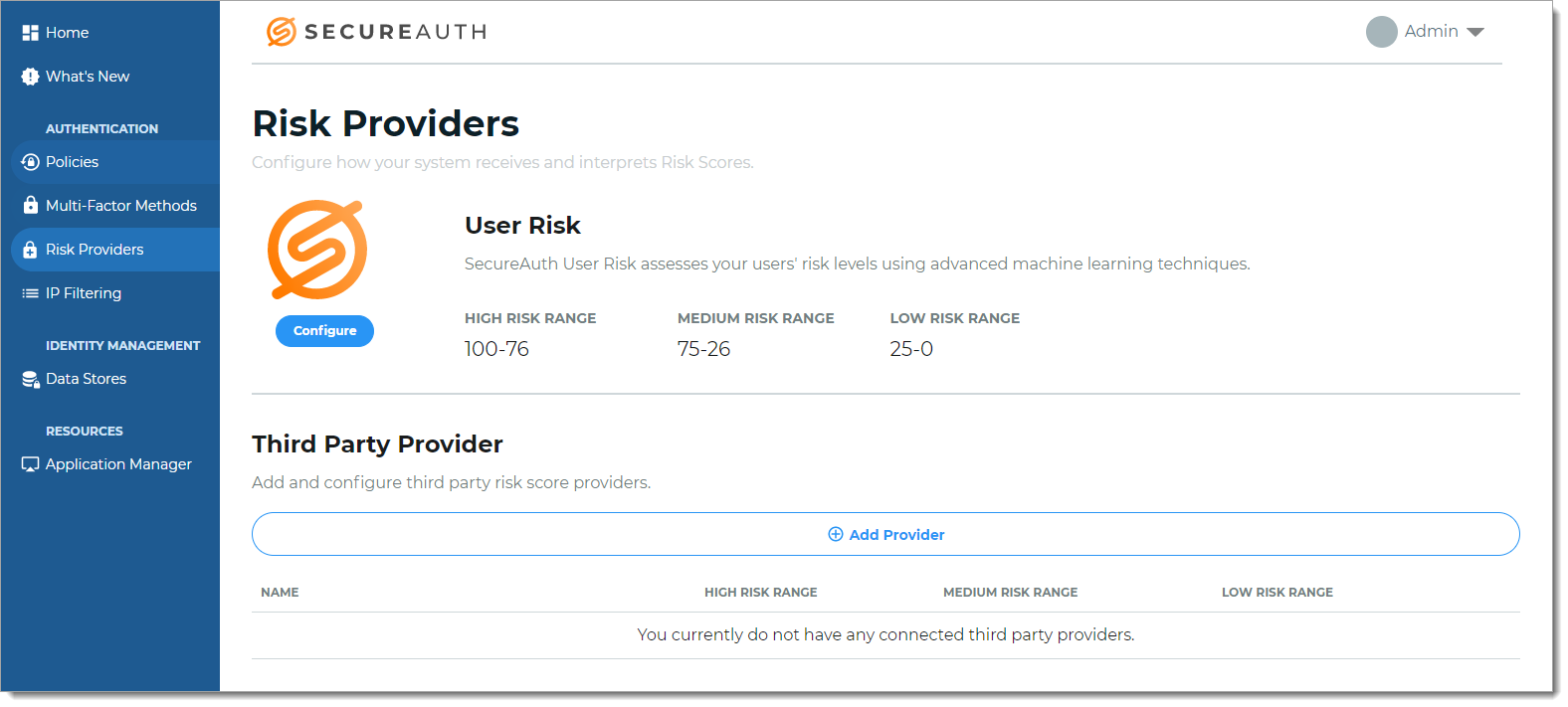
Click Configure.
The configuration page to adjust the user risk thresholds appears.
