Ultipro (SP-initiated) Integration Guide
Introduction
Use this guide to enable Multi-Factor Authentication and Single Sign-on (SSO) access via SAML to Ultipro using AD FS 2.0.
Prerequisites
1. Have an Ultipro account with AD FS 2.0
2. Create a New Realm for the Ultipro integration in the SecureAuth IdP Web Admin
3. Configure the following tabs in the Web Admin before configuring the Post Authentication tab:
Overview – the description of the realm and SMTP connections must be defined
Data – an enterprise directory must be integrated with SecureAuth IdP
Workflow – the way in which users will access this application must be defined
Multi-Factor Methods – the Multi-Factor Authentication methods that will be used to access this page (if any) must be defined
SecureAuth IdP Configuration Steps
Data
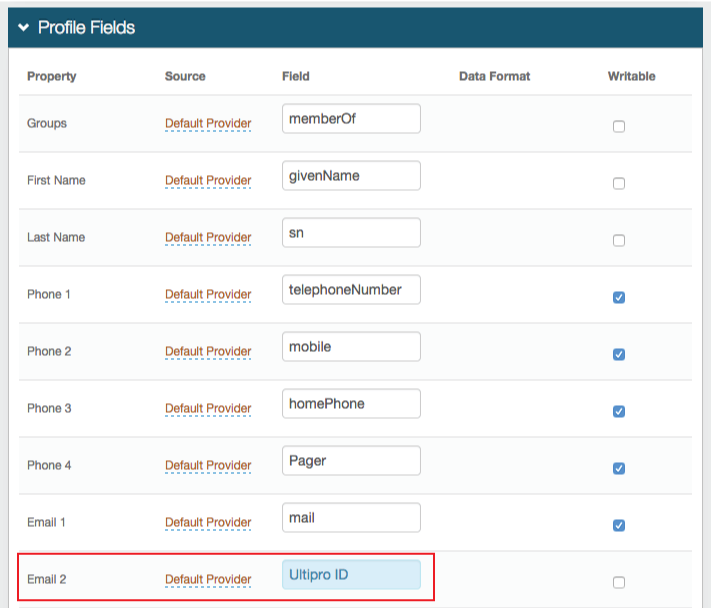 |
1. In the Profile Fields section, map the directory field that contains the user's Ultipro ID to the SecureAuth IdP Property
For example, add the Ultipro ID Field to the Email 2 Property if it is not already contained somewhere else
Warning
Click Save once the configurations have been completed and before leaving the Data page to avoid losing changes
Post Authentication
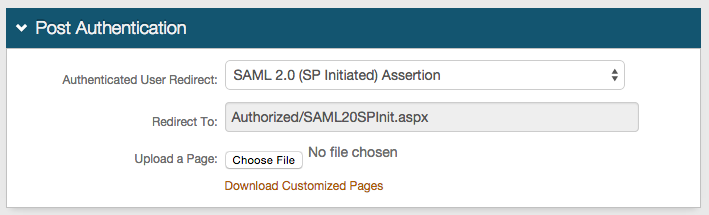 |
2. Select SAML 2.0 (SP Initiated) Assertion Page from the Authenticated User Redirect dropdown in the Post Authentication tab in the Web Admin
3. An unalterable URL will be auto-populated in the Redirect To field, which will append to the domain name and realm number in the address bar (Authorized/SAML20SPInit.aspx)
4. A customized post authentication page can be uploaded, but it is not required
User ID Mapping
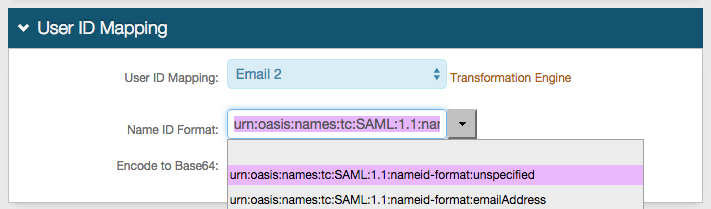 |
5. Select the SecureAuth IdP Property that corresponds to the directory field that contains the Ultipro ID (Email 2)
6. Select urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified from the Name ID Format dropdown (default)
