Pulse Secure Virtual Hostname configuration guide
Introduction
Use this guide to configure a Pulse Secure VPN Virtual Hostname.
Pulse Secure has the ability to provide the Network Address Translation in the form of a proxy service from the Internet to the private network. A new public name can be configured as a Virtual Hostname, which will allow Pulse Secure to forward traffic sent from the Internet to a public hostname, and then to a host that would normally be unavailable from the Internet.
Additionally, Pulse Secure provides the SSL service for SecureAuth IdP, which is very convenient when a wildcard SSL certificate is installed on Pulse Secure. This also creates the possibility of passing traffic from Pulse Secure to SecureAuth IdP via HTTP or HTTPS. Some organizations use advanced inspection tools and techniques, and prefer traffic on the private network to be unencrypted, which can be accomplished in this manner.
Prerequisites
Pulse Secure VPN installed and running
Pulse Secure configuration steps
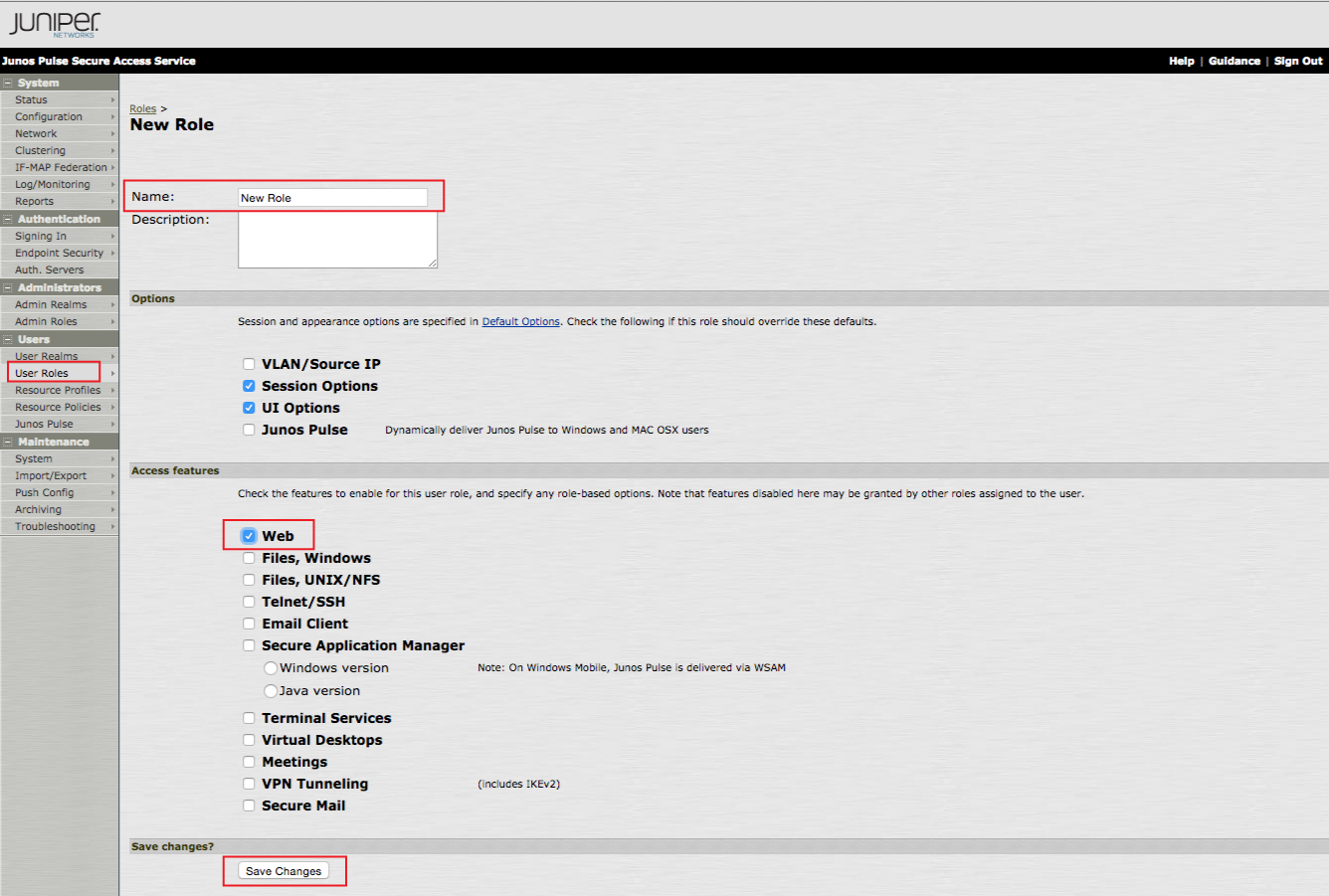
User Role configuration
1. Log on the Pulse Secure admin console, and select User Roles under Users, and click New User Role...
2. Set a Name for the new role.
3. Select Web in the Access Features section.
4. Click Save Changes.
 |
