CyberArk (SP-initiated) Integration Guide (SAML)
Updated 4/1/2020
Use this guide to enable multi-factor authentication and single sign-on (SSO) access via Security-Assertion Markup Language (SAML) to CyberArk.
Prerequisites
Have CyberArk Password Vault Server 9.2.
Create a realm in the SecureAuth IdP version 9.1+ Web Admin for the CyberArk integration.
Configure the following tabs in the Web Admin before configuring the Post Authentication tab:
Overview – Define the description of the realm and SMTP connections.
Data – Integrate an enterprise directory SecureAuth IdP.
Workflow – Define the way that users will access this application.
Multi-Factor Methods – Define the multi-factor authentication methods that will be used to access this page, if any.
SecureAuth IdP configuration steps
1. Log in to your SecureAuth IdP Admin console.
Data
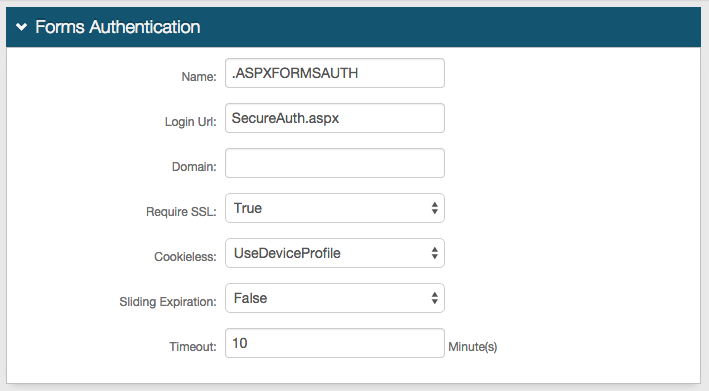
2. Map the directory field that contains the user's CyberArk ID to the SecureAuth IdP property in the Profile Fields section. The following image shows an example of adding the CyberArk ID Field to the Email 2 property.
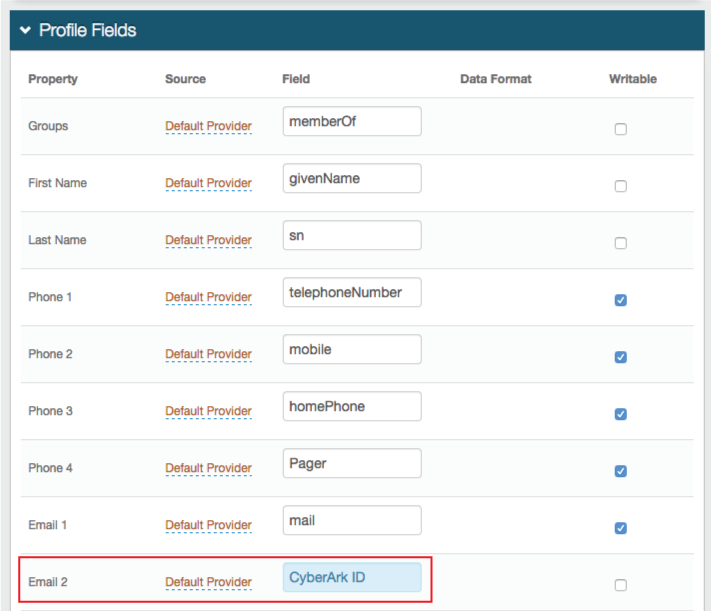 |
3. Save your changes.
Post Authentication
4. In the Post Authentication section, select SAML 2.0 (SP Initiated) Assertion from the Authenticated User Redirect dropdown, as shown in the following image.
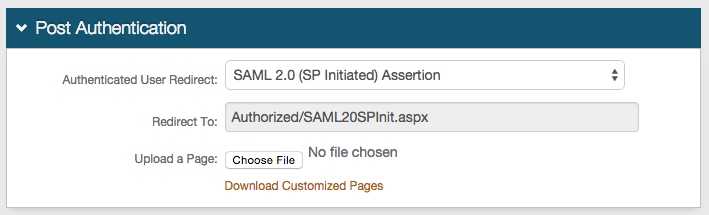 |
An unalterable URL is auto-populated in the Redirect To field, which appends to the domain name and realm number in the address bar (Authorized/SAML20SPInit.aspx).
