FIDO2 WebAuthn global MFA settings
You can allow users to register their FIDO2 authenticators as a login multi-factor authentication (MFA) option. Set how many devices users can register and whether users can remove their own devices. For FIDO2 authenticators, you can require user verification for device registration and authentication.
Note
FIDO2 authenticators could be known as external security keys or built into devices like phones and laptops. In the Identity Platform UI, the term device is interchangeable to mean either device or security key.
When you configure and save the global settings for FIDO2, it automatically generates a FIDO2 registration and management page.
Note
The FIDO2 registration and authentication web page for your end users requires HTTPS in the URL.
The FIDO2 registration and management page is localized and translated based on the user's browser language settings.
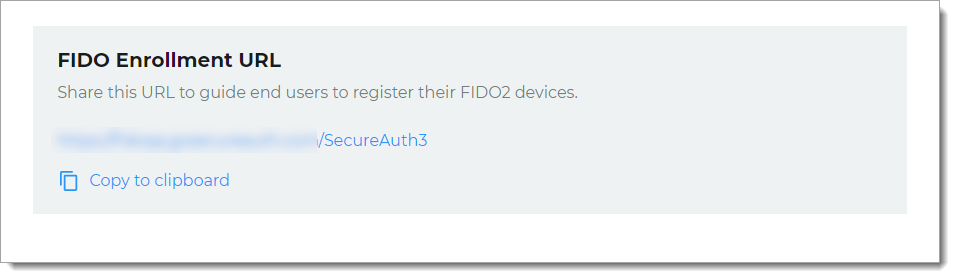
To guide end users to register their devices as FIDO authenticators, share the FIDO2 registration page URL. Once end users register their device on that page, it becomes available as a FIDO2 login option to authenticate their access to resources.
Enable FIDO2 devices
Follow these steps to enable FIDO2 devices in the SecureAuth® Identity Platform New Experience.
On the left side of the Identity Platform page, click Multi-Factor Methods.
Click the pencil icon for FIDO2 (WebAuthn).
The configuration page for FIDO2 (WebAuthn) appears.
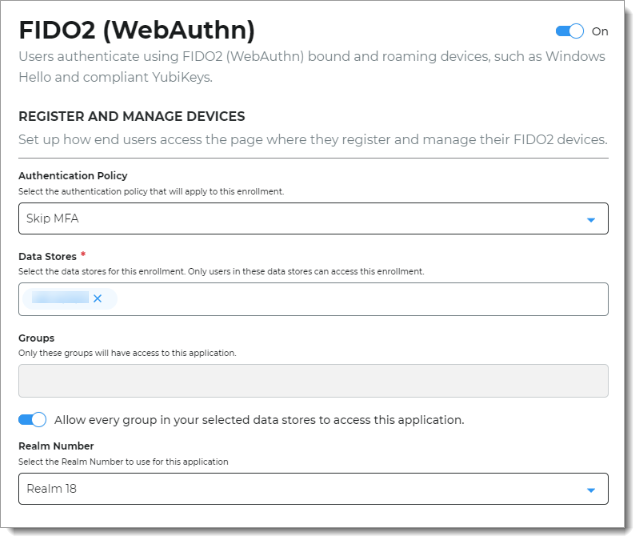
In the Register and Manage Devices section, set the following configurations.
Authentication Policy
Select the login authentication policy for the FIDO2 registration page.
The authentication policy includes the login workflow to register the FIDO2 device.
Data Stores
Enter the data stores to to authenticate and allow user access to register their FIDO2 device. Start typing to bring up a list of data store names. You can enter more than one data store.
Groups
Use one of the following options:
Slider in the On position (enabled): Allow users from every group in your selected data stores access to this FIDO2 registration page.
Slider in the Off position (disabled): Enter the specific groups who are allowed access to this FIDO2 registration page.
Realm Number
Select the Realm Number to use for this application.
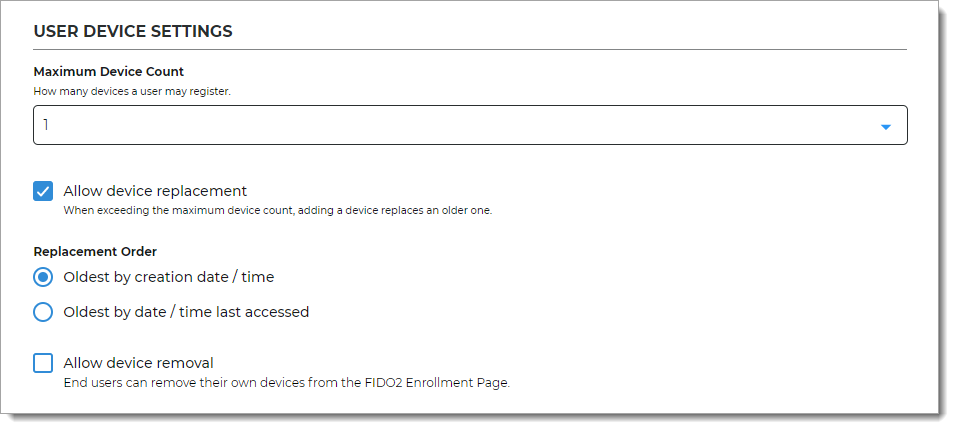
In the User Device Settings section, set the following configurations.
Maximum Device Count
Set how many FIDO2-enabled devices a user can register.
Valid values are Unlimited, 1, 5, and 10.
Allow device replacement
Set whether to allow replacement of a device when the user has reached the maximum number of registered devices.
The next admin setting determines which device to replace. This information is not displayed to the end user; they are only prompted to replace a device.
