End user login experience on Mac
This topic describes in detail the Login for Mac experience for your end users to help you decide what configurations are best for your organization.
Important
The enterprise WiFi connection must be disabled on the Mac to log on to the domain. A public WiFi connection or a wired connection can be used for Internet access.
If you are included in a bypass group, you will need to wait for the network group to be fully connected before logging on.
First login with password only
End users can log in without second-factor authentication for the number of days set by the administrator in the Grace Period option. This allows end users to log in with a password only (without using second-factor authentication), and typically occurs after the Login for Mac installation. End users can then access their device to set up their two-factor authentication methods, such as PIN creation and answers to Security Questions, before they must authenticate to access their device.
Use case: Password-only login is useful for one or more new employees who have been issued a laptop on their first day of employment. For example, if Login for Mac is already installed on the laptops and the admin has not set the Grace Period option, new employees might not be able to log into their computer if they cannot connect to the SecureAuth Identity Platform realm to register their mobile phone or self-service page to enter a phone number.
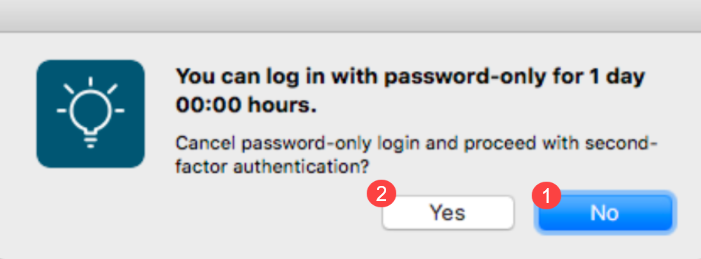
Workflow: End users are prompted to log in with their username and password only. The login screen indicates the number of days end users can continue to log in with a password only on the machine, as shown in the following image.
End users who want to log in with a password only click No next to number 1 to display the password field and log in. After end users set up their second-factor methods, they are ready to authenticate so they click Yes next to number 2, which dismisses the password-only screen and opens the 2FA login screen. Thereafter, the 2FA login screen opens for end users.
 |
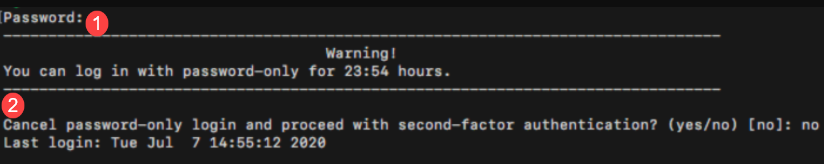
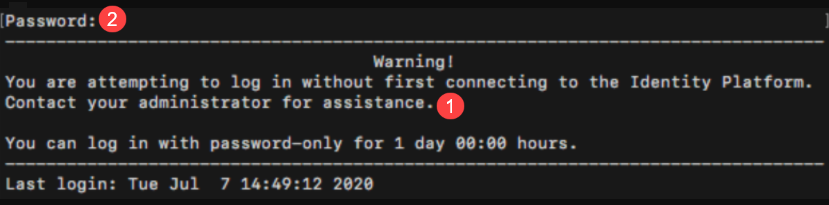
If your site uses private keys with Pluggable Authentication Module (PAM), end users will see the following message when they log in with password only. End users who want to log in with a password only enter their password next to number 1 and enter No for number 2 and log in. After end users set up their second-factor methods, they are ready to authenticate so they enter Yes for number 2, which dismisses the password-only screen and opens the 2FA login screen. Thereafter, the 2FA login screen opens for end users.
 |
Login without connection to Identity Platform
End users can log in when their machine does not have a connection to the Identity Platform if the Install Login for Endpoint without connection to Identity Platform and Grace Period options are set. This allows end users to log in with a password only (without using second-factor authentication).
Use case: Password-only login is useful if a third-party company configures machines for end users and the third-party company does not have connectivity to the Identity Platform. For example, if Login for Mac is installed on machines by a third-party without a connection to the Identity Platform, and the admin has not set the Install Login for Endpoint without connection to Identity Platform and Grace Period options, when new employees get their machine, they will not be able to log in.
