Cisco iOS Provisioning Integration Guide (Certificate)
Introduction
Use this guide to enable the provisioning of and certificate delivery to end-users' iOS devices to include Cisco VPN settings applied to the device(s) without manual input and to conduct Multi-Factor Authentication.
Settings that are delivered in a profile are bound together and cannot be removed in part by the end-user, creating front-end protection with a device PIN or passcode and control over the network through the VPN client and associated rules.
Prerequisites
1. Have a Cisco VPN
2. Download the Apple Configurator to create iOS profiles
3. Create a New Realm for the iOS Cisco integration in the SecureAuth IdP Web Admin
4. Configure the following tabs in the Web Admin before configuring the Post Authentication tab:
Overview – the description of the realm and SMTP connections must be defined
Data – an enterprise directory must be integrated with SecureAuth IdP
Workflow – the way in which users will access this application must be defined
Multi-Factor Methods – the Multi-Factor Authentication methods that will be used to access this page (if any) must be defined
iOS Configuration Steps
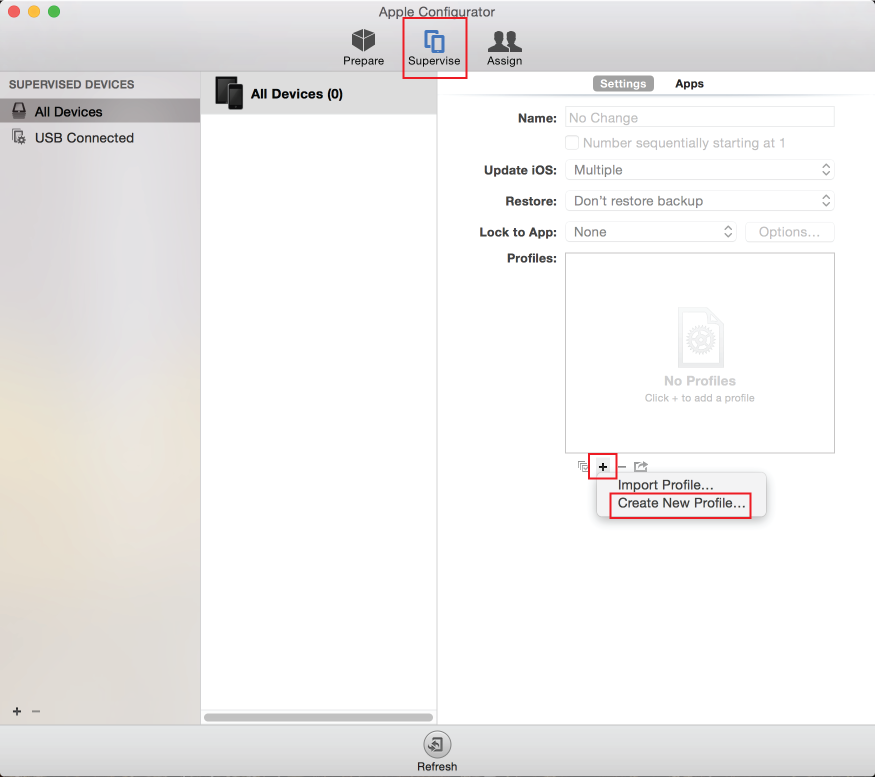 |