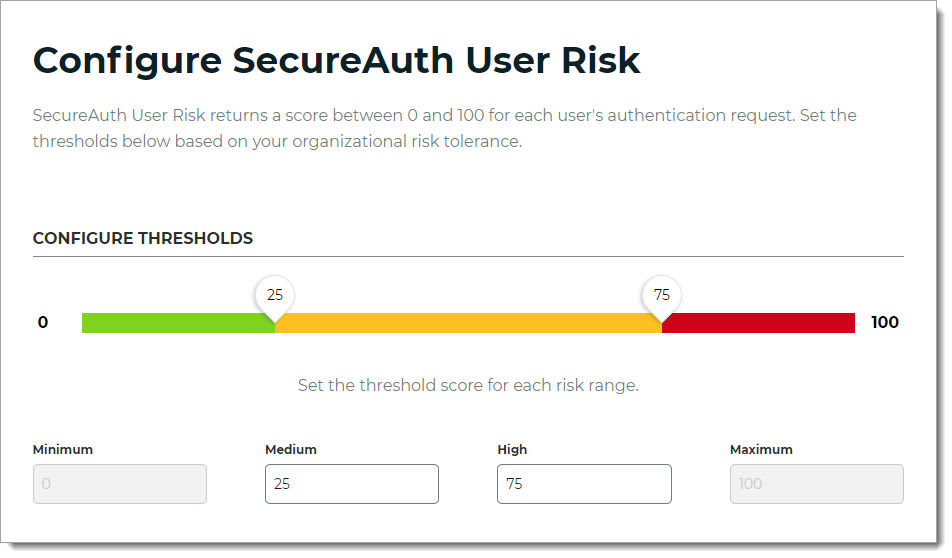
To adjust the risk ranges, move a slider or enter the threshold score for Medium and High risk scores.
By default, Minimum is 0 (zero) and Maximum is 100.
Save your changes.
Some user risk features, such as Redirect to realm or URL (available for hybrid deployments only), must be set up in the Identity Platform Advanced Settings (formerly Classic Experience) so you can create custom actions. Additionally, setting custom minimum and maximum risk thresholds are configured in Advanced Settings.
If you don't need custom user risk features, you can ignore this section.
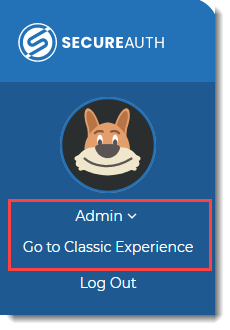
On the left side of the Identity Platform New Experience page, click your profile and select Go to Advanced Settings.
If you haven't worked in the SecureAuth Identity Platform Advanced Settings, read Web Admin introduction to learn about realms and how they work. (A realm is a workflow configured by an administrator and used by end users to complete the authentication process.)
Create a realm.
Set up the SecureAuth Identity Platform realm with the customized risk score providers, risk scores, and risk actions right for your organization's risk tolerance.
Optional: Add a third-party provider, such as SailPoint IdentityIQ or Exabeam UEBA.
Optional: Integrate the SecureAuth Pre-Login Assessment Survey.
For a detailed discussion about how SecureAuth calculates user risk scores, see Machine learning user risk score calculations.
Set up the SecureAuth Identity Platform realm with the customized risk actions, such as Redirect to realm or URL, that are right for your organization.
The following risk score actions are available in the Identity Platform Advanced Settings:
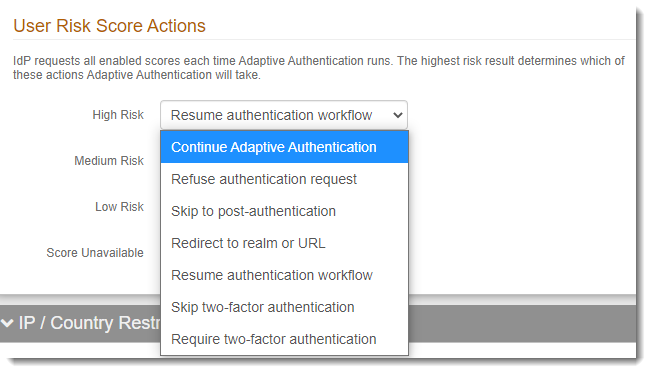
If your organization needs one of the user risk score actions available in Advanced Settings, such as Redirect to realm or URL, you can add it to a hybrid deployment. Contact SecureAuth Support to edit the web.config file to include the action you need.
Caution
After you edit the web.config file, if you change the policy in the New Experience and save your changes, this will overwrite the manual changes on the web.config file. You must add the changes again.
Save your changes.
Next steps
Open a policy and add a new User Risk rule as applicable on the Authentication Rules tab.
Next steps for custom user risk features
Monitor user risk scores after you've completed onboarding the Prevent package. After three weeks of data retrieval you should see risk scores normalize. If the risk scores for your organization are still high, contact SecureAuth Support to check the machine learning logs.