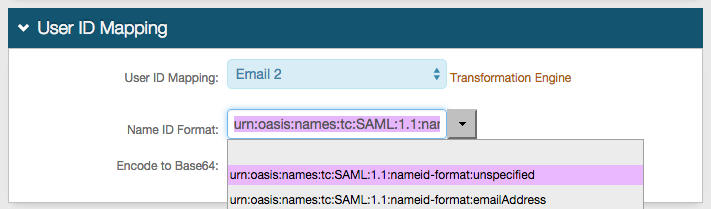
5. In the User ID Mapping section, make the following entries:
a. Select the SecureAuth IdP property that corresponds to the directory field that contains the CyberArk ID (Email 2).
b. Select urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified from the Name ID Format dropdown (default).
Select a different option if CyberArk requires it, which the Service Provider (SP) will provide.
c. Select False from the Encode to Base64 dropdown.
 |
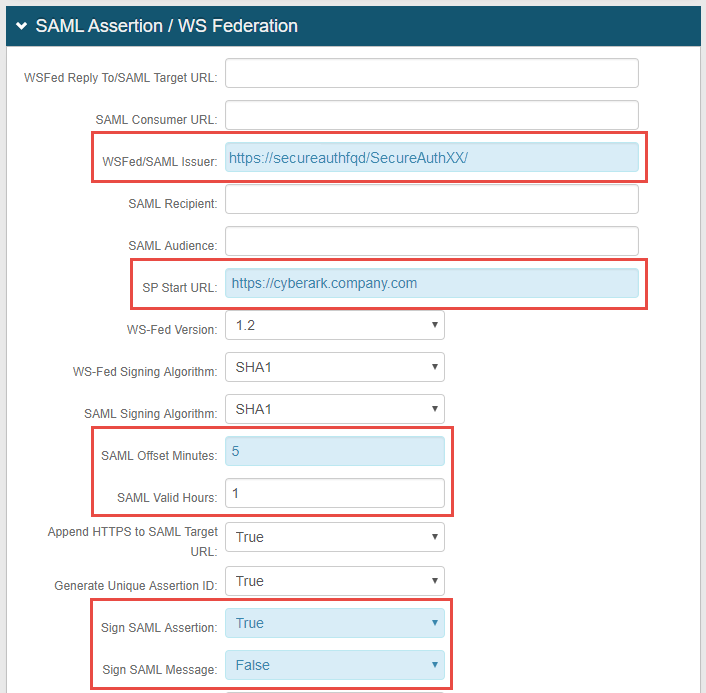
6. In the SAML Assertion / WS Federation section, make the following entries:
a. Set the WSFed/SAML Issuer to a unique name that is shared with CyberArk, for example, the name you use for single sign-on URL, such as https://secureauthfqd/SecureAuthXX/.
The WSFed/SAML Issuer name must match exactly on the SecureAuth IdP side and the CyberArk side.
b. Provide the SP Start URL to enable SSO and to redirect users appropriately to access CyberArk.
An example of the SP Start URL is https://cyberark.company.com.
c. Set the SAML Offset Minutes to 5.
d. Set the SAML Valid Hours to the number of hours during which the SAML assertion is valid, for example, 1 hour.
e. Select True from the Sign SAML Assertion dropdown.
f. Select False from the Sign SAML Message dropdown.
The following image shows example settings for the SAML Assertion / WS Federation section.
 |
Note
No configuration is required for the WSFed Reply To/SAML Target URL, SAML Consumer URL, SAML Recipient, or SAML Audience fields.
g. Leave the Signing Cert Serial Number as the default value, unless there is a third-party certificate being used for the SAML assertion.