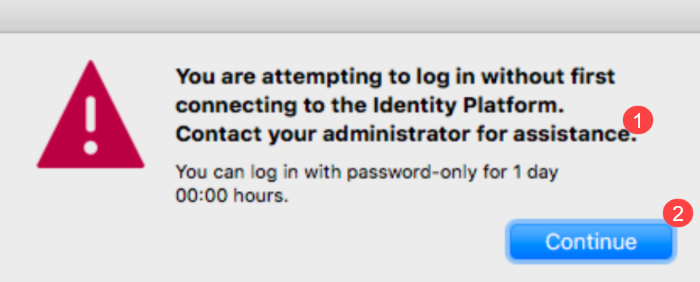
Workflow: End users are prompted to log in with their username and password only. The login screen indicates the number of days end users can continue to log in with a password only on the machine, as shown in the following images.
End users whose machines are not connected to the Identity Platform should contact the admin first so they can copy the message next to number 1 and send it to their admin. End users can then click Continue next to number 2 on the UI to display the password field or enter a password on the PAM UI and log in. After the machine connects to the Identity Platform, the 2FA login screen opens for end users so they can set up their second-factor methods and log in.
 |
If your site uses private keys with Pluggable Authentication Module (PAM), end users will see the following message when they log in with password only. The workflow is the same as in the previous "Workflow" paragraphs.
 |
First-time login experience
If the administrator has set up a mandatory questionnaire for your organization to fill out prior to logging into Login for Mac, you will log in with a username and then you will be redirected to the questionnaire. After you fill out the questionnaire and submit it, close the browser to display the second-factor authentication screen.
Enter your domain username and password on the Mac login screen.
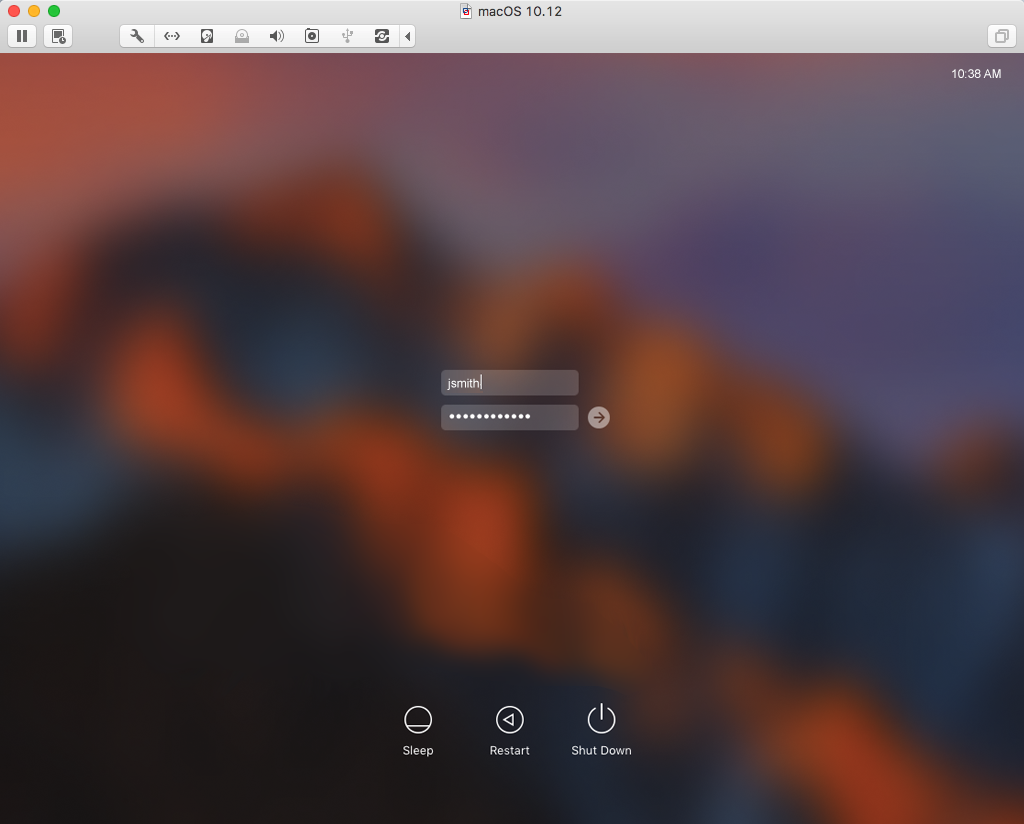
The first time end users log in, Login for Mac shows only OATH-based methods (for example, TOTP, HOTP YubiKey), if at least one method is available to end users. If at least one OATH-based method is not available to end users, they can use any other available method. This could be a method that uses the SecureAuth Authenticate App on your mobile device or another device provisioned with the SecureAuth IdP realm to supply timed passcodes, such as an HOTP YubiKey.