Select a different option if Ultipro requires it, which the Service Provider (SP) will provide
7. Select False from the Encode to Base64 dropdown
SAML Assertion / WS Federation
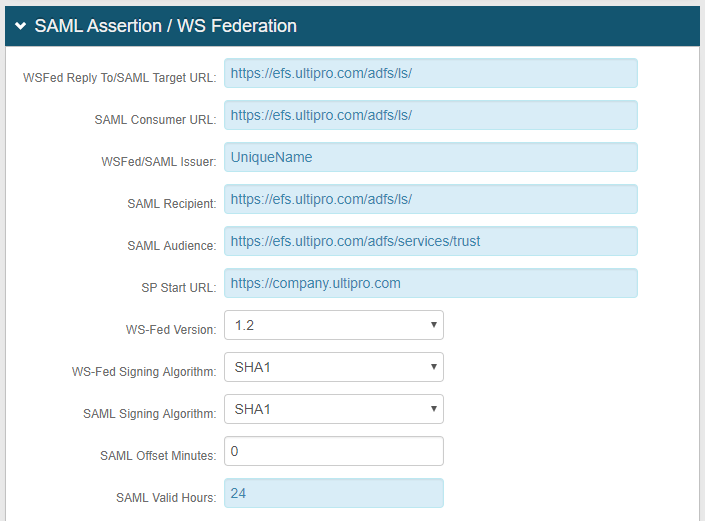 |
8. Set the WSFed Reply To/SAML Target URL to https://efs.ultipro.com/adfs/ls/
9. Set the SAML Consumer URL to https://efs.ultipro.com/adfs/ls/
10. Set the WSFed/SAML Issuer to a Unique Name that will be shared with Ultipro
The WSFed/SAML Issuer must match exactly on the SecureAuth IdP side and the Ultipro side
11. Set the SAML Recipient to https://efs.ultipro.com/adfs/ls/
12. Set the SAML Audience to https://efs.ultipro.com/adfs/services/trust
13. Provide the SP Start URL to enable SSO and to redirect users appropriately to access Ultipro
For example, the SP Start URL would be https://company.ultipro.com
14. Set the SAML Offset Minutes to make up for time differences between devices
15. Set the SAML Valid Hours to limit for how long the SAML assertion is valid
 |
16. Leave the Signing Cert Serial Number as the default value, unless there is a third-party certificate being used for the SAML assertion
If using a third-party certificate, click Select Certificate and choose the appropriate certificate
17. Download the Assertion Signing Certificate, which will be used in the Ultipro Configuration Steps
Warning
Click Save once the configurations have been completed and before leaving the Post Authentication page to avoid losing changes
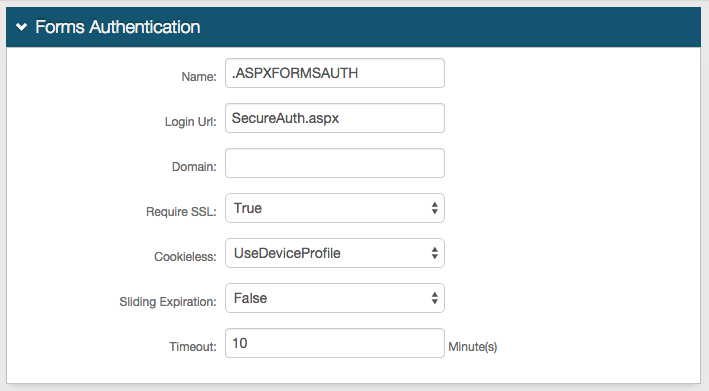
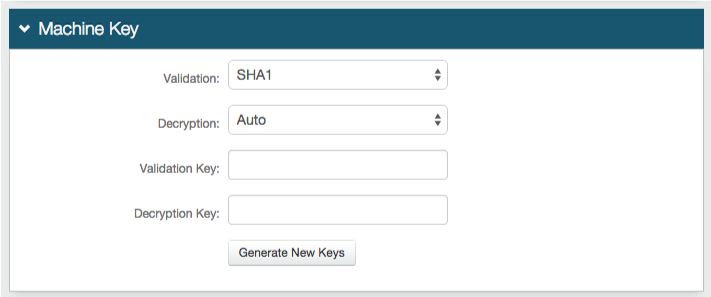
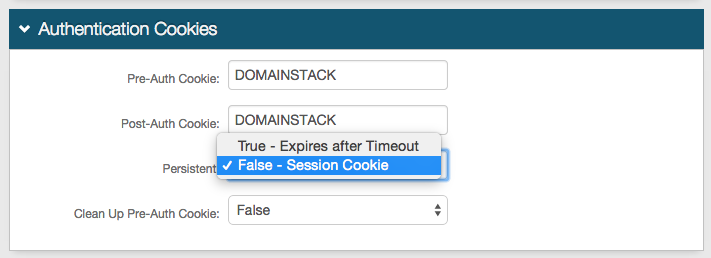
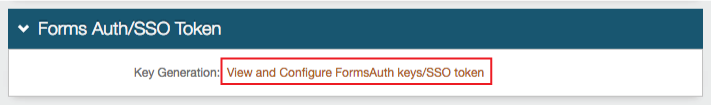
Forms Auth / SSO Token
Optionally, in the Forms Auth / SSO Token section, click the View and Configure FormsAuth keys/SSO token link to configure the token/cookie settings and configure this realm for SSO.