1. Download the Apple Configurator from Apple
2. In the Supervise section under Settings, click the + button, and select Create New Profile...
General
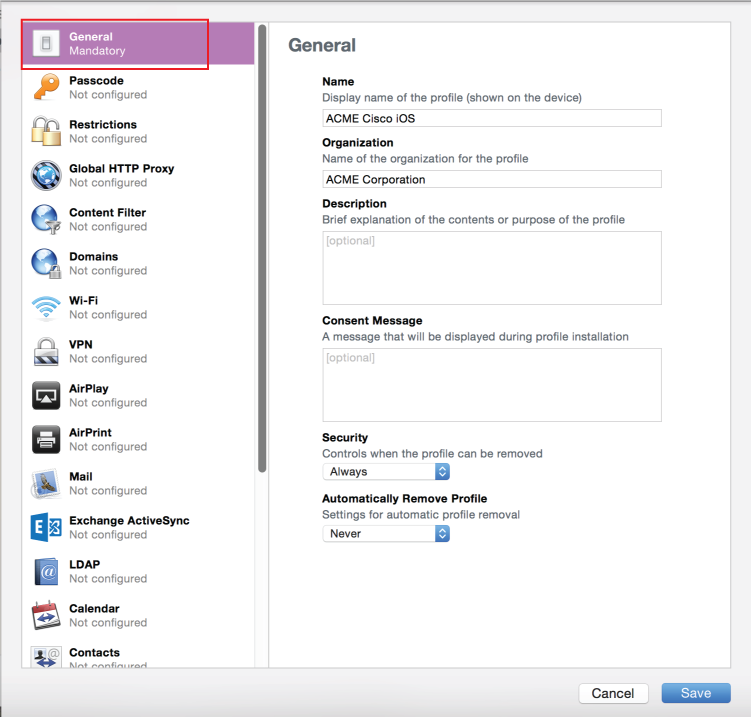 |
3. In the General section, fill out the fields to describe the profile
VPN
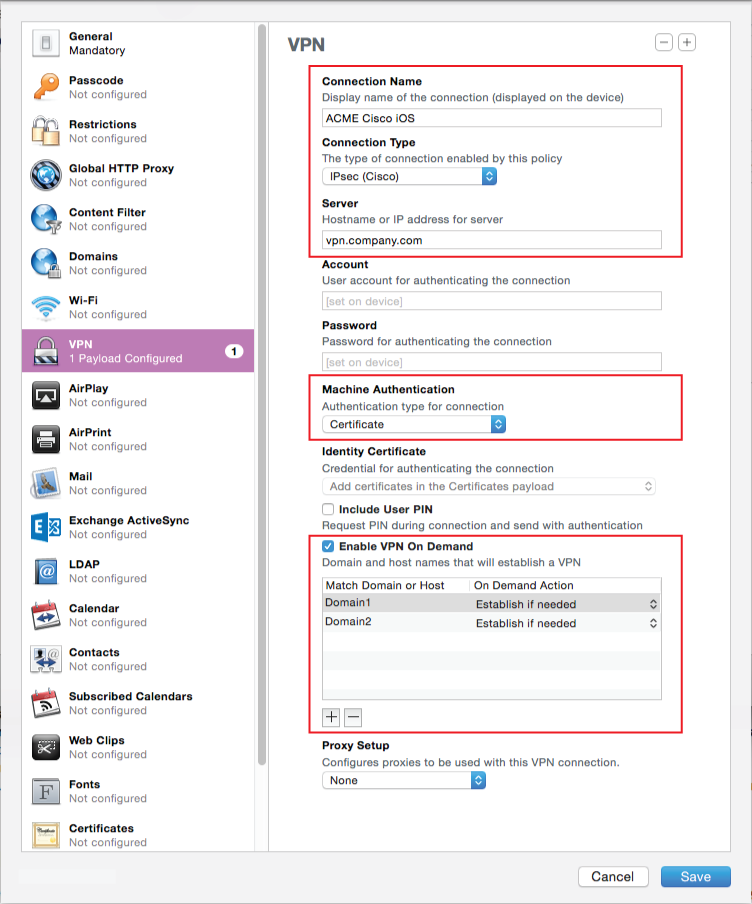 |
4. In the VPN section, provide a Connection Name that displays on the device
5. Select IPsec (Cisco) from the Connection Type dropdown
6. Set the Hostname to the domain or IP address of the Cisco server
7. Select Certificate from the Machine Authentication dropdown
A prompt will appear to upload a certificate, but it is not required
The certificate will be delivered to the device through the SecureAuth IdP workflow
8. (OPTIONAL) Check Enable VPN On Demand to enable instant access to the VPN connection on the device without requiring manual entry or login
9. (OPTIONAL) Click the + button to add a domain or hostname in which VPN On Demand is enabled
10. (OPTIONAL) Edit the Domain or Hostname, and select the On Demand Action
Passcode
Note
Apple encourages more than one payload configuration. A good counterpart to the VPN configuration are the security settings that require a PIN be entered after the phone has been idle for a while.