If end users need to login when their machine is offline, they must choose an OATH-based method during the first login. After end users select a timed authentication option and enter their password, TOTP and HOTP passcode options will be available for them to use when logging on the machine offline.
The window pictured above appears only the first time you use Login for Mac.
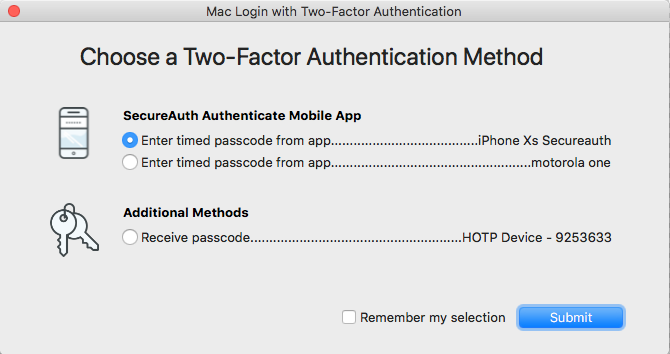
End users with more than one mobile phone or YubiKey provisioned can select which device or token to use when online. When logging on the machine offline, any OATH-based method that was used online will be available for use.
If you do not have an authentication method that provides an OATH-based method, then select any other option available to you.
Optionally, check the Remember my selection box if you want to use this same authentication method the next time you log on the Mac.
Enter the passcode that appears on the device, and then click Submit.
After successfully logging on the Mac using a timed passcode, timed passcodes from that device can be used for login access when offline, i.e., when the Mac is not connected to the Internet.
Log out of the Mac.
Log back on the Mac, and select an authentication option from the list of multi-factor authentication methods for which you have previously enrolled.
If your list of available authentication options is lengthy, you may need to scroll down the list if the option you want does not appear on the main page.
Optionally, check the Remember my selection box if you want to use this same authentication method the next time you log on the Mac.
Click Submit to access the Mac on the network.
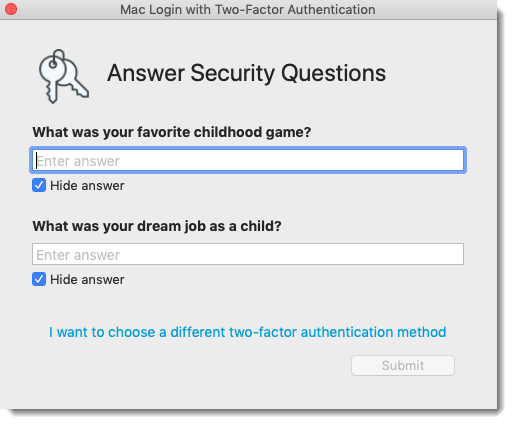
No matter which option you choose, you can return to this selection window by clicking the I want to choose a different two-factor authentication method link located at the bottom of each second-factor authentication screen.
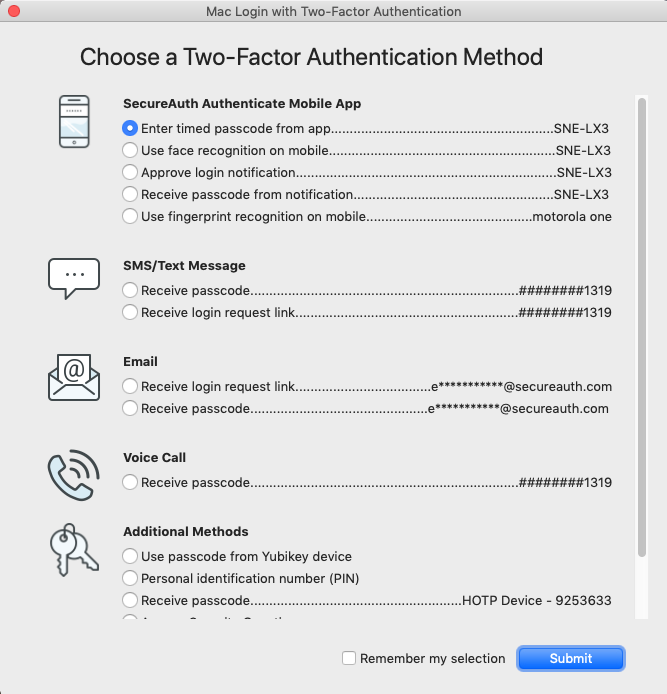
Authentication method workflows are described in the following sections.