 |
Ultipro Configuration Steps
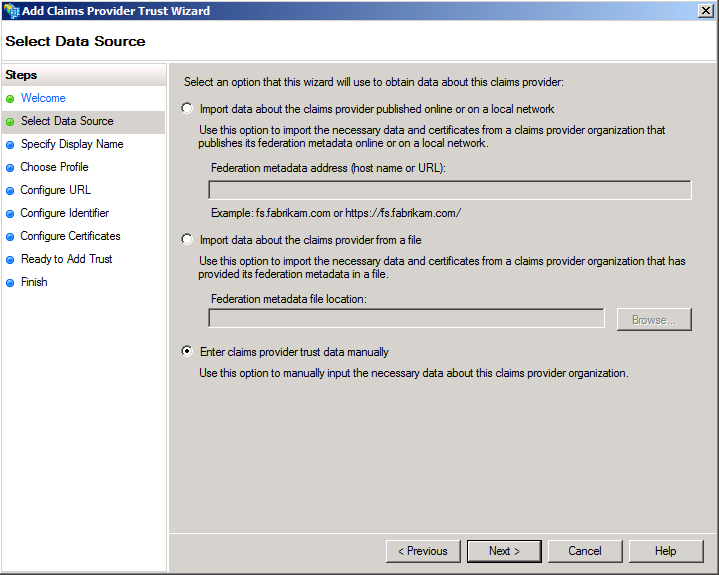
Set up AD FS 2.0 with Claims Provider Trust
1. To set up AD FS 2.0 with a Claims Provider Trust, open the Claims Provider Trust Wizard
2. In the Select Data Source section, select Enter claims provider trust data manually from the options, and click Next
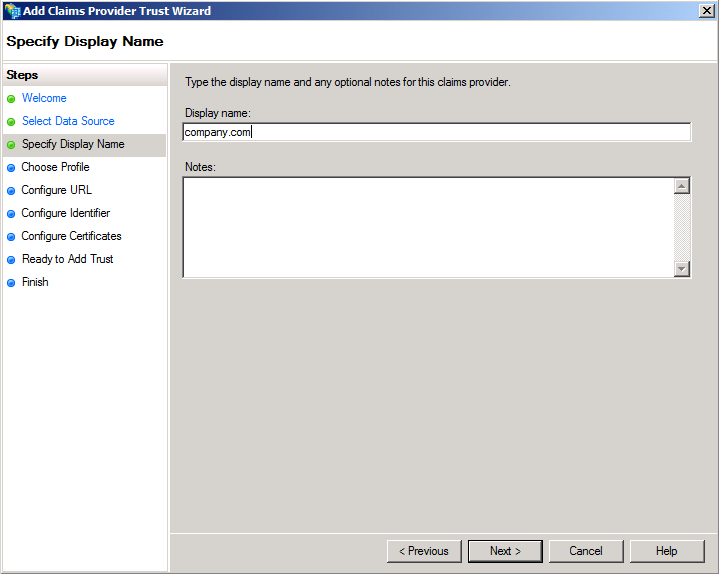
3. In the Specify Display Name section, provide a Display Name, and click Next
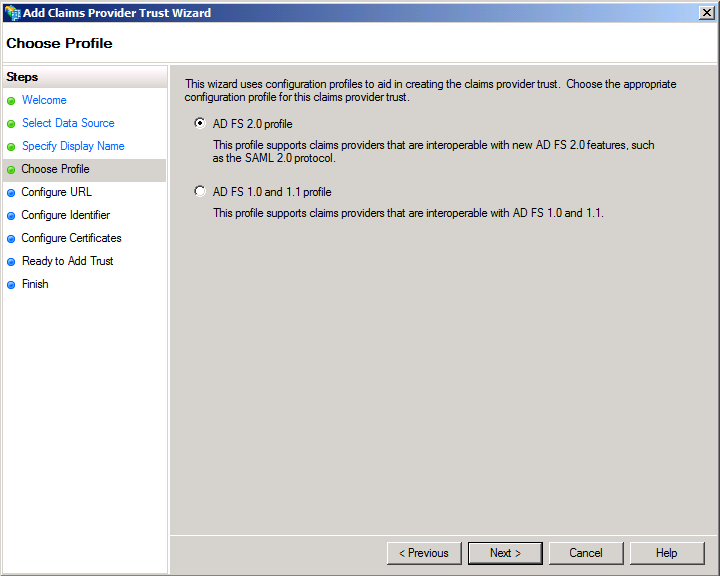
4. In the Choose Profile section, select AD FS 2.0 profile from the options, and click Next
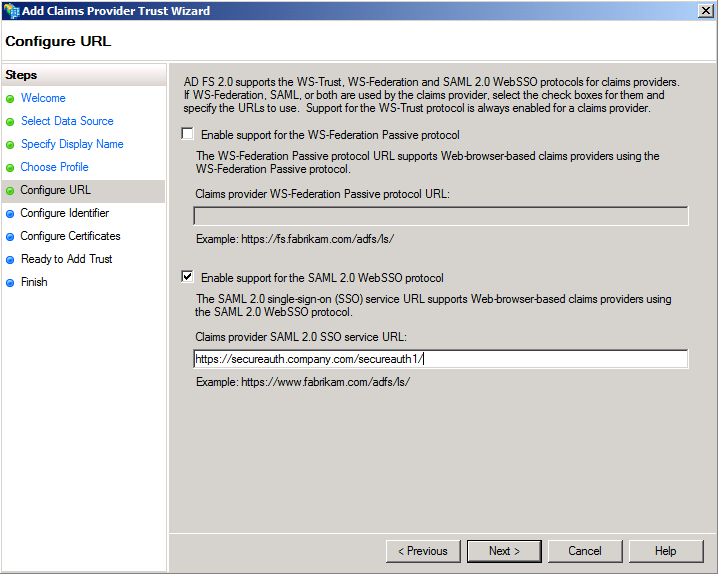
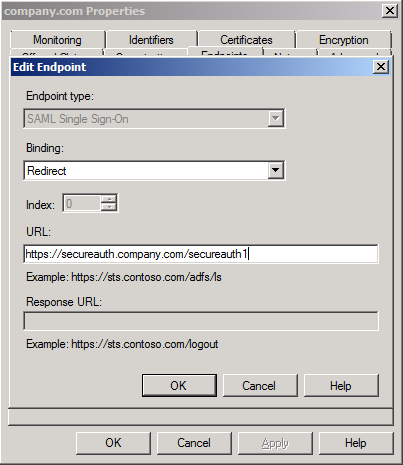