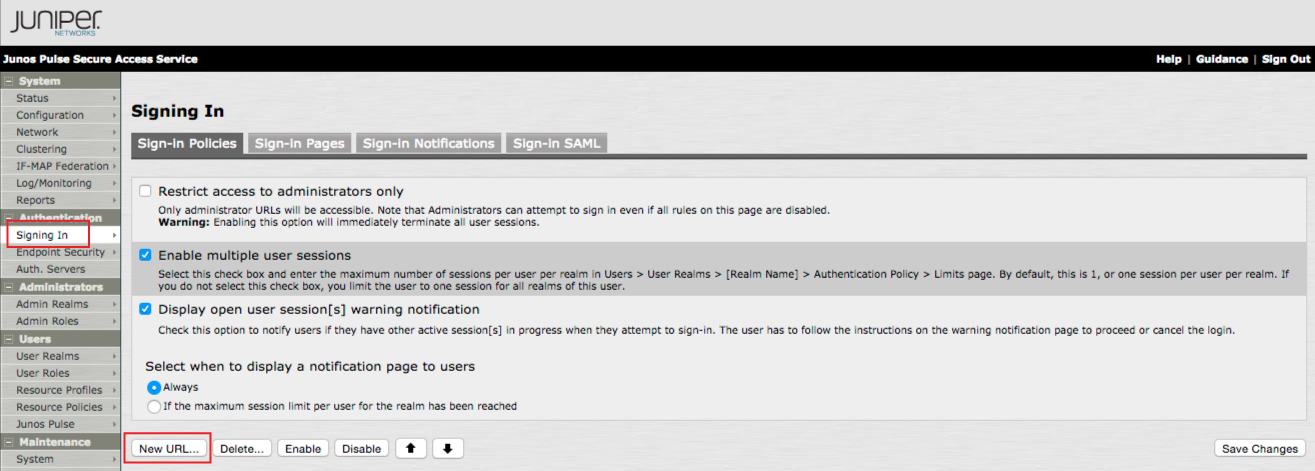
Sign-in Policy configuration
5. On the admin console, select Signing In under Authentication, and click Sign-in Policies.
6. Click New URL... to create the new Signing-in Policy.
 |
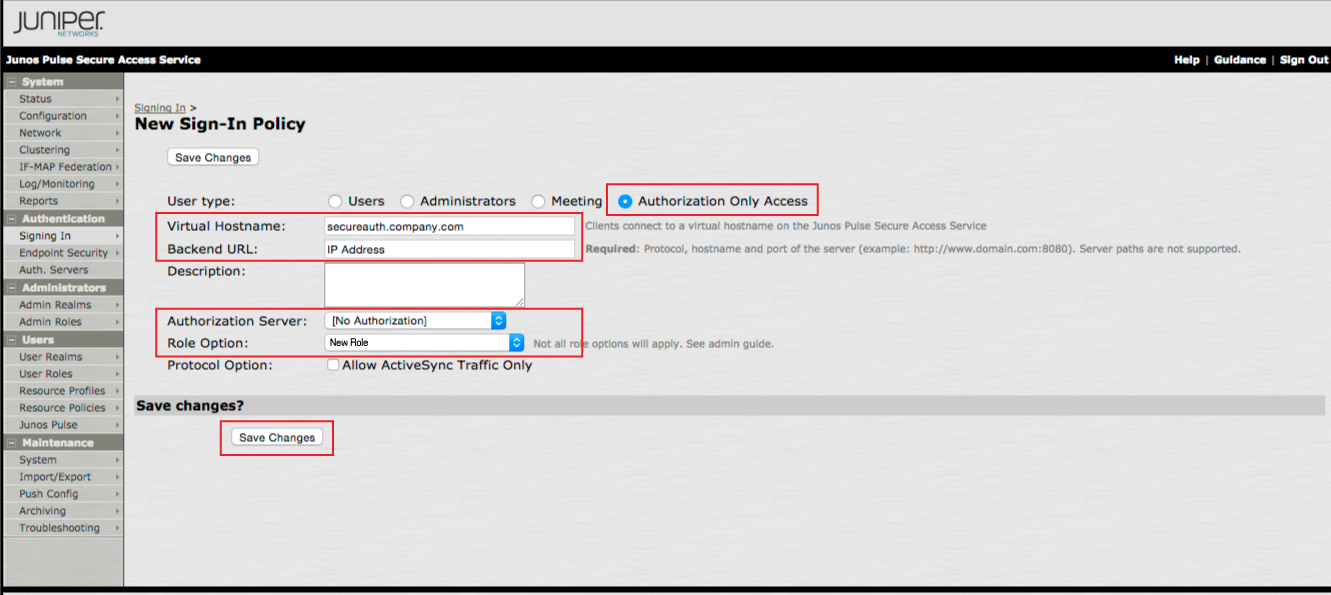
7. Select Authorization Only Access from the User type options.
8. Set the Virtual Hostname to the FQDN of the SecureAuth IdP appliance
e.g. https://secureauth.company.com
9. Set the Backend URL to the internal hostname or IP Address of the SecureAuth IdP appliance.
10. Select [No Authorization] from the Authorization Server dropdown.
11. Select the New Role (created in the previous steps) from the Role Option dropdown.