SecureAuth Authenticate Mobile app options
The methods in this section are delivered via push notification and require the use of the SecureAuth Authenticate App.
In the following screens, you can show or hide the passcode so that, as you type, you see characters instead of dots.
Under the passcode field, clear the Hide passcode checkbox to see the passcode.
Set the Hide passcode checkbox to hide the passcode.
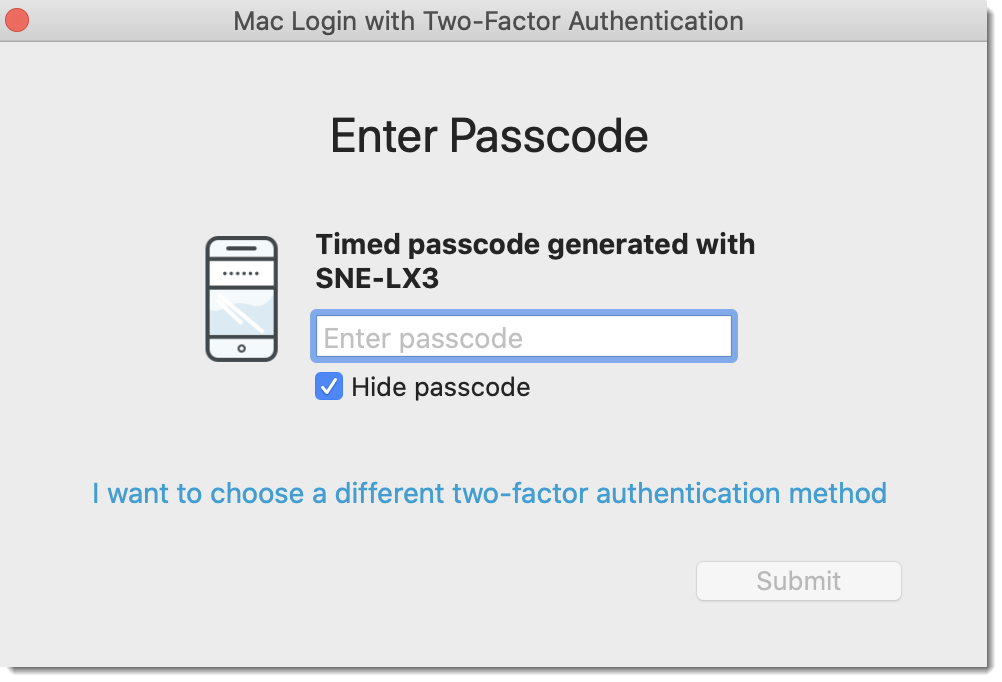
Enter timed passcode from app
This method and "Enter passcode from YubiKey" are displayed at first login, if available. If not available, all available methods are displayed.
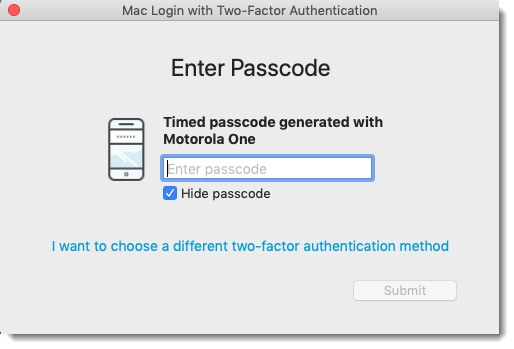
When selecting this option, the Enter Passcode window appears.