If using a third-party certificate, then click Select Certificate and choose the appropriate certificate.
h. Download the Assertion Signing Certificate, which is used later in the "CyberArk configuration steps" section.
 |
i. Save your changes.
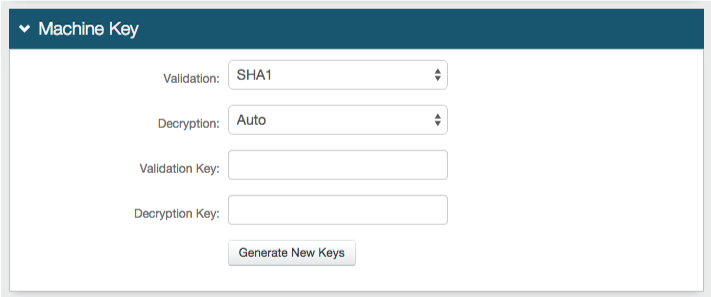
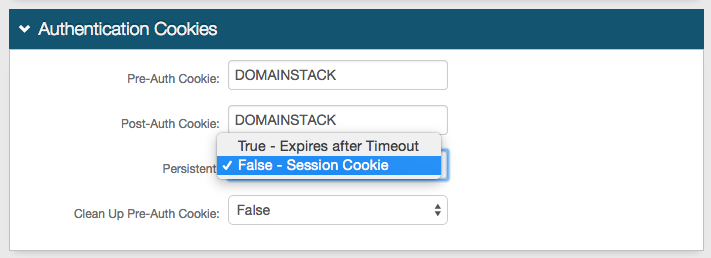
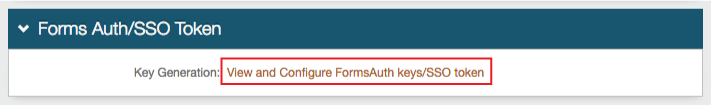
Forms Auth / SSO Token
Optionally, in the Forms Auth / SSO Token section, click the View and Configure FormsAuth keys/SSO token link to configure the token/cookie settings and configure this realm for SSO.
 |
CyberArk configuration steps
1. Log into the CyberArk Password Vault admin console, and open Administration by clicking the wrench icon.
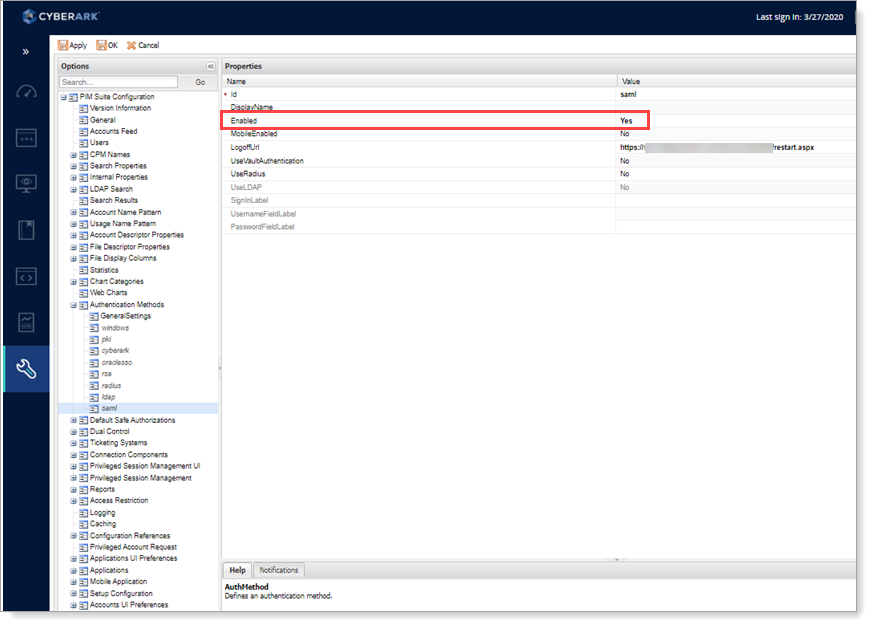
2. Select SAML under Authentication Methods.
3. Enable SAML by setting Enabled to Yes.
4. Set the LogoffURL to any preferred URL, such as the SecureAuth IdP logoff page (https://secureauth.company.com/secureauth2/restart.aspx) or the company homepage.