5. In the Configure URL section, check Enable support for the SAML 2.0 WebSSO protocol; set the Claims provider SAML 2.0 SSO service URL to the Fully Qualified Domain Name (FQDN) of the SecureAuth IdP appliance, followed by the SecureAuth IdP Ultipro-integrated realm (e.g. https://secureauth.company.com/secureauth1/); and click Next
Note
Make sure to include the trailing slash "/" at the end of the URL to avoid IIS errors
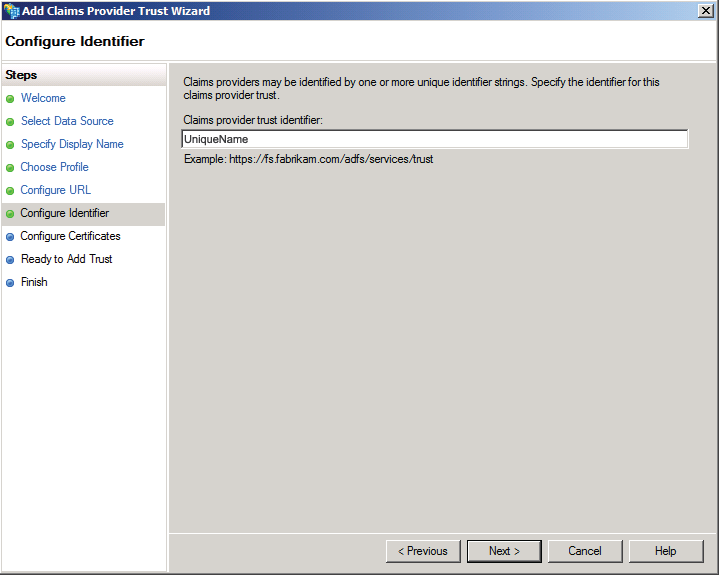
6. In the Configure Identifier section, set the Claims provider trust identifier to the same Unique Name established in the WSFed/SAML Issuer field in the SecureAuth IdP Web Admin (step 10), and click Next
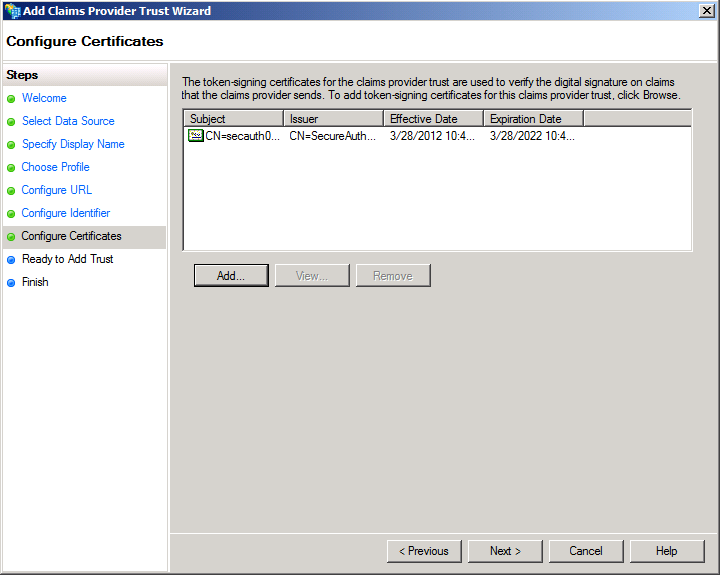
7. In the Configure Certificates section, click Add to upload the Assertion Signing Certificate from the SecureAuth IdP Web Admin (step 17), and click Next