Enter the OATH OTP from your SecureAuth OTP App.
Click Submit to log on the Mac.
Receive passcode from notification
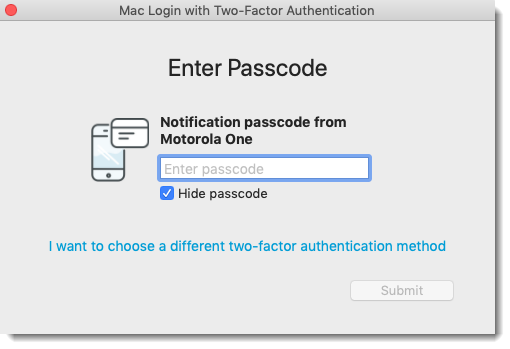
When selecting this option, the Enter Passcode window appears.
Enter the passcode that was sent to the SecureAuth Authenticate App on your mobile device.
Click Submit to log on the Mac.
Approve login notification for fingerprint recognition
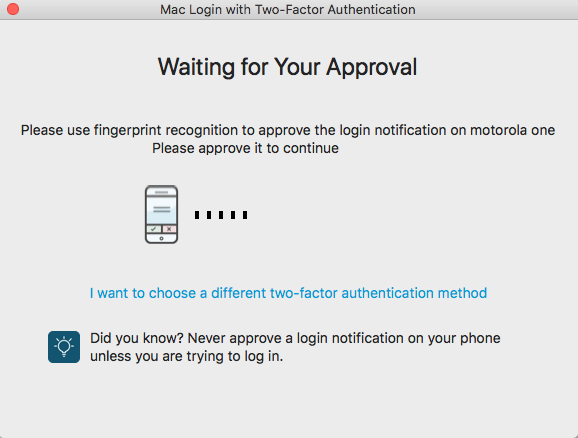
When selecting this option, the Waiting for Your Approval window appears.
Accept the login notification sent to the SecureAuth Authenticate App on your mobile device to log on the Mac.
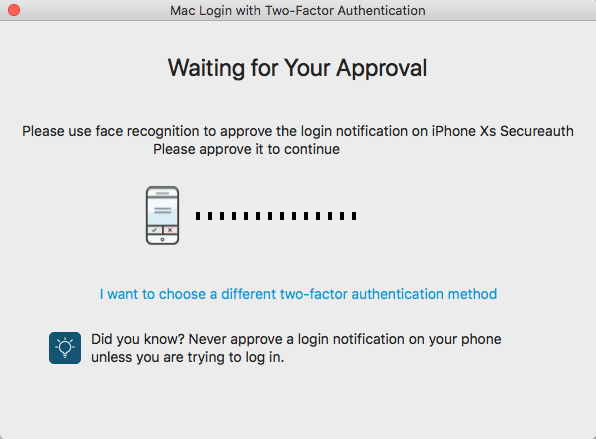
Approve login notification for face recognition
This option is available for iOS only. When selecting this option, the Waiting for Your Approval window appears.
Accept the login notification sent to the SecureAuth Authenticate App on your mobile device to log on the Mac.
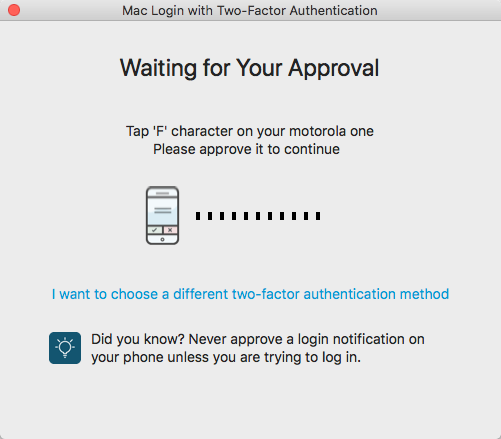
Approve login notification for Symbol-to-Accept
When selecting this option, the Waiting for Your Approval window appears.
Receive the set of 4 symbols sent to the Authenticate mobile app on your mobile device.
One symbol will display on your Mac desktop or laptop.
On the Authenticate mobile app, tap the symbol that matches the one displayed on your desktop or laptop. You are then logged on the Mac.
