Add Microsoft Entra ID data store
In the SecureAuth® Identity Platform, you can add an Microsoft Entra ID (formerly Azure AD) data store to assert or manage user identity information. This requires registering the Identity Platform in Microsoft Entra admin center to communicate with Microsoft Entra ID.
Note
The SecureAuth Connector is not required for Microsoft Entra ID data store in the Identity Platform.
Prerequisites
Identity Platform release 22.02, cloud or hybrid deployment
Identity Platform is registered in Microsoft Entra admin center with application read/write permissions to Microsoft Entra ID. For more information, see Microsoft Entra ID configuration. You will need to capture the connection IDs and client secret key from the Microsoft Entra admin center.
Data store limitations
Note the following issues with Microsoft Entra ID data stores:
Login workflows that include a password is not supported for guest accounts on Microsoft Entra ID. Use passwordless login workflow.
The username and password login workflow is not compatible with conditional access and MFA. For more information, see this Microsoft article.
You can only use Microsoft Entra ID in applications created in the New Experience.
Password complexity rules set up in the Identity Platform cannot be applied to Microsoft Entra ID.
Process
There are two parts to adding a data store in the Identity Platform — (1) adding the data store and (2) mapping the data store properties.
Step 1 of 2: Add Microsoft Entra ID data store
The first part of adding an Microsoft Entra ID data store is configuring the data store name, connections, credentials, and search attributes.
On the left side of the Identity Platform page, select Data Stores.
Select the Data Stores tab.
Click Add a Data Store.
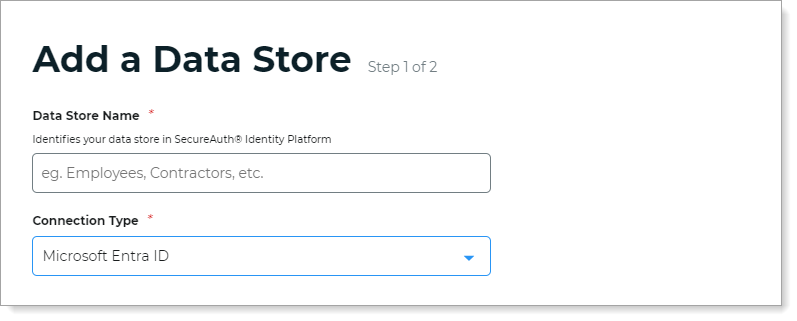
Set the Data Store Name and select the Connection Type as Microsoft Entra ID.
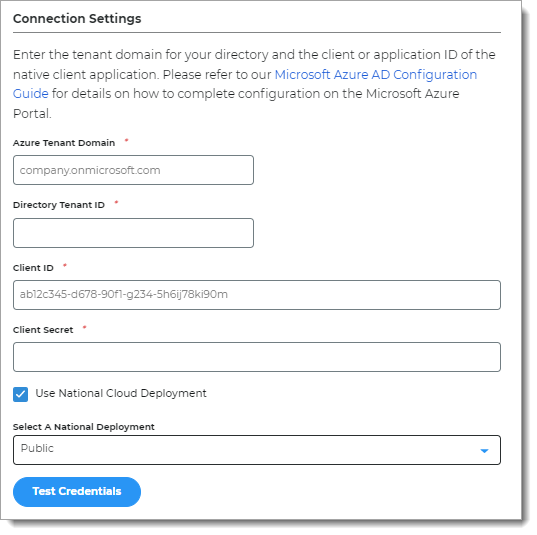
In the Connection Settings section, enter the connection information for your configured Microsoft Entra ID data store.
Note
For information about how to get the connection settings for Microsoft Entra ID, see Microsoft Entra ID configuration.
Azure Tenant Domain
The domain of the Microsoft Entra ID (formerly Azure AD) directory.
For example, company.onmicrosoft.com
Directory Tenant ID
The Directory (tenant) ID value copied from the Microsoft Entra admin center for the registered Identity Platform application.
Client ID
The Application (client) ID value copied from the Microsoft Entra admin center for the registered Identity Platform application.
Client Secret
The client secret copied from the Microsoft Entra admin center for the registered Identity Platform application.
Use National Cloud Deployment
Select check box and set to the regional instance for your Microsoft Entra ID data store. Options are:
Public (default)
China
Germany
US Government
Test Credentials
Test the data store connection by clicking Test Credentials. (This button is available only in hybrid deployments of Identity Platform 22.02 and 22.12.)
Click Continue.
The Map Data Store Properties page opens.