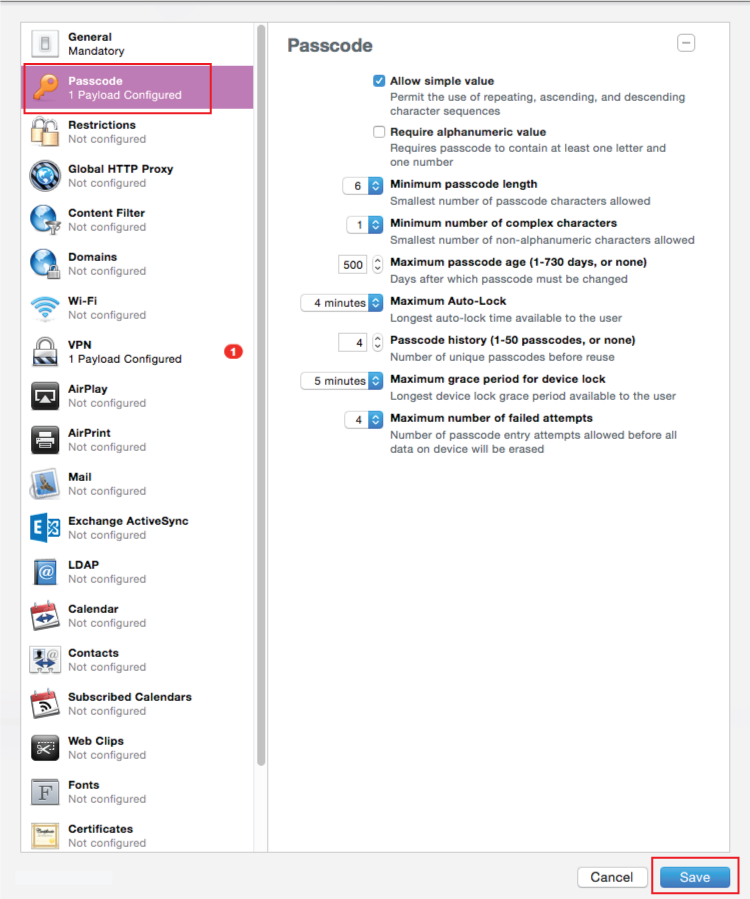 |
11. In the Passcode section, configure preferred requirements for the PIN code applied to idle devices
12. Click Save
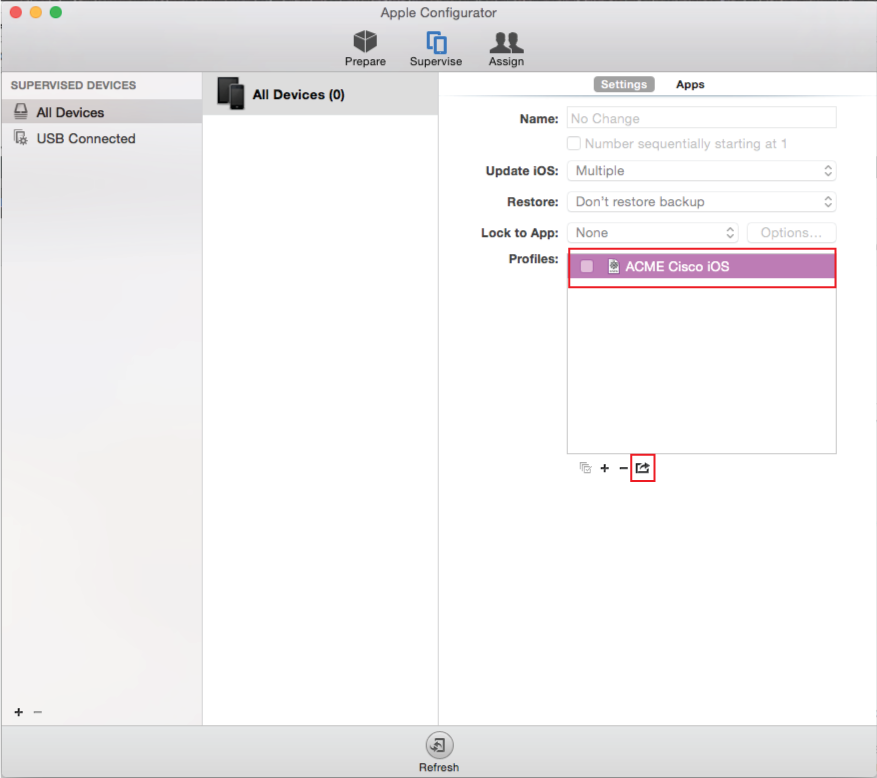 |
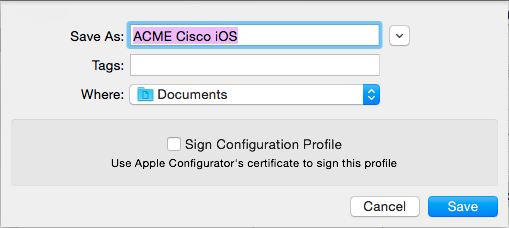
13. Select the new Cisco iOS Profile, and click Export
14. Uncheck Sign Configuration Profile
15. Click Save
SecureAuth IdP Configuration Steps
Post Authentication
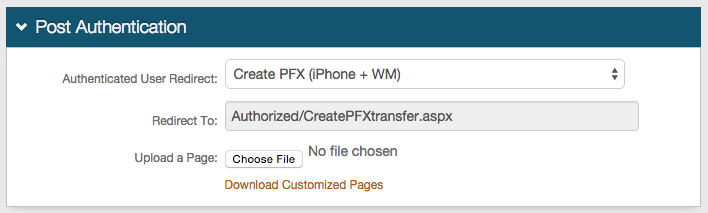 |
1. In the Post Authentication section, select Create PFX (iPhone + VM) from the Authenticated User Redirect dropdown
2. An unalterable URL will be auto-populated in the Redirect To field, which will append to the domain name and realm number in the address bar (Authorized/CreatePFXtransfer.aspx)
3. A customized post authentication page can be uploaded, but it is not required
iPhone / Android
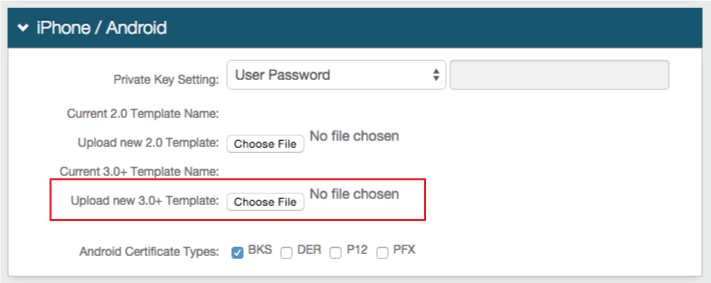 |