SMS / Text Message
When text message is set up as an MFA method in the Identity Platform, end users could see these options.
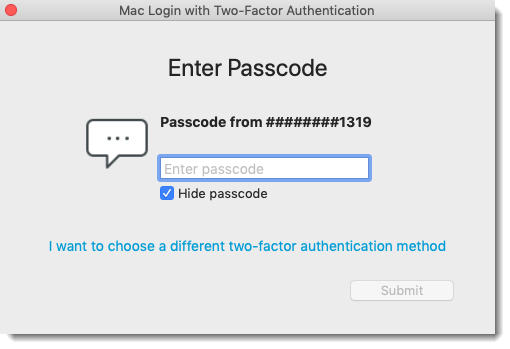
Receive passcode
When selecting this option, the Enter Passcode window appears.
Enter the passcode sent via SMS to your mobile phone.
Click Submit to log on the Mac.
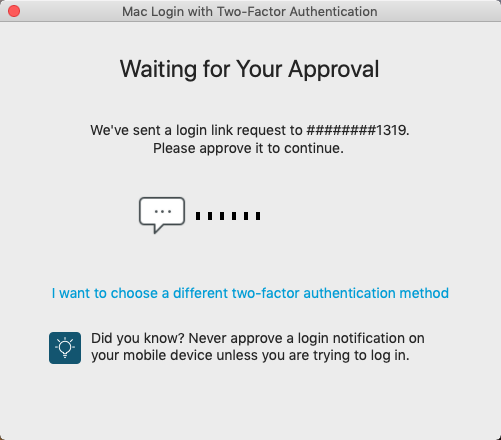
Receive link
When selecting this option, the Waiting for Your Approval window appears.
Tap the login link request sent via SMS to your mobile phone.
The following page will close after the login request is verified.
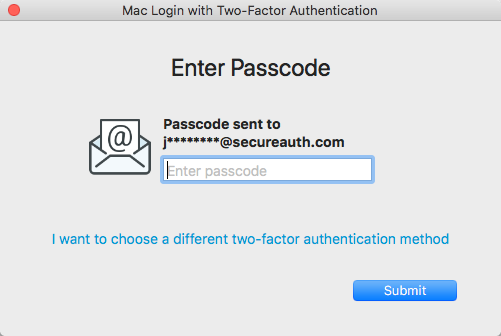
When email is set up as an MFA method in the Identity Platform, end users could see these options.
Receive passcode
When selecting this option, the Enter Passcode window appears.
Enter the passcode sent to your email address.
Click Submit to log on the Mac.
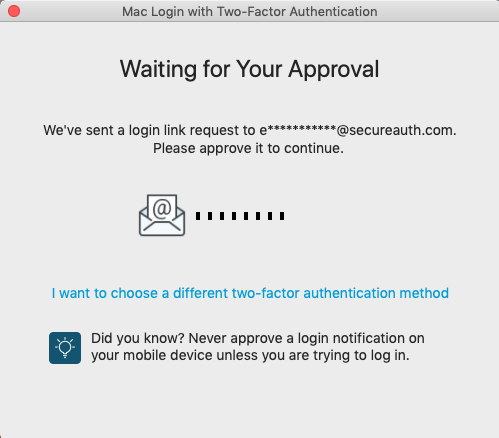
Receive link
When selecting this option, the Waiting for Your Approval window appears.
Tap the login link request sent to your email address.
The following page will close after the login request is verified.
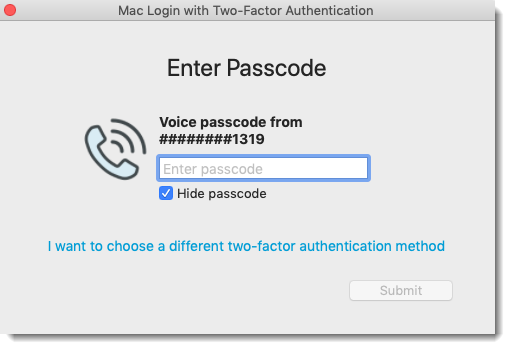
Voice Call
When voice call is set up as an MFA method in the Identity Platform, end users could see the following option.
Receive passcode
When selecting this option, the Enter Passcode window appears.