5. Click Apply.
 |
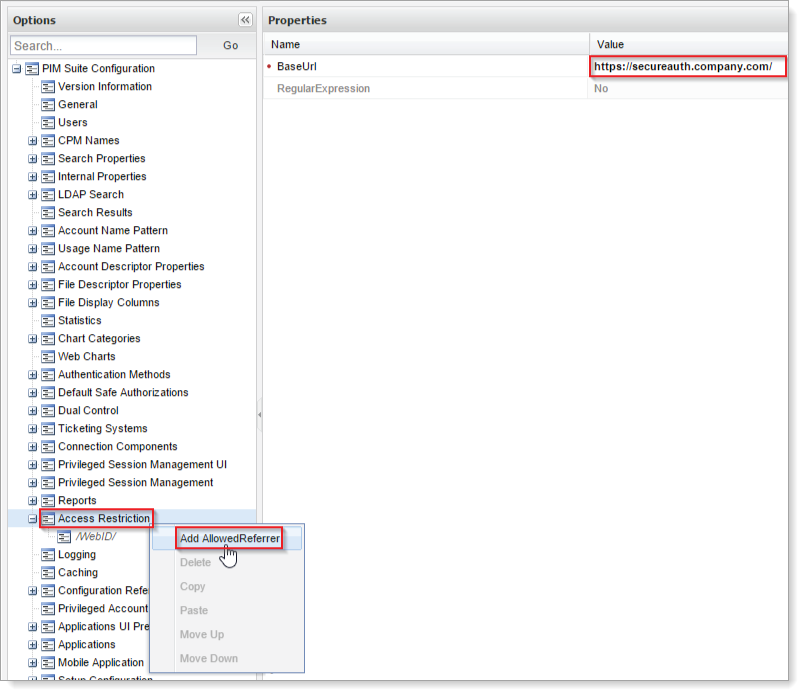
6. Right-click Access Restriction, located in the PIM Suite Configuration folder, and select Add AllowedReferrer.
7. Set the BaseUrl value to the base URL of the IdentityProviderLoginURL.
For example, if the IdentityProviderLoginURL is https://secureauth.company.com/secureauth2, then the BaseUrl would be https://secureauth.company.com.
8. Click OK.
 |
9. To configure the SAML settings, stop the Password Vault Web Access by entering iisreset -stop on the command line.
10. Locate the Password Vault Server web.config file at C:\inetpub\wwwroot\PasswordVault, and back up the file.
11. Set the CyberArk web.config SAML configuration values.
Open the web.config file (located in C:\inetpub\wwwroot\PasswordVault), and add the following three keys to the <appSettings> section of the file:
<add key="IdentityProviderLoginURL" value="https://secureauth.company.com/SecureAuth1" /> <add key="IdentityProviderCertificate" value="<FULL CERT VALUE>" /> <add key="Issuer" value="UniqueName" />
Replace https://secureauth.company.com/SecureAuth1 with the actual Fully Qualified Domain Name (FQDN) of the SecureAuth IdP appliance, and the CyberArk-integrated realm name.
Replace <FULL CERT VALUE> with the actual certificate value from the Assertion Signing Certificate in the SecureAuth IdP Web Admin (step 14).
Replace UniqueName with the actual WSFed/SAML Issuer value set in the Web Admin (step 7).
Warning
The certificate value must be in base64 format and pasted as a single line.
12. Save the web.config file.
13. Start the Password Vault Web Access by entering iisreset -start on the command line.