4. Select the preferred password method from the Private Key Setting dropdown
5. Click Choose File to Upload new 3.0+ Template, and select the new profile file
Warning
Click Save once the configurations have been completed and before leaving the Post Authentication page to avoid losing changes
Forms Auth / SSO Token
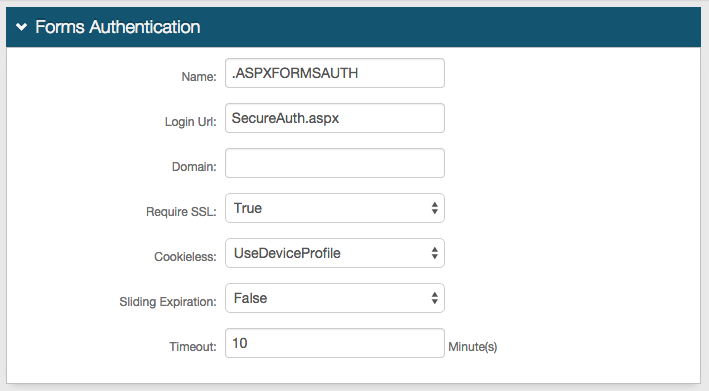
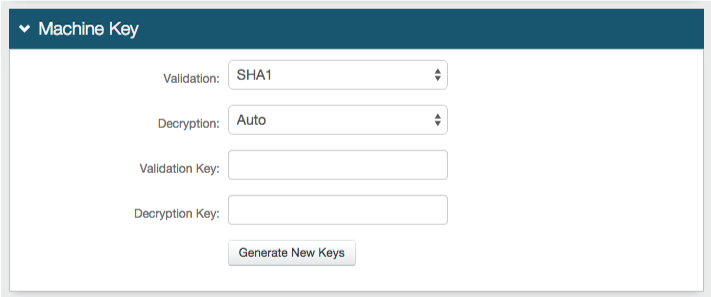
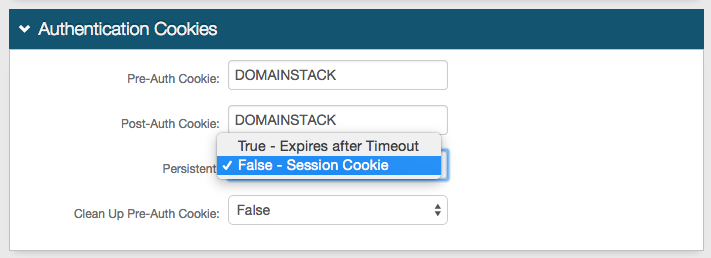
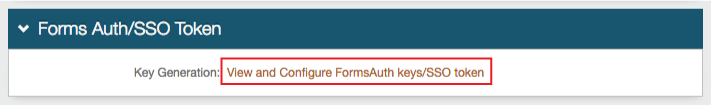
Optionally, in the Forms Auth / SSO Token section, click the View and Configure FormsAuth keys/SSO token link to configure the token/cookie settings and configure this realm for SSO.
 |
Cisco Configuration Steps
Configure the ASA for a typical certificate-based IPSec or AnyConnect tunnel
Apple's VPN On Demand feature works only with certificate-based authentication; but if VPN On Demand is not enabled, Certificate plus AAA can be configured on the Apple Configurator