Enter the passcode received from the phone call.
Click Submit to log on the Mac.
Additional methods
When other MFA methods are set up in the Identity Platform, end users could see the following.
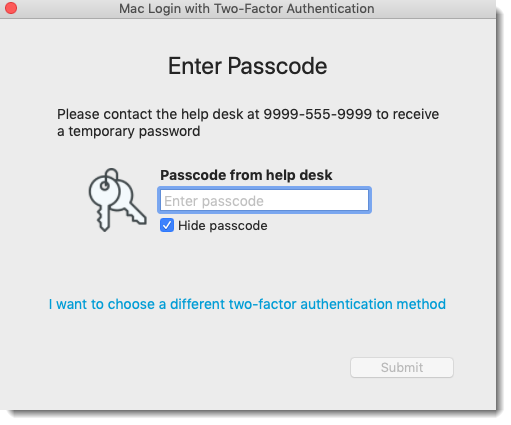
Contact the help desk
When selecting this option, the Enter Passcode window appears. (The phone number in the image below is an example only.)
If more than one phone number displays for the help desk, select the phone number to use for contacting the help desk.
Input the passcode supplied by the help desk.
Click Submit to log on the Mac.
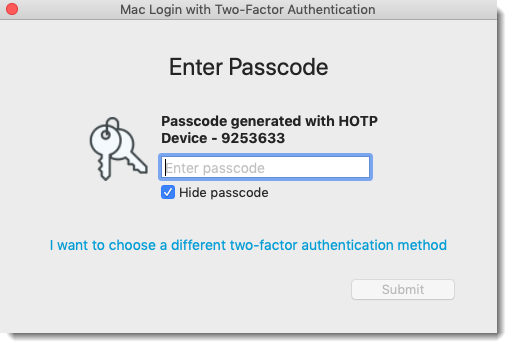
Enter passcode from token
This method and "Enter timed passcode from app" are displayed at first login, if available. If not available, all available methods are displayed.
When selecting this option, the Enter Passcode window appears.
With the YubiKey HOTP device inserted in the machine, tap or press the device to populate the passcode in the field.
Click Submit to log on the Mac.
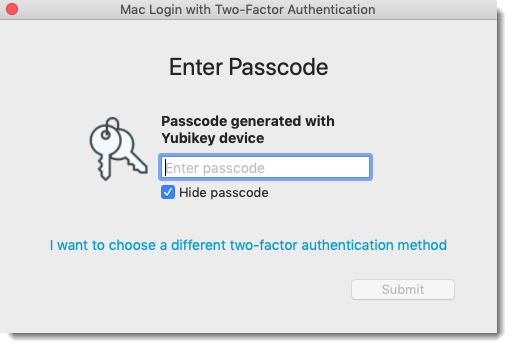
Enter passcode from YubiKey (Yubico OTP protocol)
When selecting this option, the Enter Passcode window appears.
With the YubiKey OTP device (Yubico OTP protocol) inserted in the machine, tap or press the device to populate the passcode in the field.
Click Submit to log on the Mac.
Enter passcode from YubiKey
When selecting this option, the Enter Passcode window appears.
With the YubiKey OATH-TOTP device inserted in the machine, tap or press the device to populate the passcode in the field.
Click Submit to log on the Mac.
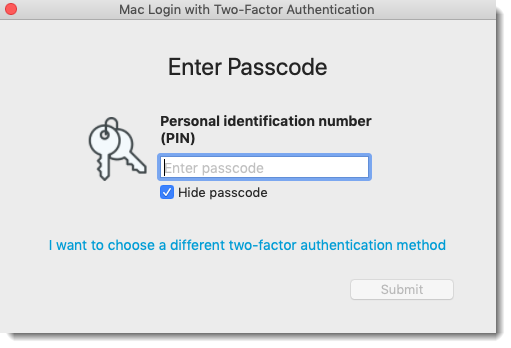
Enter PIN
When selecting this option, the Enter Passcode window appears.
Enter your predefined personal identification number (PIN).
Click Submit to log on the Mac.
Enter answers to Security Questions
When selecting this option, the Answer Security Questions window appears.
Answer both questions with your predefined answers. You must answer both questions.
Click Submit to log on the Mac.