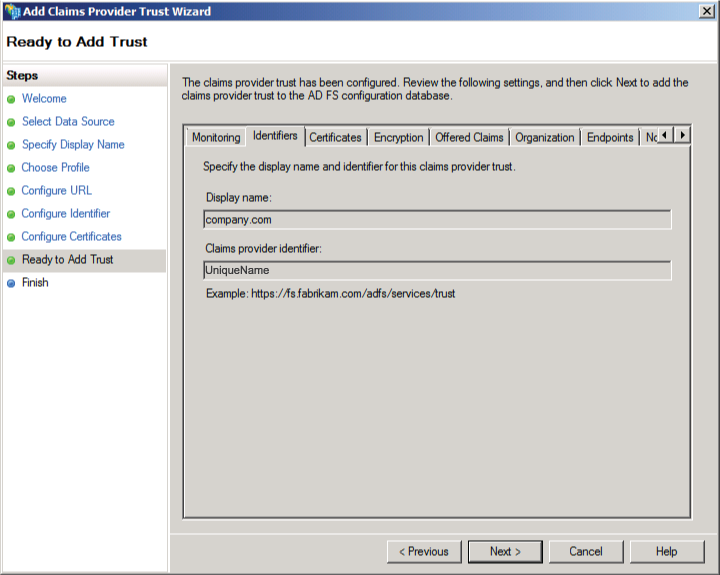
8. In the Ready to Add Trust section, verify that the settings are correct, and click Next
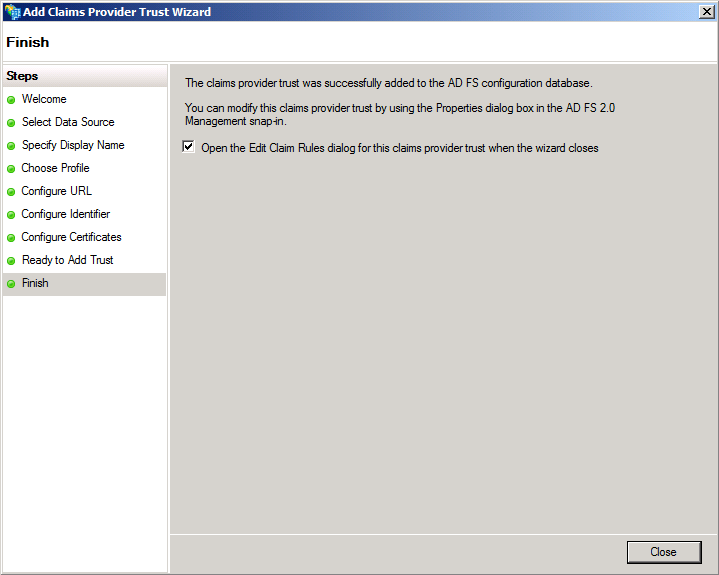
9. In the Finish section, click Close to complete the wizard
AD FS 2.0 Management Console
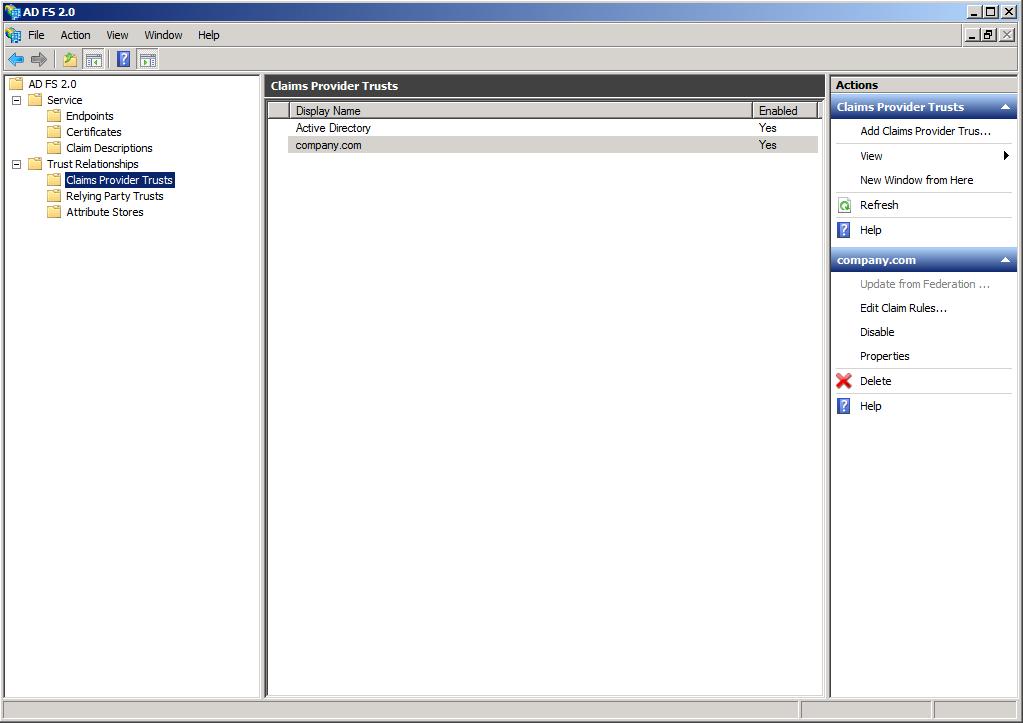 |
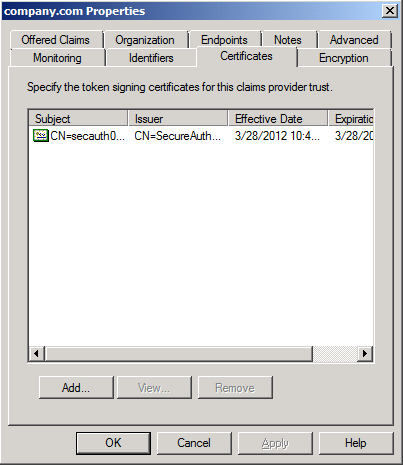
10. Open the AD FS 2.0 Management Console, and browse to the new Claims Provider Trust
11. Open it and verify the settings
Specifically:
In the Identifiers tab, the Claims provider identifier must match the WSFed/SAML Issuer value in the SecureAuth IdP Web Admin (step 10)
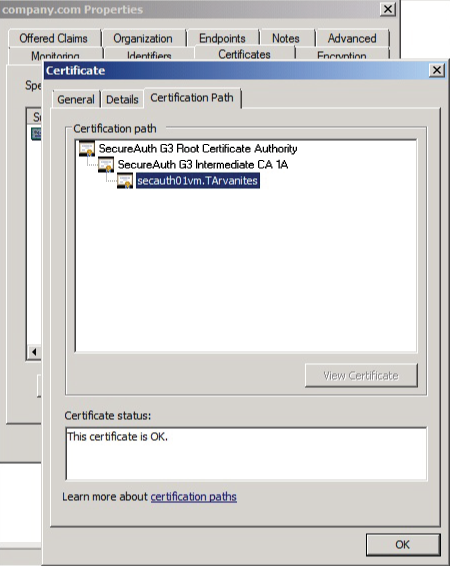