12. Click Save Changes.
 |
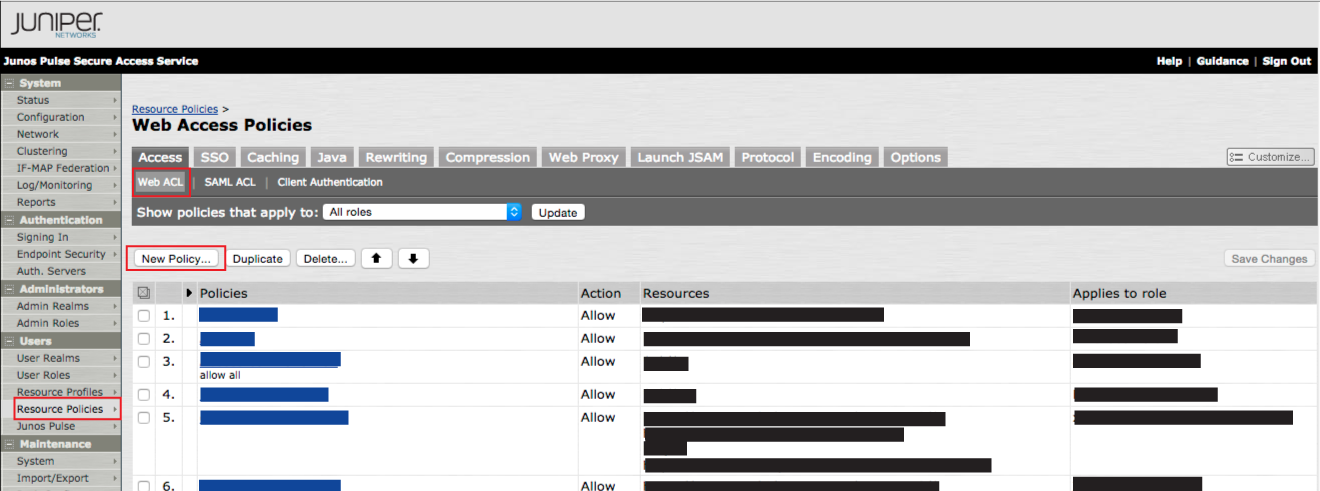
Resource Policy to Allow access to SecureAuth IdP configuration
13. On the admin console, select Resource Policies under Users, and click Web ACL.
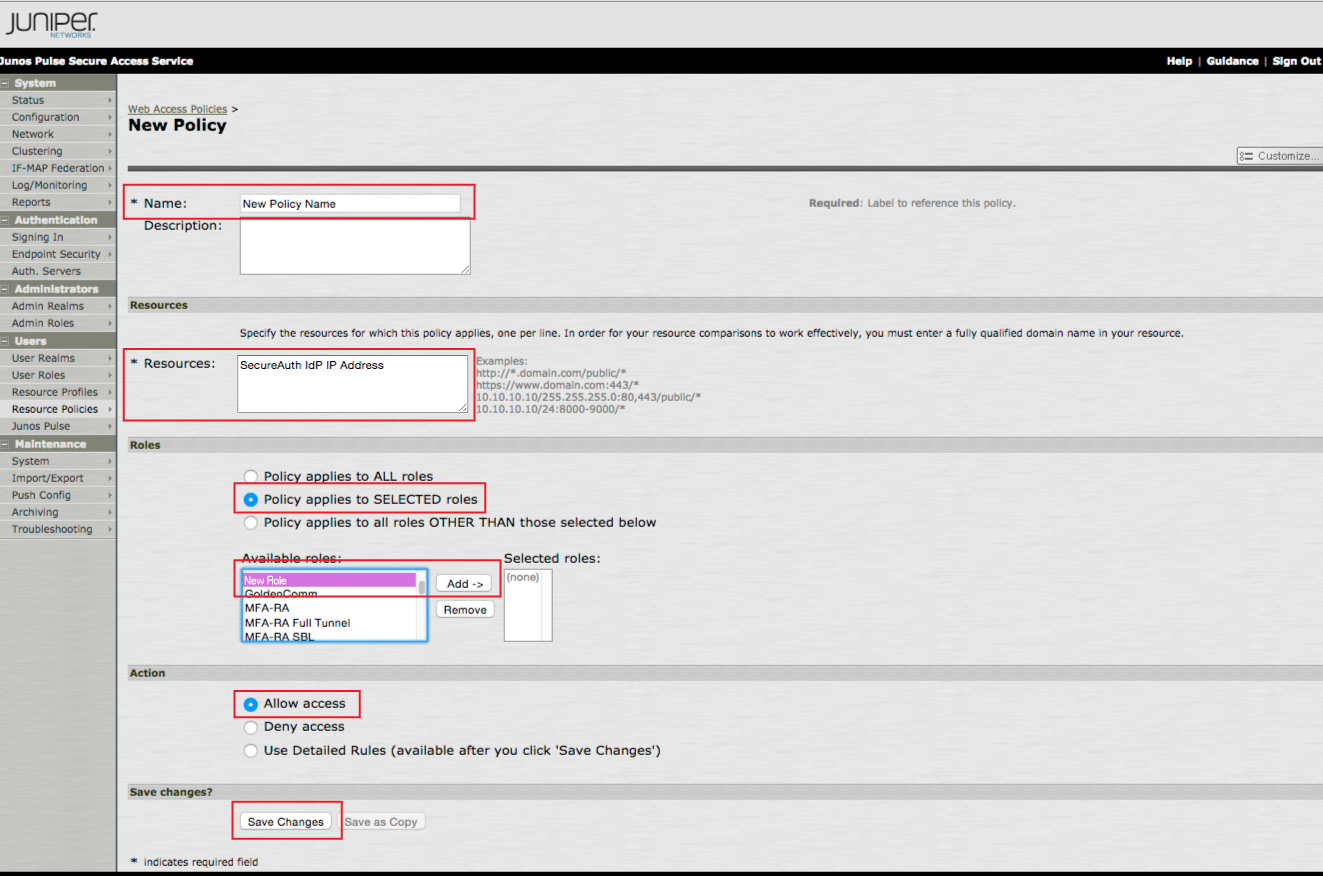
14. Click New Policy... to create a new Policy.
 |
15. Set a Name for the new policy.
16. Provide the SecureAuth IdP server IP Address in the Resources field.
17. Select Policy apples to SELECTED roles in the Roles section.
18. Select the New Role created in the previous steps, and click Add.
19 Select Allow access in the Action section.
20. Click Save Changes.
 |