Step 2 of 2: Map the Microsoft Entra ID data store properties
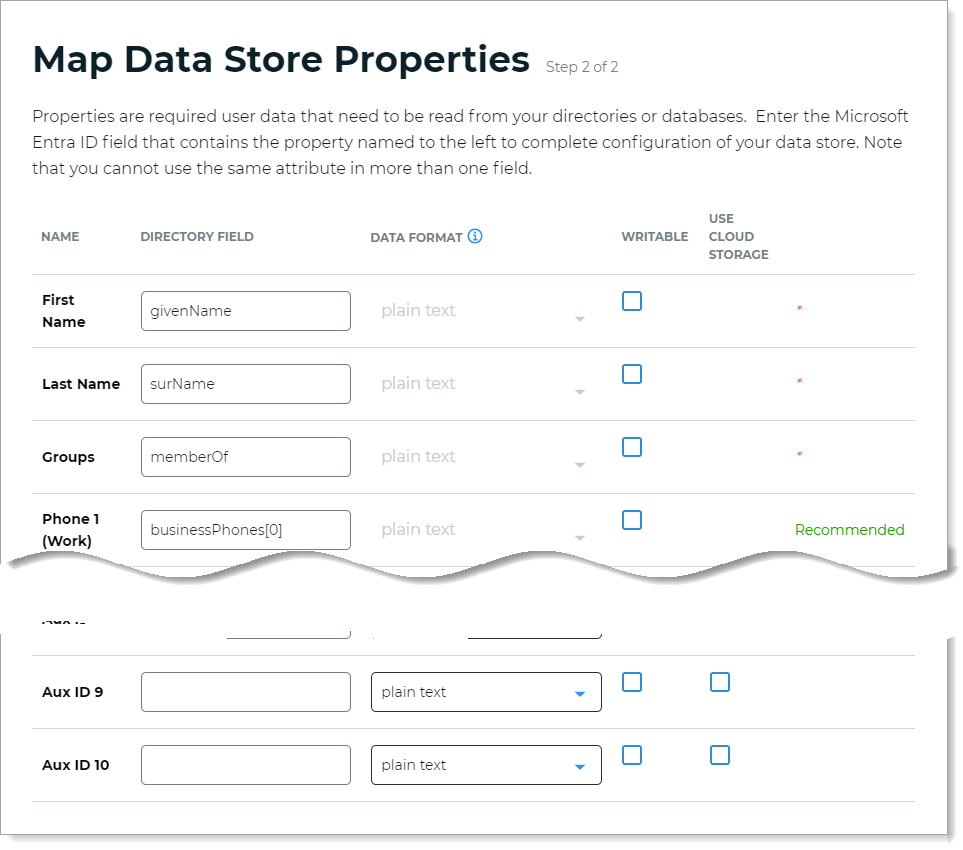
The second part of adding an Microsoft Entra ID data store is mapping the data store properties.
Each user is uniquely identified by profile data that is read from or stored in your directories and databases.
The Identity Platform does not store user profiles, so your Microsoft Entra ID attributes must be mapped to the Identity Platform profile properties to be read and updated in the directory by the Identity Platform. The Microsoft Entra ID attribute mapped to the property is retrieved only when required for authentication or assertion purposes.
For more information about how data store profile properties are stored for on-premises, hybrid, or cloud Identity Platform deployments, see List of stored profile field properties.
Note
Each mapped profile property needs to have its own directory attribute. You cannot map the same directory attribute to more than one property.
For example, you cannot map the mobilePhone attribute in Phone 3 because that attribute is already mapped to Phone 2.
On the Map Data Stores Properties page, define the required attributes in the Directory Field that corresponds to each Microsoft Entra ID property required by your environment and the Identity Platform. The required attributes are:
First Name
Last Name
Groups
Email 1 (Work)
Define any other applicable attributes in the Directory Field that correspond to each Microsoft Entra ID property.
In the Writable column, define whether a profile property can be writable (select check box) or not writable (cleared check box) according to your Microsoft Entra ID directory configuration.
For example, if you want to allow users to update their personal email address on the self-services page, select the Writable check box.
Note
Test the data store connection by clicking Test Credentials. (This button is available only in hybrid deployments of Identity Platform 22.02 and 22.12.)
For the mapped Aux ID 1 through Aux ID 10 fields, specify the Data Format to define how data is encrypted and stored in the directory.
For cloud deployments, certain profile properties (for example, push tokens, behavioral biometrics, and device profiles) are generated and used by SecureAuth, and stored in the SecureAuth cloud database.
The selection options are:
plain text – store data as regular, readable text (default)
standard encryption – store and encrypt data using RSA encryption
advanced encryption – store and encrypt data using AES encryption
standard hash – store and encrypt data using SHA-256 hash
Click Save Data Store.
The Microsoft Entra ID data store you just added appears in the User Data Stores list.