Replacement Order
This option is active only when the Allow device replacement option is selected. Choose which device to automatically replace:
Oldest by creation date/ time - the last time the user registered the device
Oldest by date time last accessed - the last time the device was used in the system
Allow device removal
Set whether to allow users to remove their own device from the FIDO2 registration and management page.
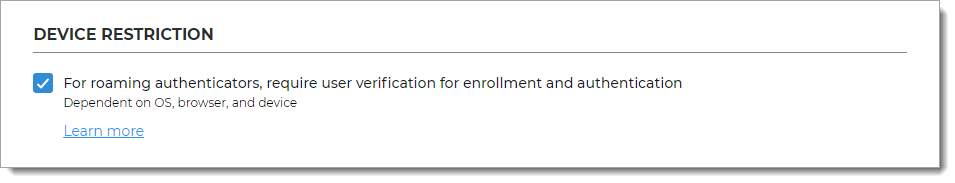
In the Device Restriction section, set whether users must provide verification (for example, PIN) for enrollment and verification while using a FIDO2 authenticator, like a security key or mobile device.
Note
Some browsers and operating systems might not have PIN support for FIDO2 authenticators. To learn more, see Admin troubleshooting PIN support for FIDO2 WebAuthn.
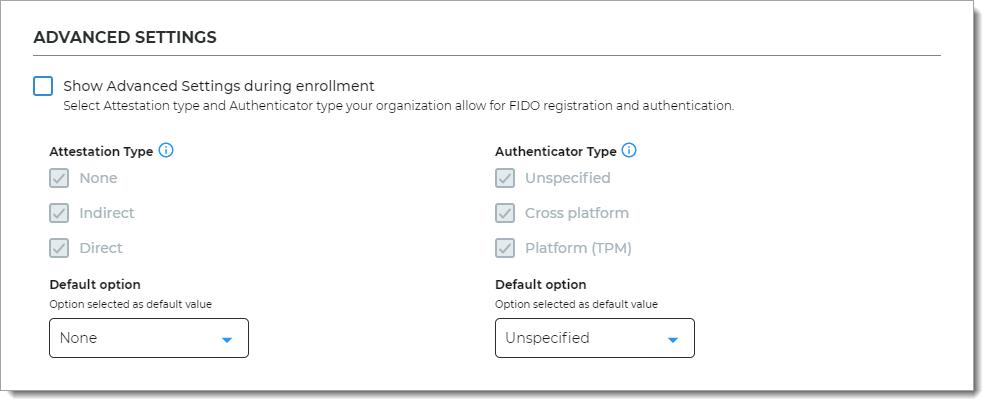
In the Advanced Settings section, set whether to allow registration of any FIDO2 authenticator by default. Or, you can limit registrations to certain FIDO2 authenticator types.
Show Advanced Settings during enrollment
Indicate whether to show the Advanced Settings during enrollment of the FIDO2 authenticator.
Use this setting only for end users who understand the FIDO2 WebAuthn specifications. Otherwise, the default settings are correct for most users.
Attestation Type
Attestation type is a FIDO protocol that sends identifying data about the device model.
None. Do not sent authenticator data to the server. (Default setting)
Indirect. Requires user consent. Send anonymized authenticator data to the server.
Direct. Requires user consent. Send authenticator data to the server.
Authenticator Type
Authenticator type enables you to allow or restrict certain authenticator types.
Unspecified. Allow all authenticator types like built-in biometric readers and separate (roaming) security keys. (Default setting)
Cross platform. Allow only separate (roaming) authenticators like smartphones and security keys (like YubiKey, Titan Security Key, etc.)
Platform (TPM). Allow only built-in (bound) authenticators on the same device like Touch ID, Face ID, and Windows Hello.
Default option
Recommended default settings are:
Attestation Type – None
Authenticator Type – Unspecified
If you change the default settings, take note of the following:
It will allow registration of new devices only to the selected Authenticator Type. Users with existing devices in this category can still authenticate.
It will block all existing devices that do not belong to the selected Authenticator Type. Users with existing devices in this category will not be able to authenticate.
Click Save.
This creates the FIDO2 registration page and provides the registration URL. Share this URL with your end users to register and manage their FIDO2 devices.
Note
If you turn off FIDO2 as a login method, it prevents end users from seeing it as an MFA choice during login. The FIDO2 Enrollment URL page stays active for end users to manage their FIDO2 devices.
Enable FIDO2 devices in the Advanced Settings
You can enable FIDO2 WebAuthn as authenticators for logins to realms created in the Identity Platform Advanced Settings (formerly Classic Experience).
Follow these instructions:
In the Advanced Settings, select the Multi-Factor Methods tab.
In the Multi-Factor Configuration > FIDO2 (WebAuthn) Settings section, set the following:
FIDO2 Devices
Set to Enabled.
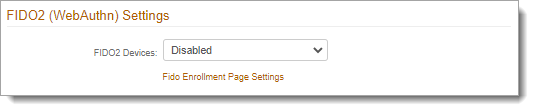
To continue with the FIDO2 enrollment page configuration, click the Fido Enrollment Page Settings link.
You will be redirected to the FIDO2 (WebAuthn) settings page in the New Experience.
Next steps
Configure a policy to use FIDO2 authenticators as MFA in the login workflow. See Policy configuration - Multi-factor methods.
Copy and share the FIDO2 Enrollment URL with your end users. For example, to encourage end users to register their FIDO2 devices, customize the "Passwordless with FIDO2" setup instructions available in the SecureAuth Onboarding Toolkit.
Note
The FIDO2 registration and authentication web page for your end users requires HTTPS in the URL.