In the Certificates tab, the Assertion Signing Certificate from the SecureAuth IdP Web Admin (step 17) should be present and show trust all the way up to the root
Note
Downloading and installing the root certificates into the AD FS 2.0 server certificate store may be required
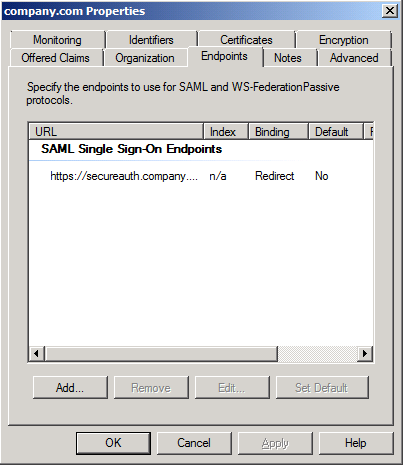
In the Endpoints tab, the SAML Single Sign-On Endpoints must point to the SecureAuth IdP Ultipro-integrated realm (https://secureauth.company.com/secureauth1/), and it must be a SAML Redirect endpoint
In the Advanced tab, the Secure hash algorithm must be SHA-2
SecureAuth IdP 8.1+ appliances or pre-8.1 appliances that have run the ACRU utilize SHA-2 SSL certificates; if using a SHA-1 certificate from a third-party provider, select SHA-1 from the dropdown
Note
In the General section of the Certificate window, the type of certificate is expressed
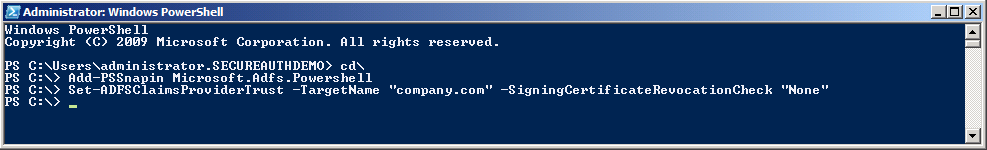
Avoid ID4037 Error
To avoid the ID4037 error in AD FS 2.0 that hinders the communication from working due to not being able to check the SecureAuth IdP SSL certificate against a CRL, run the following commands from a Windows PowerShell window on the AD FS 2.0 server:
Add-PSSnapin Microsoft.Adfs.Powershell
Set-ADFSClaimsProviderTrust -TargetName "company.com" -SigningCertificateRevocationCheck "None"
Note
Be sure to replace the company.com value with the actual Display Name created in step 3 of the Ultipro Configuration Steps
Click here for more information